Fingerprint and Voiceprint Dual Authentication Method
A dual-authentication and fingerprint technology, applied in the field of computer authentication services, can solve problems such as identity authentication correctness and security impact, application limitations of fingerprint recognition technology, intrusion recognition is not very good, etc., to solve insecure problems, security and the effect of improved reliability and accurate two-factor authentication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
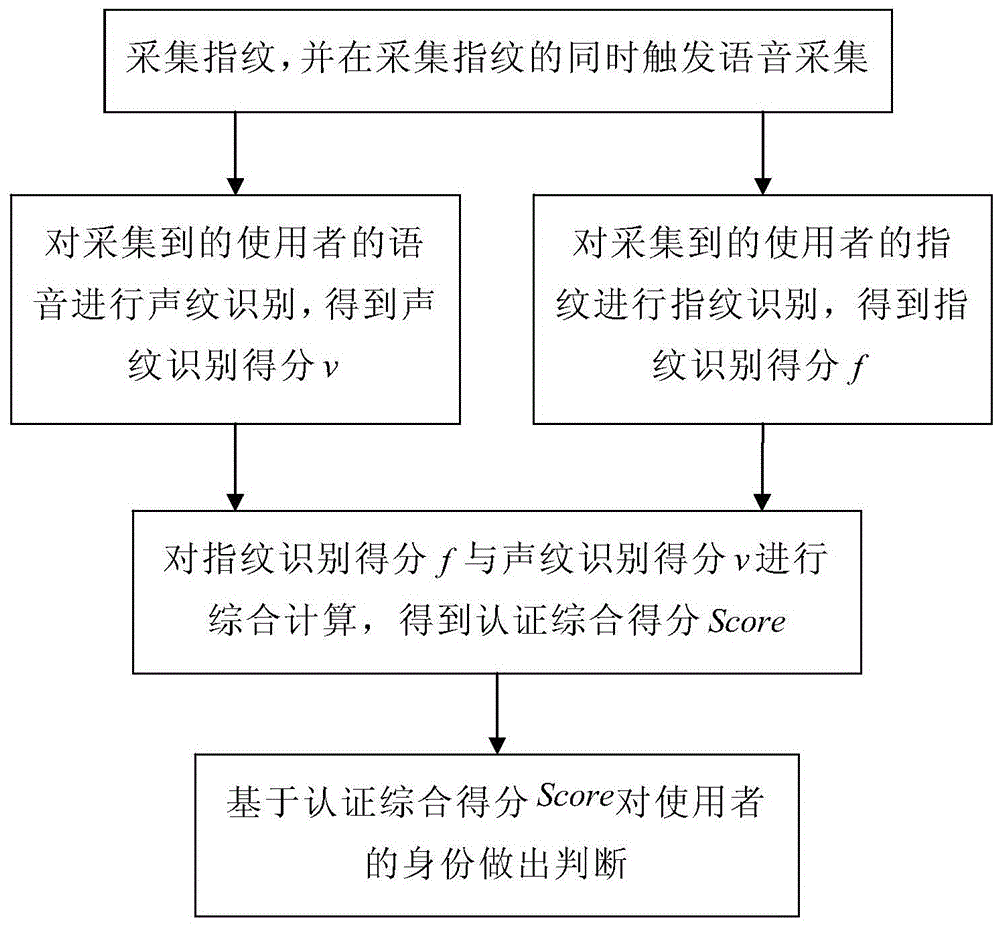
[0028] like figure 1 As shown, the fingerprint and voiceprint double authentication method of the present invention comprises the following steps:
[0029] 1) Collect fingerprints, and trigger voice collection while collecting fingerprints;
[0030] 2) Perform fingerprint recognition on the collected user fingerprints to obtain a fingerprint recognition score f, and simultaneously perform voiceprint recognition on the collected user voice to obtain a voiceprint recognition score v;
[0031] 3) Comprehensively calculate the fingerprint recognition score f and the voiceprint recognition score v to obtain the authentication comprehensive score Score as an identity judgment;
[0032] 4) Make a judgment on the identity of the user based on the comprehensive score of the authentication score: if the Score is greater than or equal to the set threshold, it is considered that both the fingerprint and the voiceprint come from the claimed user, and the authentication is passed; if the S...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More