An access control method for smart home environment based on private chain
A smart home and access control technology, applied in the field of information security, can solve the problems of denial, deception of smart home owners, and the owner's unwillingness to pay for services.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
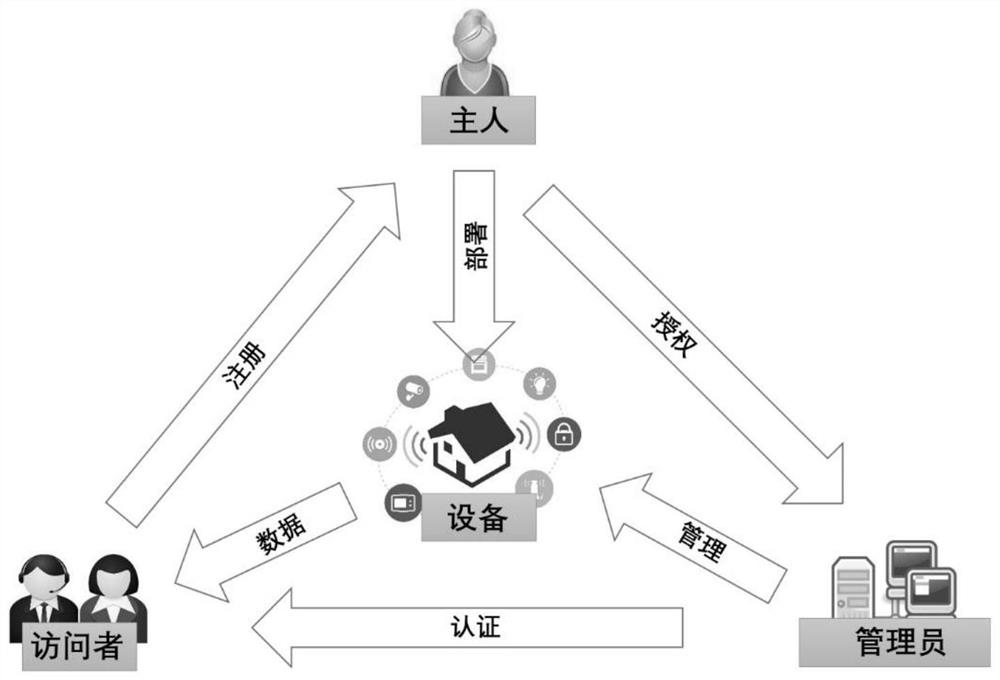
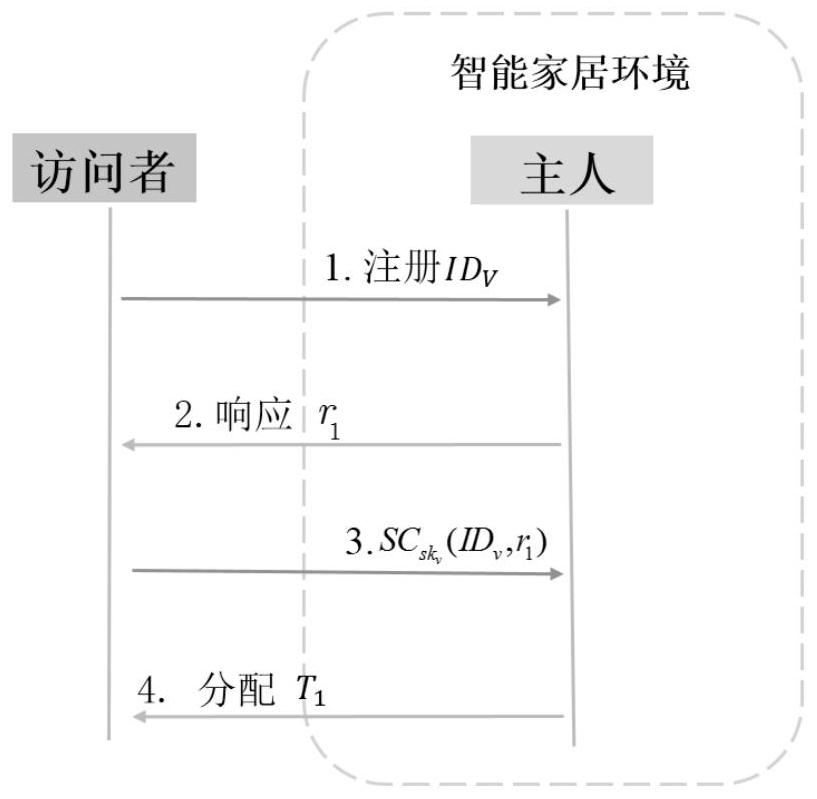
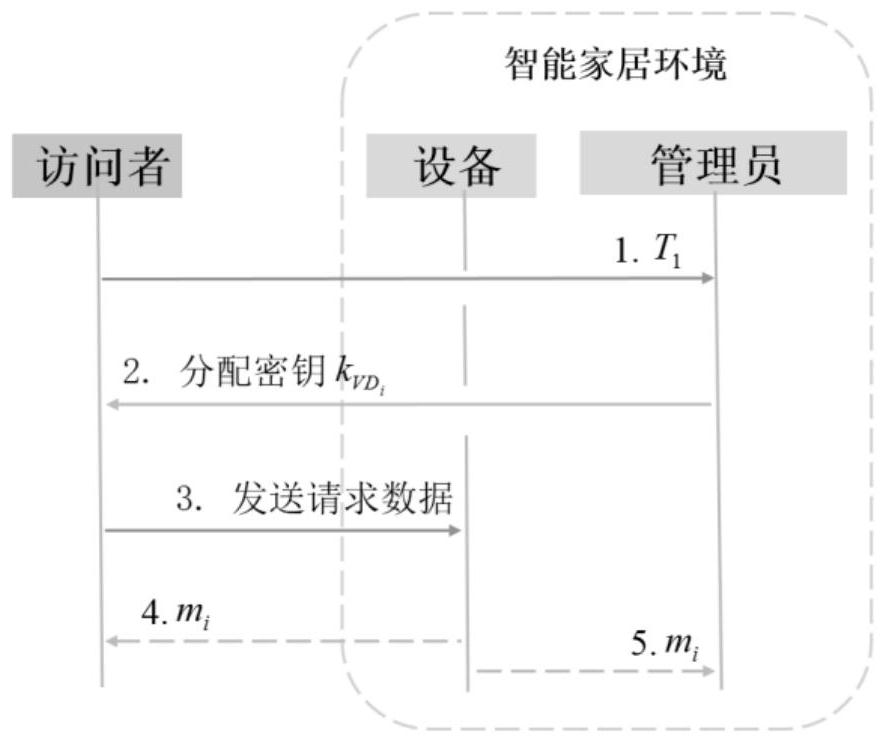
[0031] This embodiment provides an access control method for a smart home environment based on a private chain. The flow chart of access control for a smart home environment based on a private chain is as follows: figure 1 shown, including:
[0032] Initialization: First the smart home master for smart home manager Assign identity information and keys, and assign identity information to smart devices; then the owner writes the policy header into the first block of the private chain; finally, the smart home administrator communicates with the smart device and the smart home owner respectively. share different symmetric keys;
[0033] The specific method of initialization is:
[0034] The initialization algorithm selects a group G of prime order p 1 , a hash function H: {0, 1}*→Z p , a symmetric encryption algorithm E k′ (m) and a signcryption a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More