User data access control method, device and system
A data access and user data technology, applied in the Internet field, can solve problems such as poor data security of data sources and poor account security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0040] According to the embodiment of the present application, a method embodiment of a user data access control method is also provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be implemented in a computer system such as a set of computer-executable instructions and, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
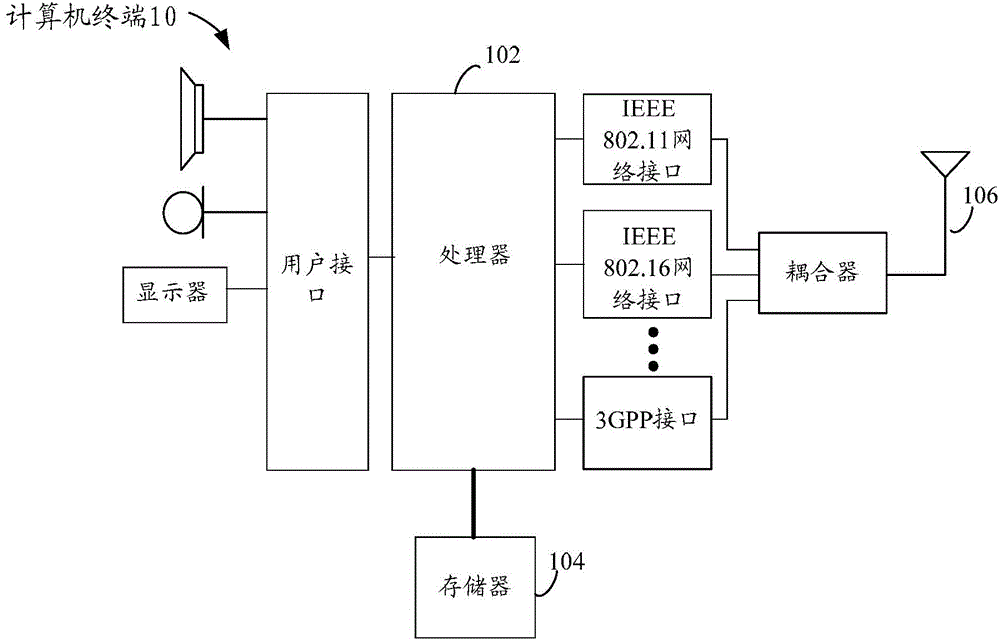
[0041] The method embodiment provided in Embodiment 1 of the present application may be executed in a mobile terminal, a computer terminal, or a similar computing device. Take running on a computer terminal as an example, figure 1 It is a block diagram of the hardware structure of a computer terminal according to a user data access control method according to an embodiment of the present application. Such as figure 1 As shown, the computer terminal 10 may include one or more (only one is sh...
Embodiment 2
[0178] According to the embodiment of the present application, a method embodiment of a user data access control method is also provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be implemented in a computer system such as a set of computer-executable instructions and, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
[0179] The method embodiment provided in Embodiment 2 of the present application can still be executed in a mobile terminal, a computer terminal or a similar computing device. It should be noted here that the method embodiment provided in Embodiment 2 can still run on figure 1 on the computer terminal shown.
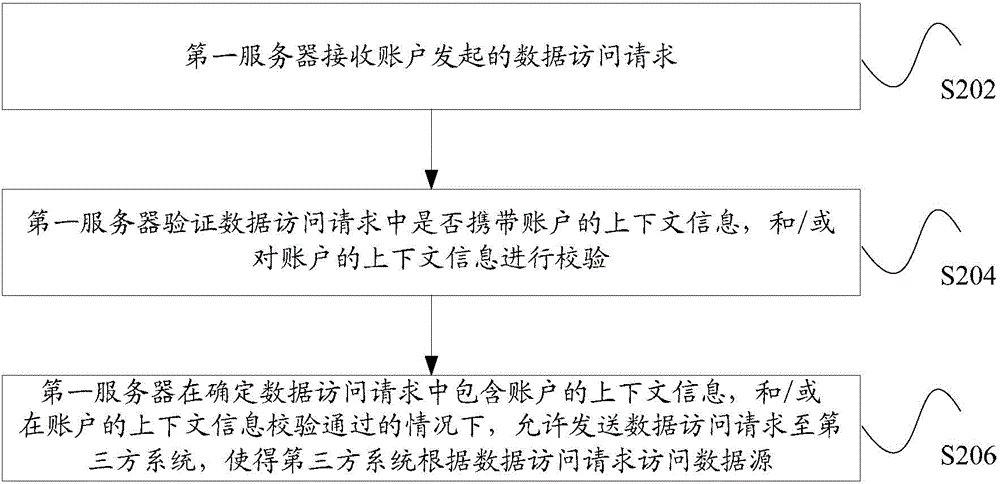
[0180] Based on the above operating environment, this application can also provide such Figure 7 Access control methods for user data shown. Figure 7 It is a schematic flowchart of...
