Access control method
A technology of access control and control instructions, applied in the field of information security, can solve problems such as low protection rate, affect protection efficiency, and protection lag, and achieve the effect of avoiding security risks, improving protection efficiency, and ensuring security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
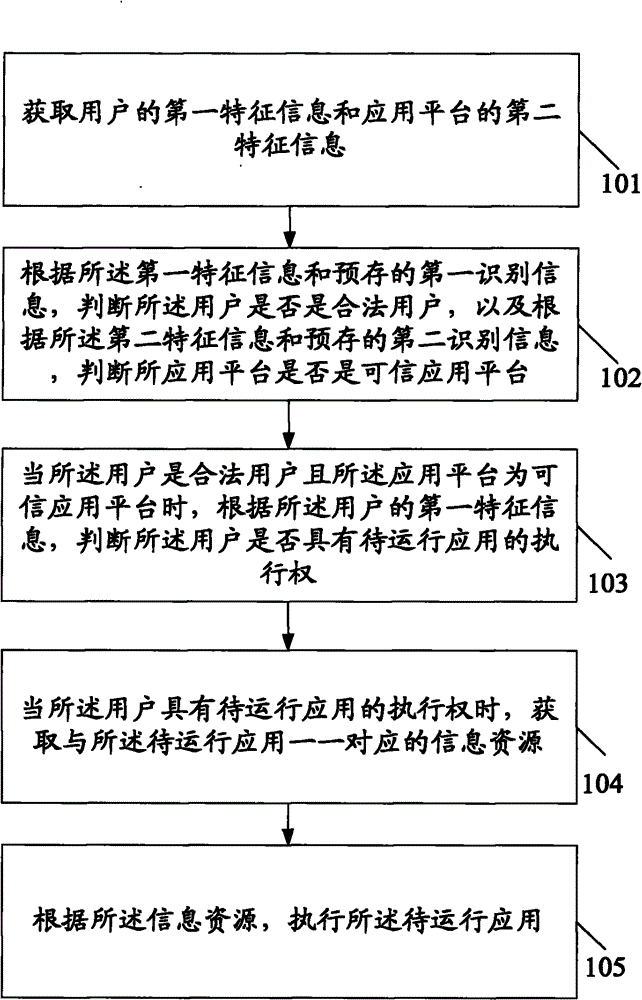
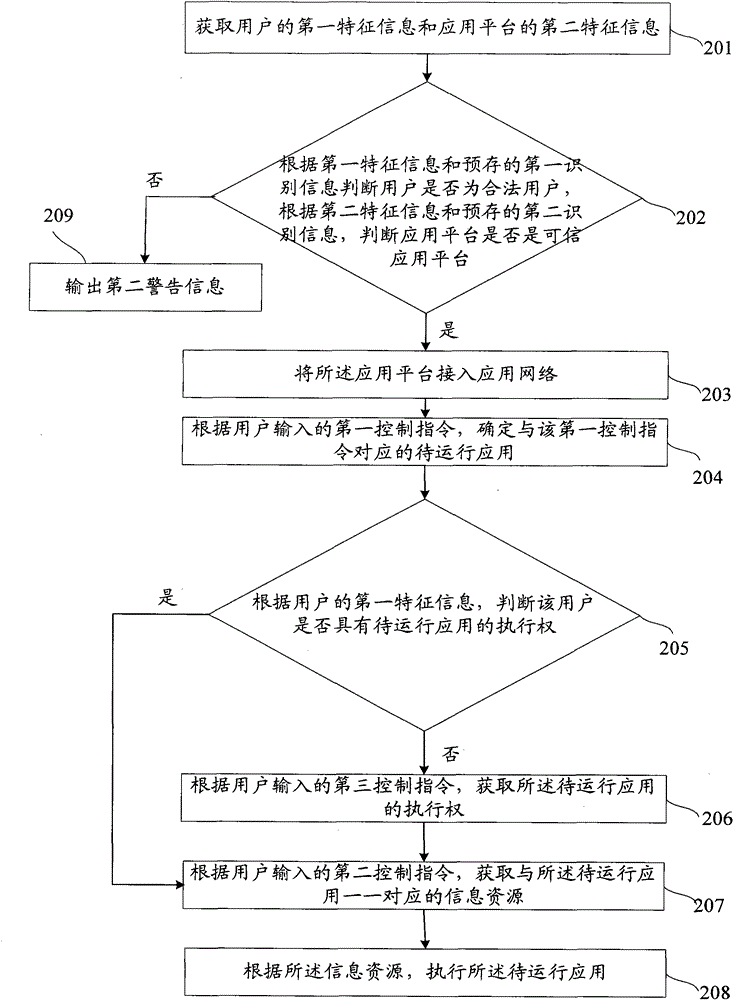
[0036] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0037] The embodiment of the present invention discloses an access control method. By acquiring the first feature information of the user and the second feature information of the application platform, and according to the first feature information and the pre-stored first identification information, it is judged whether the user is a legitimate user, And according to the second feature information and the pre-stored second identification information, it is jud...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More