Storage method, system and device
A technology that has stored and stored keys, applied in memory systems, transmission systems, digital transmission systems, etc., to solve the problem of inability to increase access rights to data files to another user
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] In order to make the object, technical solution, and advantages of the present invention clearer, the present invention will be further described in detail below with reference to the accompanying drawings and examples.
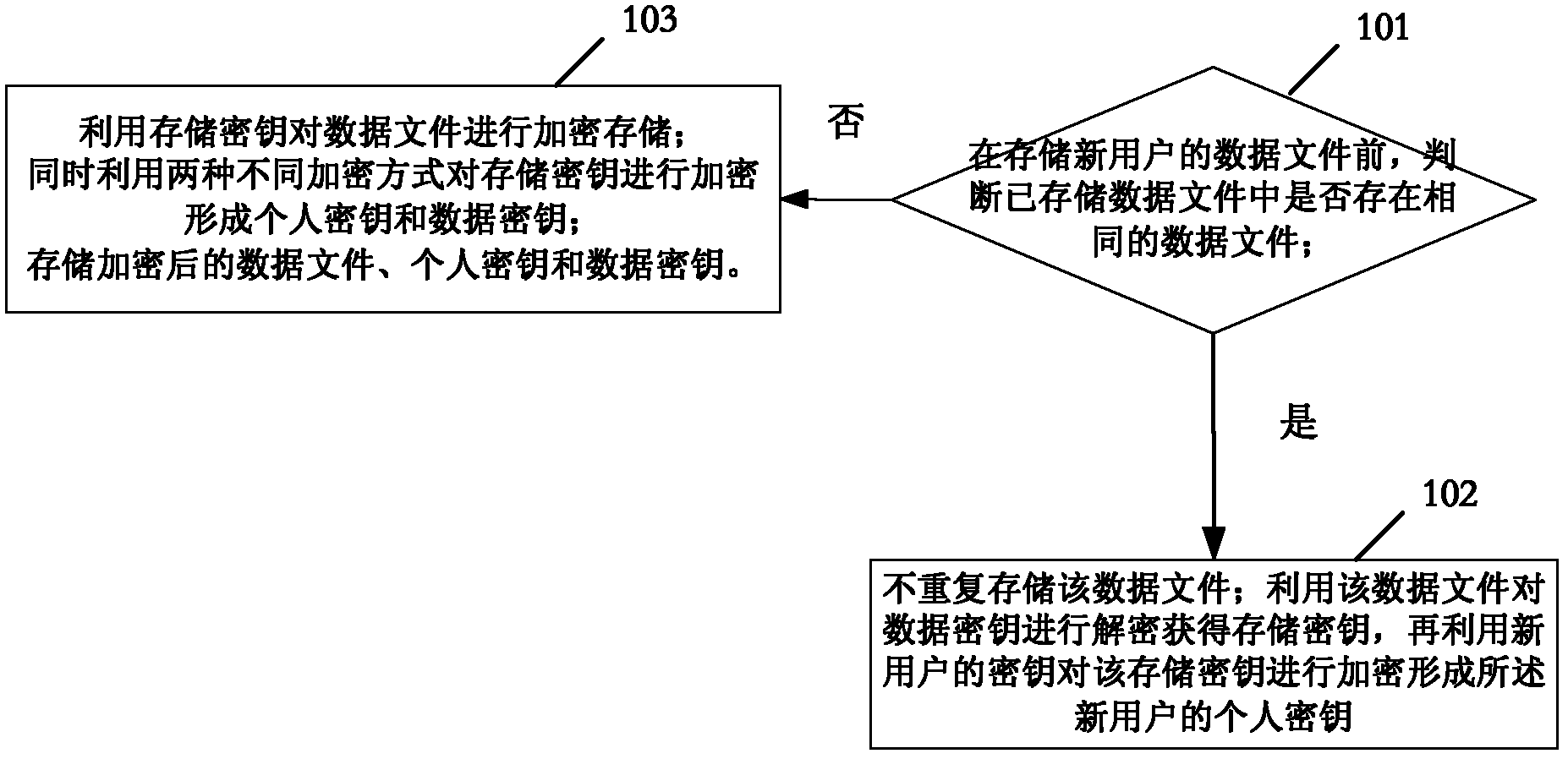
[0031] figure 1 It is a flowchart of a storage method provided by an embodiment of the present invention. In this embodiment, the data file is encrypted and stored using the storage key; at the same time, two different encryption methods are used to encrypt the storage key to form a personal key (personal key) and a data key (data key); The key of the user to whom the data file belongs is the decryption key, and the storage key can be obtained after decrypting the personal key; the storage key can be obtained after decrypting the data key with the data file before encryption as the decryption key; data files, personal keys, and data keys. The method also includes:
[0032] Step 101: Before storing the data file of the new user, judge whether there i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More