Crash data monitoring method and apparatus
A data monitoring and data technology, applied in the computer field, can solve the problem that the module cannot be directly reflected, the client crash data statistical monitoring granularity is limited to the number of crashes and the crash rate, etc., to achieve the effect of improving monitoring accuracy and improving analysis efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
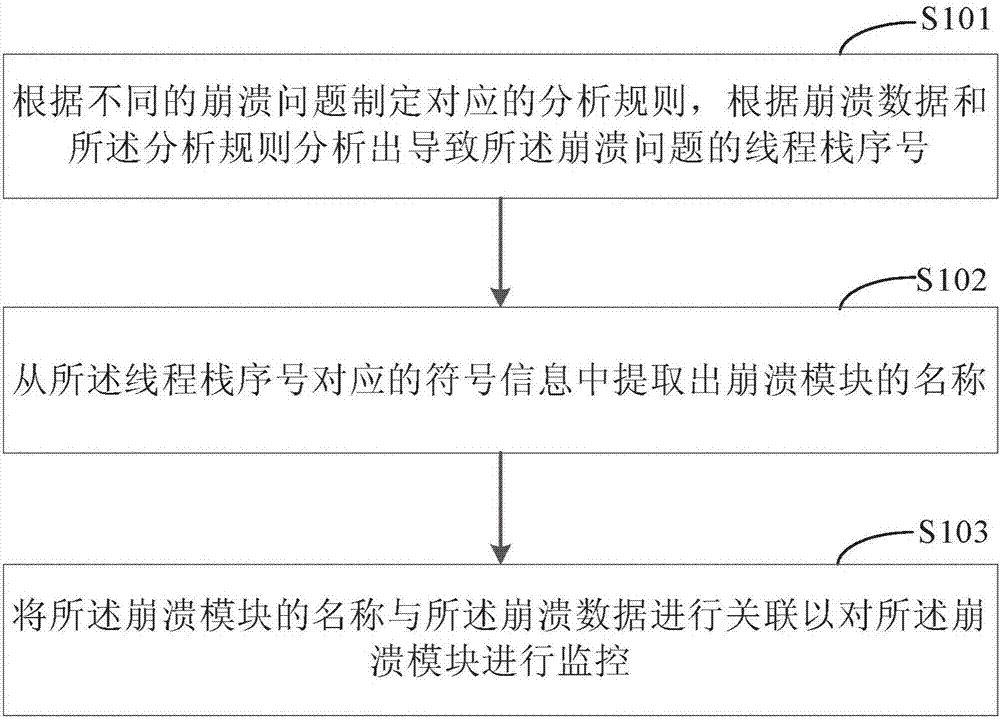
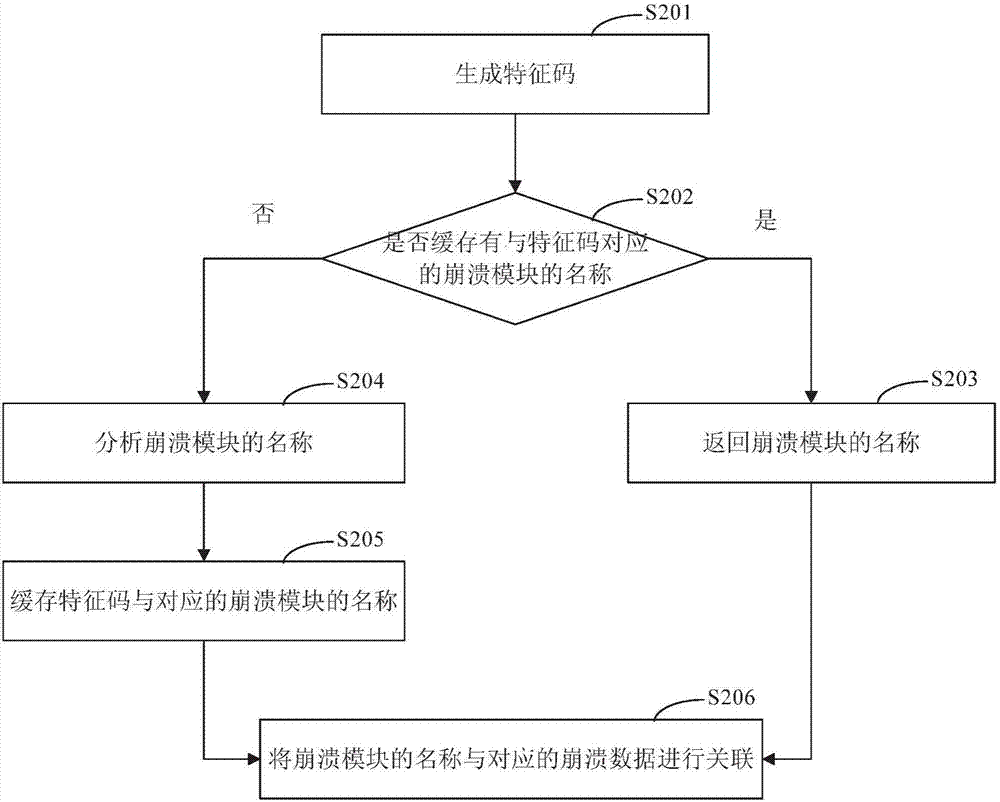
Method used
Image
Examples
Embodiment 1
[0052] Example 1: When the user clicks on the login in the application, he needs to enter the account number and password to log in. Assuming that the user does not enter a password, and the application does not check whether the password is empty, the operation of the empty string in the logic processing will cause the application to collapse. Then, for this crash problem, on the same platform, the virtual memory offset in the crash data generated by different devices is unchanged. For the crash problem caused by this specific scenario in different devices on the same platform, the signature generated by the virtual memory offset can identify the crash problem in this specific scenario (enter from the login entry, the password is empty).
Embodiment 2
[0053] Embodiment 2: Assume that when a user searches for a product, due to a code logic defect (Bug), when the application calls a method that does not exist, the application will crash. Then, for this crash problem, on the same platform, the virtual memory offset in the crash data generated by different devices is unchanged. For the crash problem caused by this specific scenario in different devices on the same platform, the signature generated by the virtual memory offset can identify the crash in this specific scenario (entering from the search entry, the code accesses a method that does not exist) question.
[0054] Table 1 shows a piece of crash data on the IOS platform. Taking this piece of crash data as an example, it explains how to generate signatures based on virtual memory offsets. The thread stack information is executed from bottom to top. Corresponding to this embodiment, the execution sequence of the thread stack information is: thread stack 14->thread stack 1...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More