Identity-based encryption method allowing revocation at lattice
An encryption method and identity technology, applied in the field of information security, can solve problems such as difficulty in resisting quantum attacks and leakage of user private keys
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0053] The present invention will be described in detail below in combination with specific embodiments.
[0054] The reversible identity-based encryption method of the present invention is specifically implemented according to the following steps:
[0055] Step 1. System establishment:
[0056] Specifically follow the steps below:
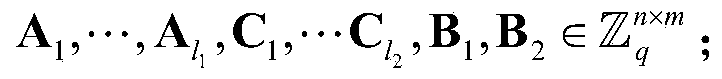
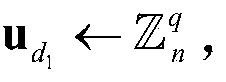
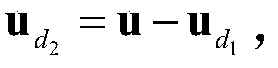
[0057] Step (1.1), input security parameter λ, and the maximum number N of users, setting parameter m=2n log q, σ = m a x ( l 1 , l 2 ) m ω ( log m ) , α 1 5 ( 1 + ω ( log m ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More