Protection setting and key safety measures checking method based on 61850 client
A technology for protecting fixed value and customer end, applied in the direction of emergency protection circuit devices, electrical components, information technology support systems, etc., to avoid the risk of false tripping of primary equipment or malfunction of operating protection devices
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
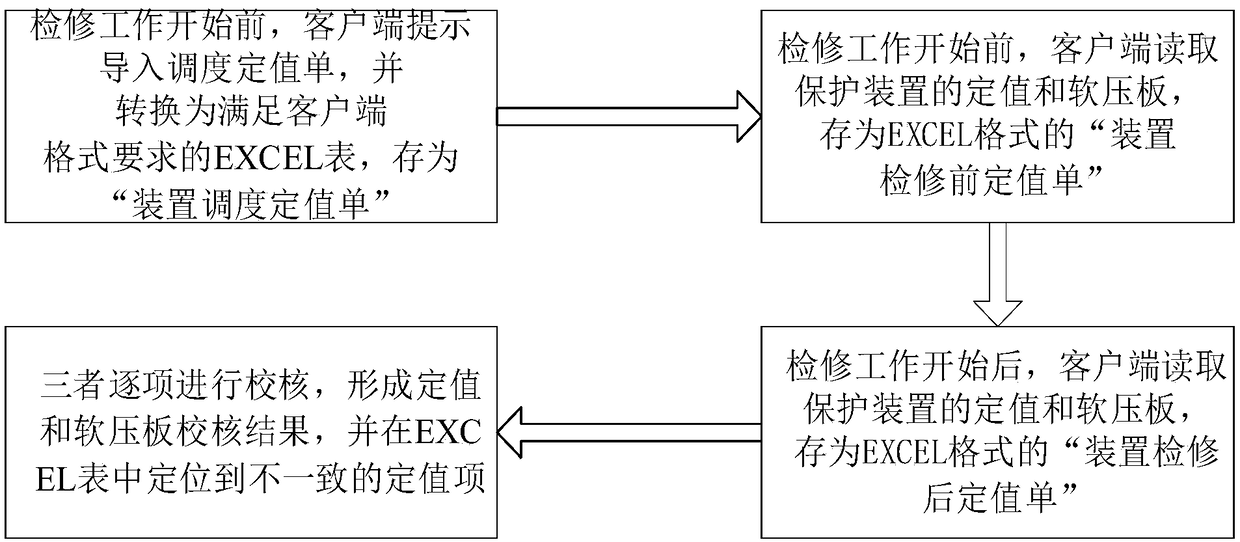
[0027] Such as Figure 1 to Figure 2 As shown, based on the 61850 client’s protection setting and key security check method, the following steps are performed in sequence:
[0028] A. Convert the imported scheduling formal value sheet to the value sheet in EXCEL format through the 61850 client;
[0029] B. Through the 61850 client terminal, read the internal fixed value and soft pressure plate of the protective device, and form the fixed value list in EXCEL format before and after the maintenance of the protective device;
[0030] C. Through the 61850 client terminal, compare the above-mentioned fixed value sheets in EXCEL format, and check whether the fixed values in the above three fixed value sheets are consistent with the soft platen;
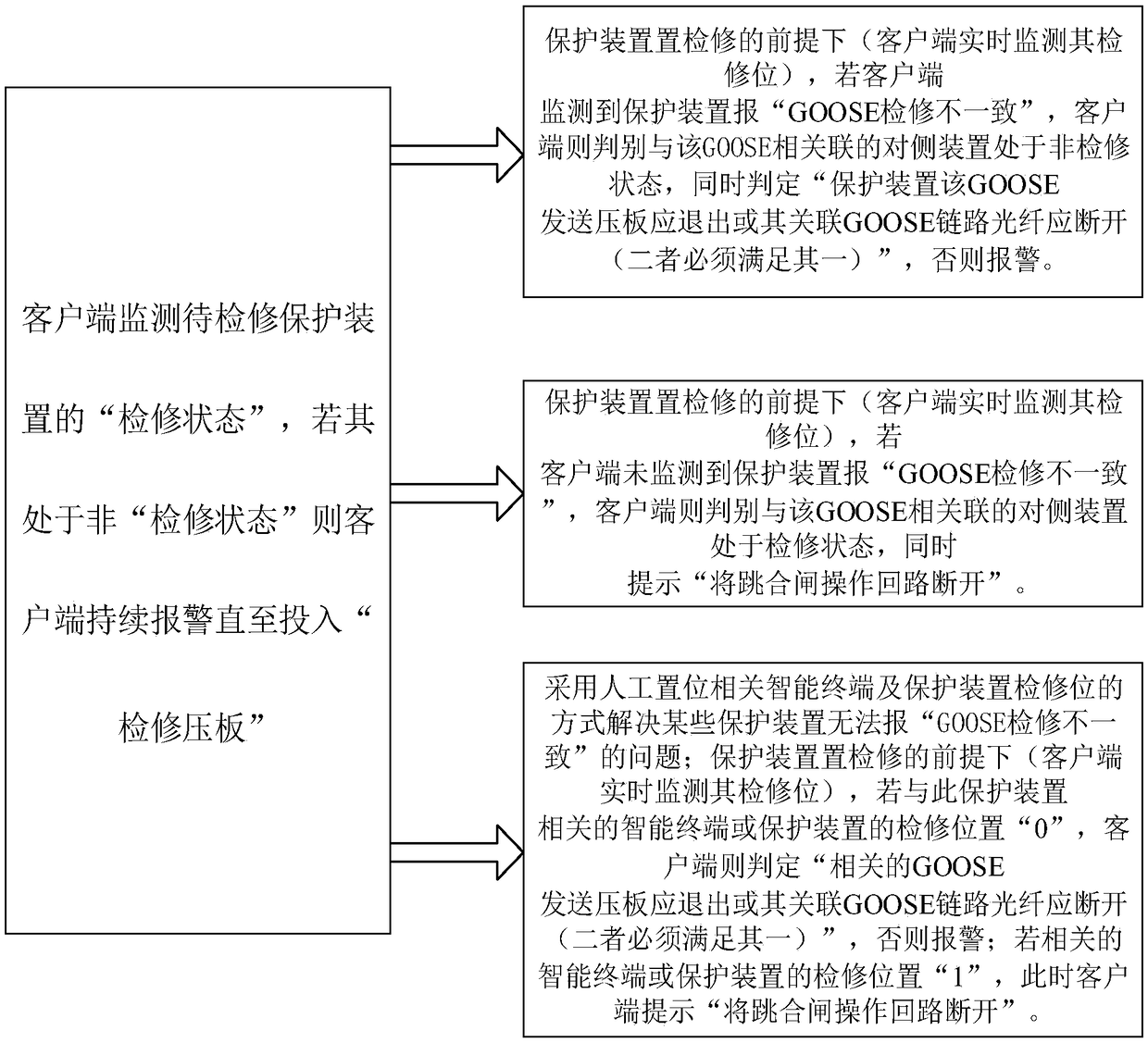
[0031] D. Monitor the "overhaul status" of the protection device to be repaired through the 61850 client, and at the same time monitor the "GOOSE inspection inconsistent" alarm signal of the protection device to be repaired, and realize ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More