Verification code inputting method and device
An input method and verification code technology, applied in the field of terminal and security verification, can solve problems such as user memory error, verification failure, and cumbersomeness, and achieve the effect of improving input efficiency and accuracy and avoiding user operations.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0014] The application will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain related inventions, rather than to limit the invention. It should also be noted that, for the convenience of description, only the parts related to the related invention are shown in the drawings.
[0015] It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other. The present application will be described in detail below with reference to the accompanying drawings and embodiments.
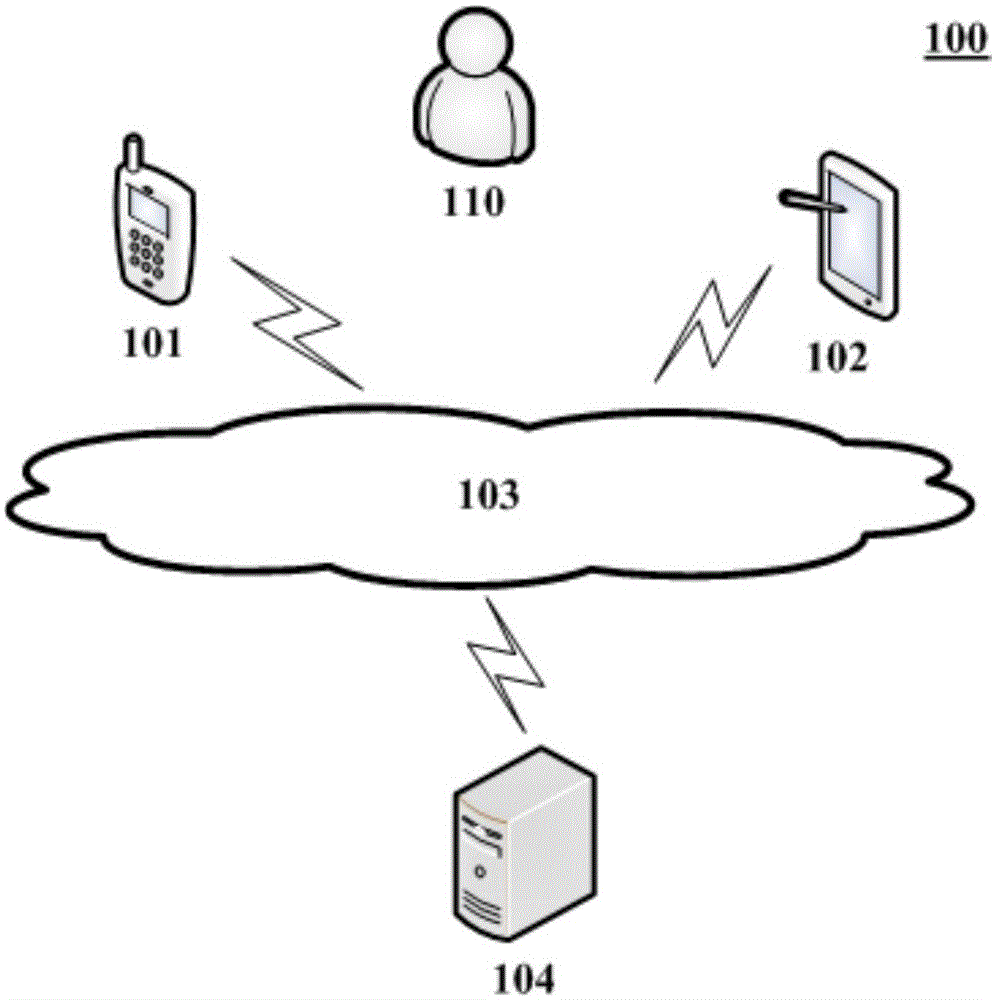
[0016] figure 1 An exemplary system architecture 100 to which embodiments of the present application may be applied is shown.
[0017] like figure 1 As shown, the system architecture 100 may include terminal devices 101 , 102 , a network 103 and a server 104 . The network...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More