A kind of access control list setting method and system
A technology of access control list and access list, which is applied in the direction of transmission system, computer security device, instrument, etc., can solve the problem of taking a long time, and achieve the effect of increasing the setting speed and reducing the time
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0048] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
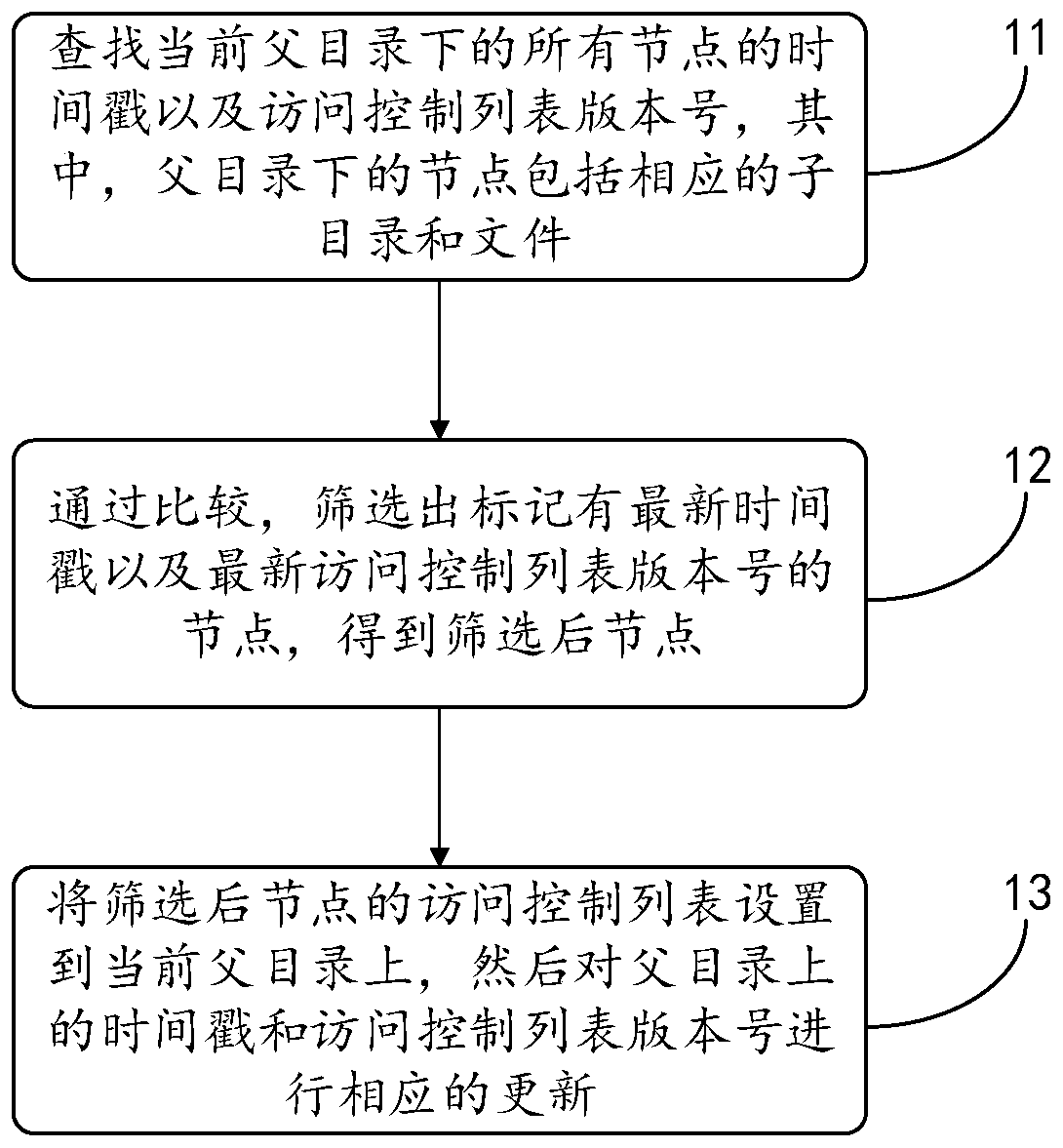
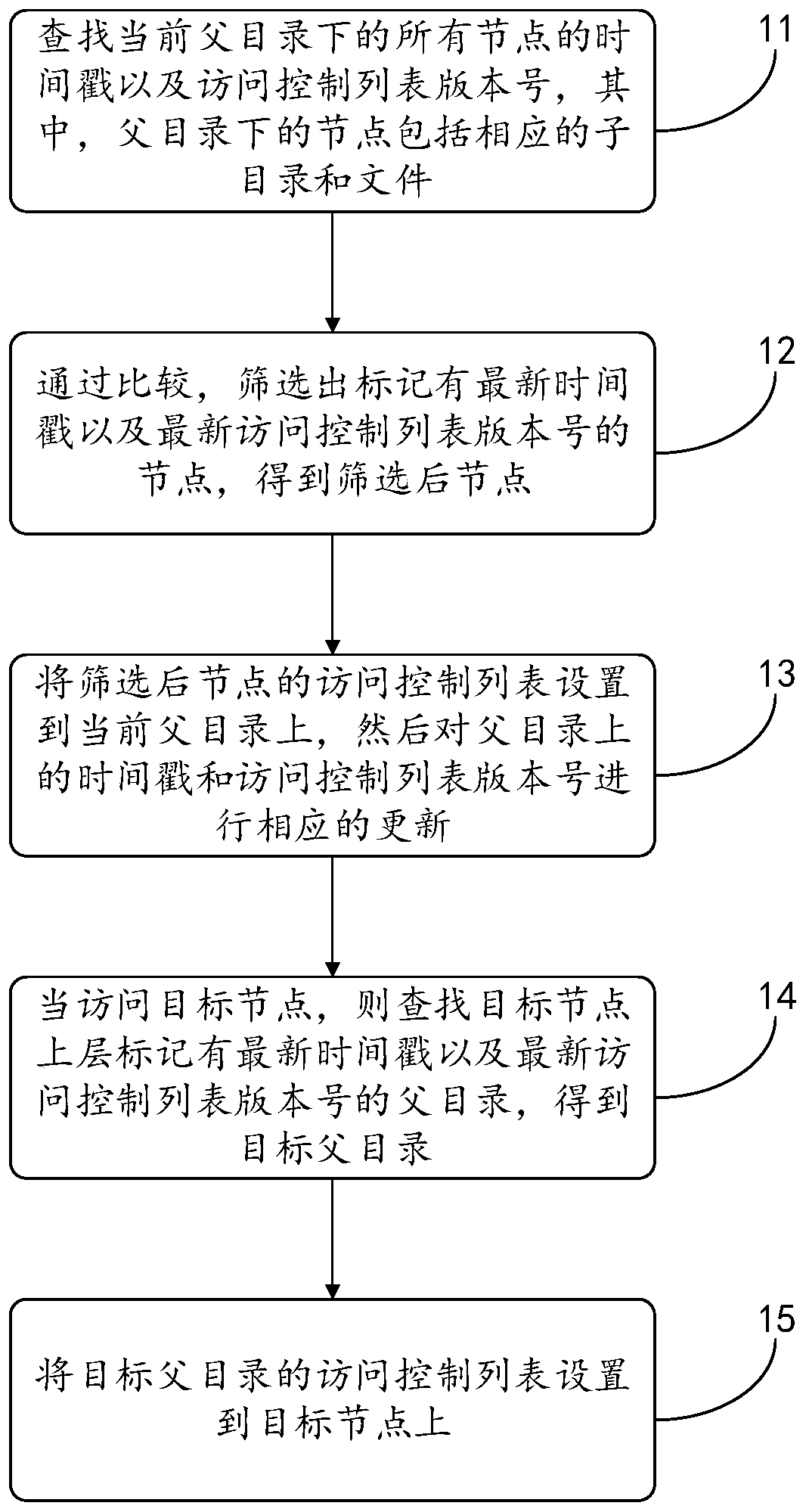
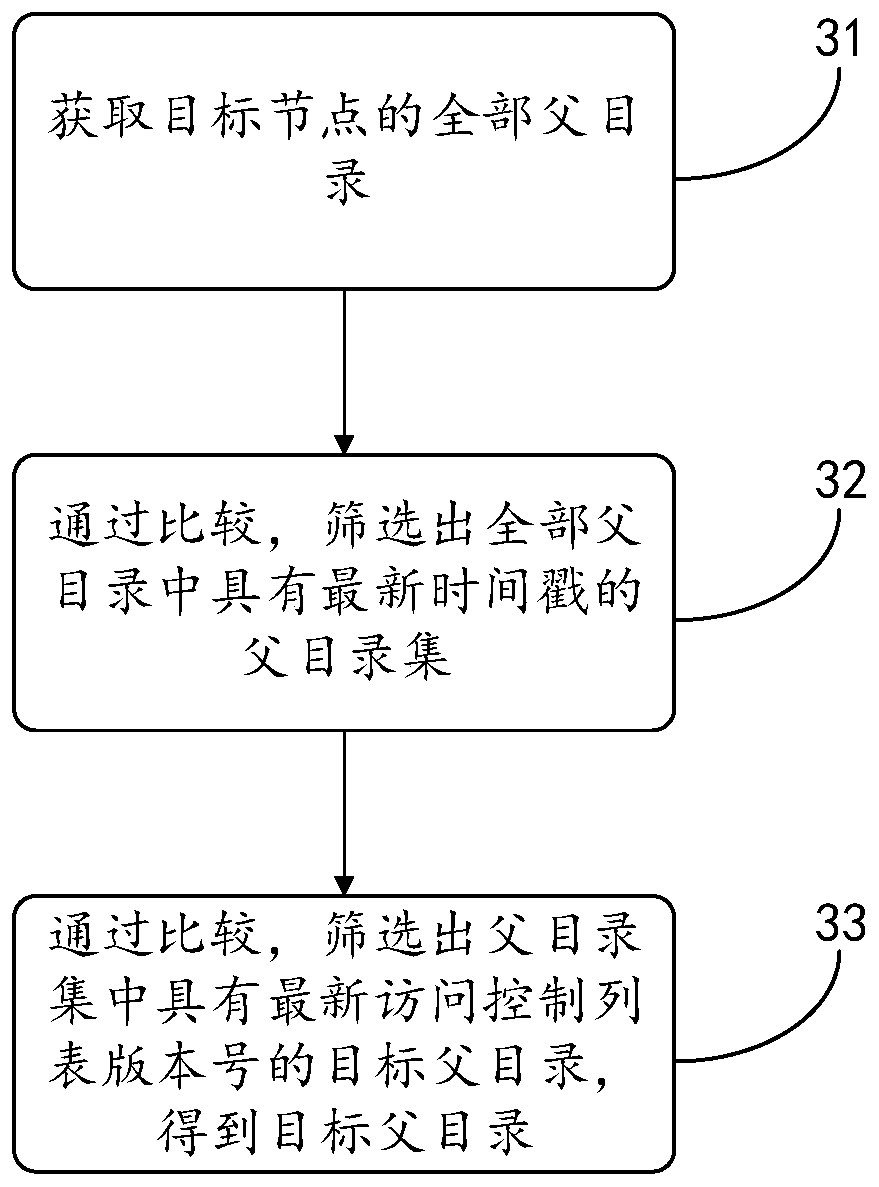
[0049] The embodiment of the present invention discloses an access control list setting method, see figure 1 As shown, the method includes:
[0050] Step 11: Find the time stamps and ACL version numbers of all nodes under the current parent directory, where the nodes under the parent directory include corresponding subdirectories and files.
[0051] In the embodiment of the present application, the above-mentioned parent directory may be a large directory con...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More