Method and device for identifying malicious resource access
A technology for resource access and resource access request, applied in transmission systems, electrical components, etc., can solve problems such as insufficient protection methods, and achieve the effect of preventing malicious access
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] In order to make the above objects, features and advantages of the present invention more comprehensible, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments.
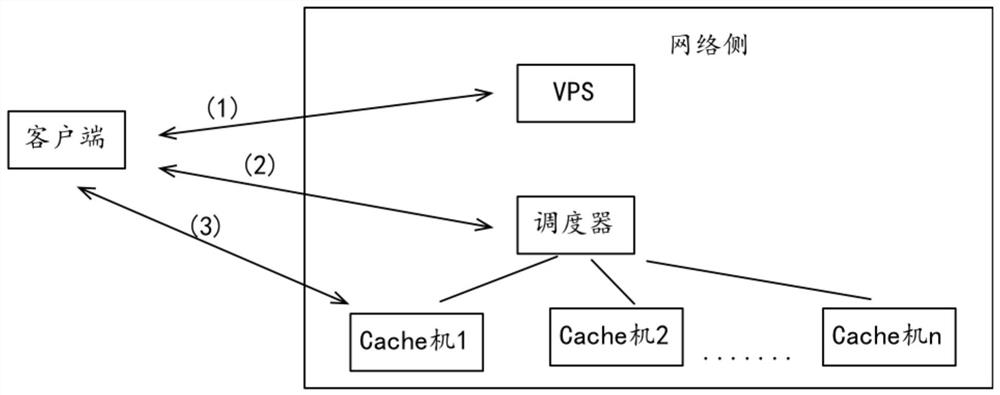
[0048] see figure 1 , is a schematic diagram of resource access control implementation in the prior art.
[0049] Step (1): the client requests the address of the dispatcher to the VPS;
[0050] Step (2): the client accesses the scheduler to obtain the address of the cache machine corresponding to Fragment 1;
[0051] Step (3): the client downloads fragment 1 according to the address of the cache machine corresponding to fragment 1;
[0052] The download of each other segment needs to repeat steps 2-3.
[0053]Wherein, in step 1, what the client requests from the VPS is the address of the scheduler; and then in step 2, according to the address of the scheduler, the client accesses the scheduler to obtain the address of the cach...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More