A Dynamic Probabilistic and Space-Frequency Domain Composite Image Selective Encryption and Decryption Method
An encryption method and selective technology, applied in image data processing, image data processing, instruments, etc., can solve problems such as spatial pixel overflow, encryption strategy irrelevant to the image to be encrypted, and loose coupling
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0158] The present invention is described below in conjunction with specific embodiment:
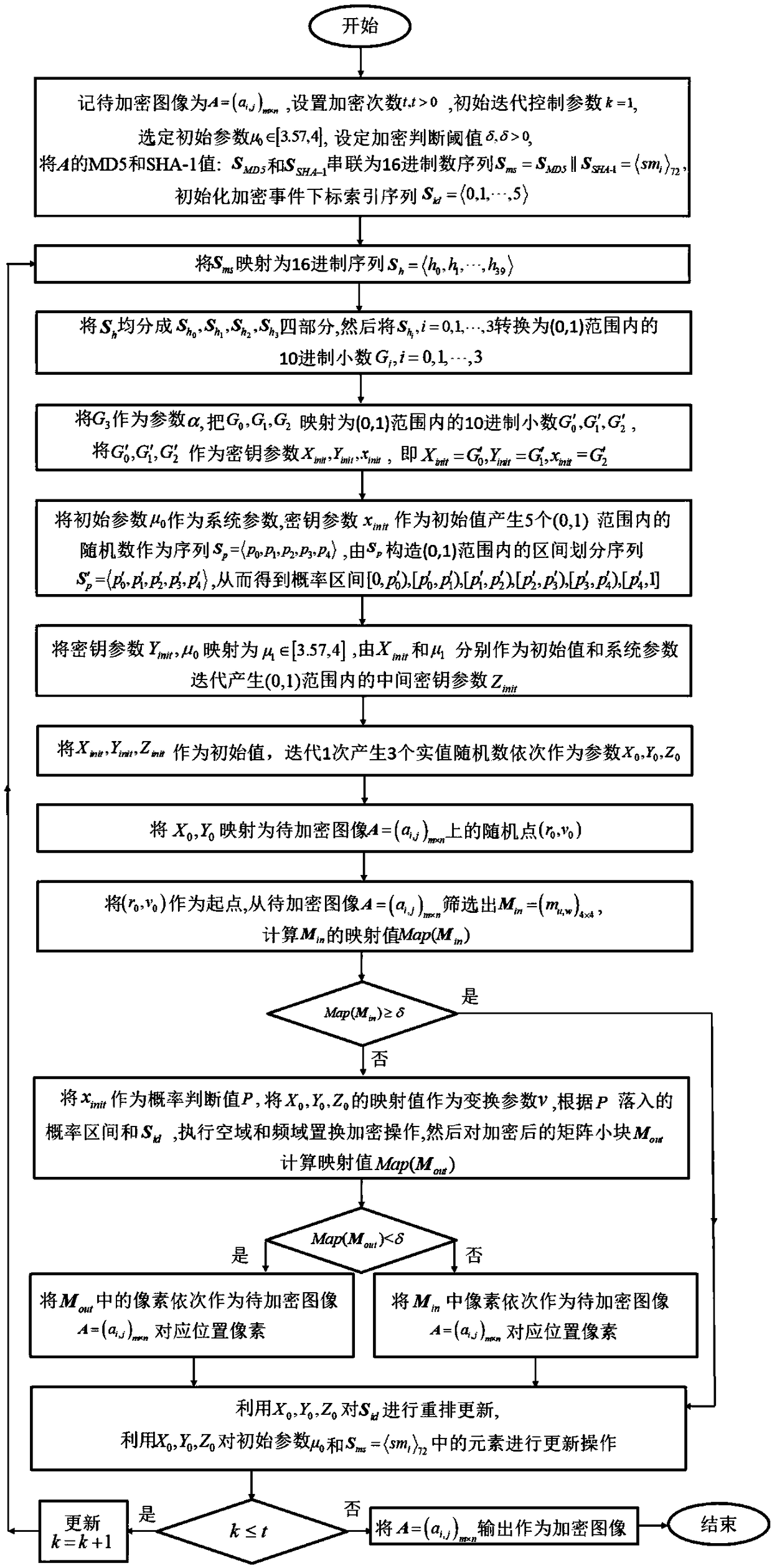
[0159]Taking JAVA jdk1.8.0_20 as the implementation environment of the case, the implementation mode of the present invention will be described in detail in conjunction with the accompanying drawings, but not limited to this implementation case, where figure 1 is the encryption flow chart, figure 2 is the decryption flow chart;
[0160] The encryption process is as follows:
[0161] Step 1: Select image A such as image 3 As shown, it is a grayscale image face of 256×256, and the image to be encrypted is A=(a i,j ) m×n ,i=0,1,...,m-1, j=0,1,...,n-1 corresponding to the 40-bit hexadecimal MD5 value S MD5 =, SHA-1 value
[0162] S SHA-1 =, will S MD5 and S SHA-1 Concatenated into a hexadecimal sequence S ms = S MD5 ||S SHA-1 =i > 72 ,i=0,1,...,71 and initialize the encrypted event subscript index sequence S id for S id =, set encryption times t=10000, initial iteration cont...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More