Embodiment 3
[0228] According to the embodiment of the present application, a method embodiment of a user data access control method is also provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be implemented in a computer system such as a set of computer-executable instructions and, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
[0229] The method embodiment provided in Embodiment 3 of the present application can still be executed in a mobile terminal, a computer terminal or a similar computing device. It should be noted here that the method embodiment provided in Embodiment 3 can still run on figure 1 on the computer terminal shown.
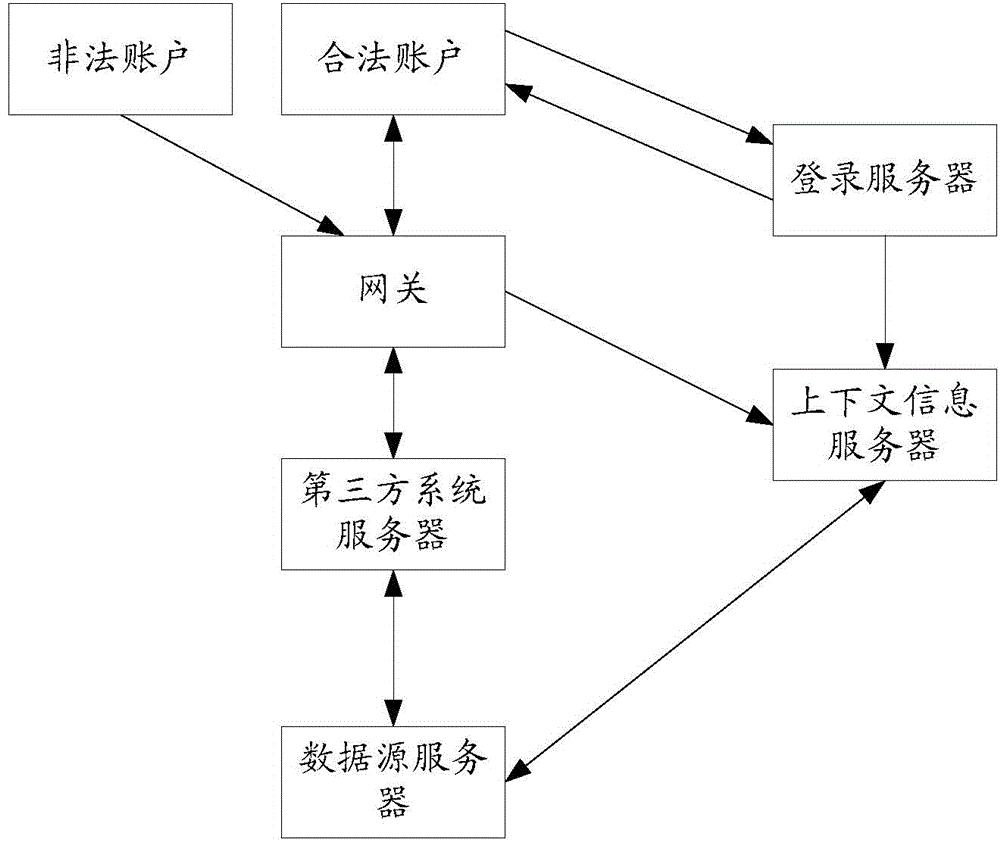
[0230] Based on the above operating environment, this application can also provide such Figure 8 Access control methods for user data shown. Figure 8 It is a schematic flowchart of...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com