Trusted and secure wifi router and data processing method thereof
A security data and router technology, applied in the field of communication security, can solve problems such as network session hijacking, theft, stealing user information, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
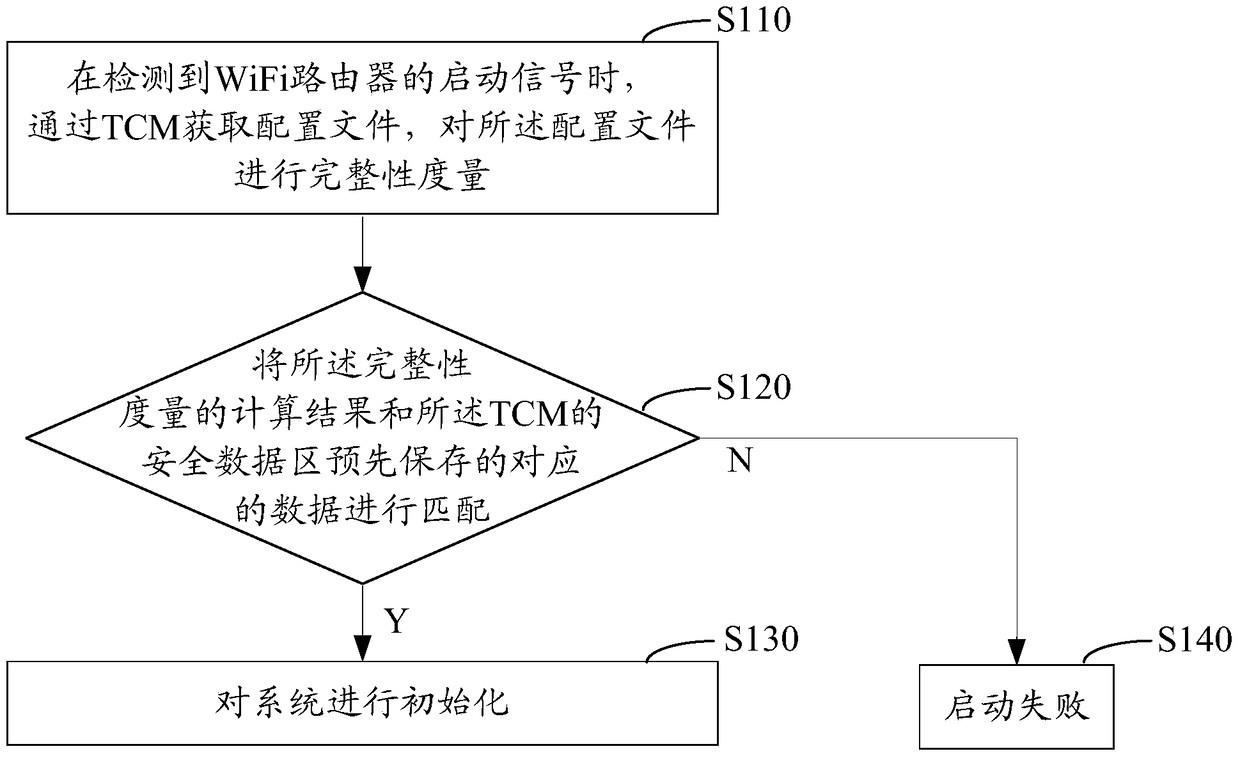
[0041] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0042] TCM (Trusted Cryptography Module, Trusted Cryptography Module) is a hardware module of a trusted computing platform, which provides identity and cryptographic computing functions for the trusted computing platform, and has a protected storage space. TCM adopts domestic encryption algorithms, and the involved cryptographic algorithms include: SM2 elliptic curve cryptographic algorithm, SMS4 symmetric cryptographic algorithm, SM3 cryptographic hash algorithm, HMAC message authentication code algorithm, and random number generator. TCM is a collection of hardware and firmware, which can be pack...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More