Encryption system and method for networked labor transaction system
A transaction system and encryption system technology, which is applied to the encryption system and field of networked labor service transaction systems, can solve the problems of information leakage, information transmission security cannot be guaranteed, and single encryption method, so as to expand the scale of information and reduce the The cost of information integration and the effect of ensuring basic security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
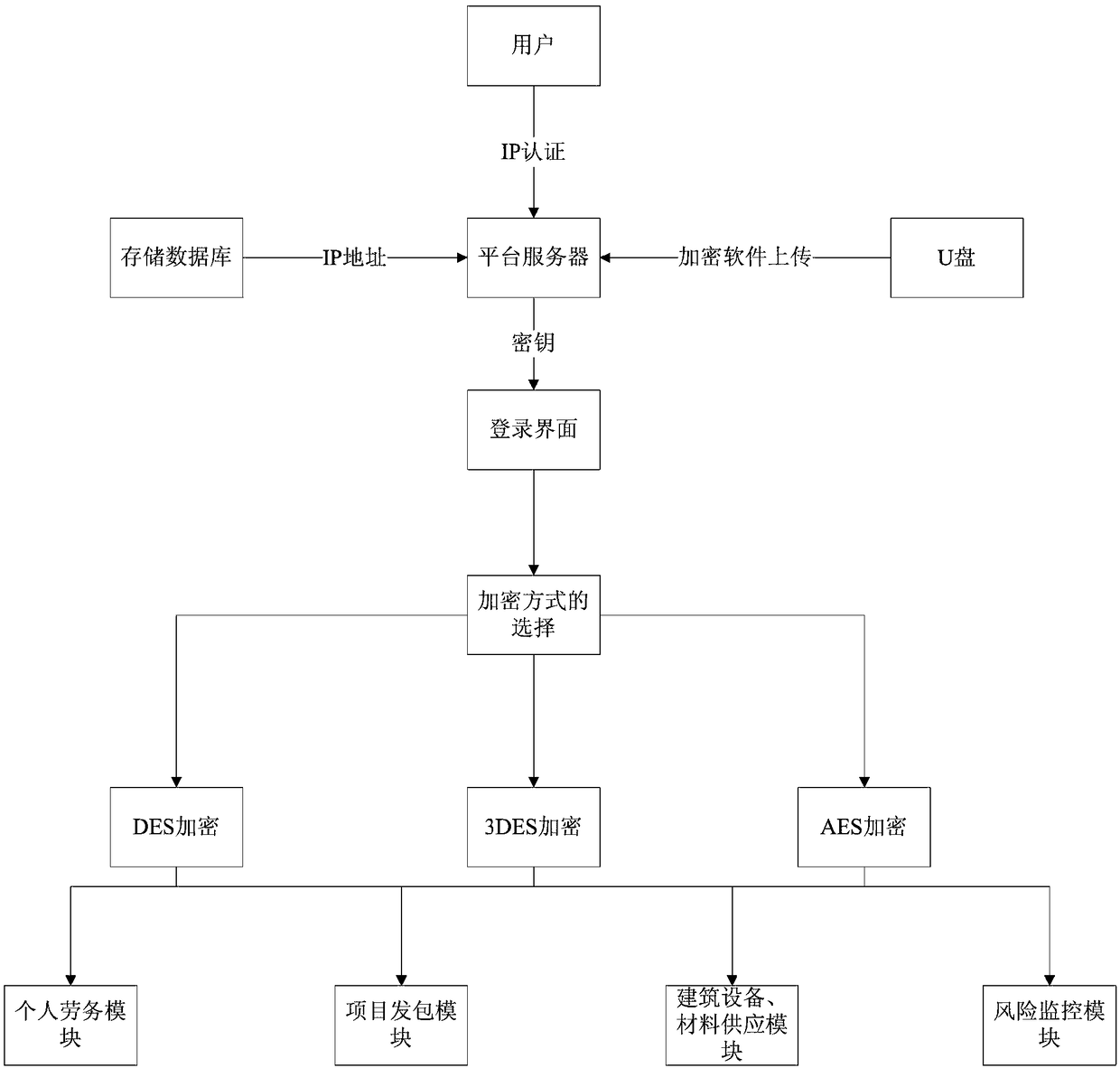
[0027] Such as figure 1 As shown, the present invention is an encryption system and method for a networked labor transaction system, an encryption system for a networked labor transaction system, including initial detection of users entering the platform server in the platform server, storage in the platform server The IP address for user authentication is stored in the database. When the platform server performs initialization detection, it will perform user IP authentication. After the login IP is consistent with the stored database, the platform server will display the login interface. After the user enters the correct key, it will enter the platform server. The personal labor service module, project contracting module, construction equipment and material supply module, and risk monitoring module perform background access, and convert the data transmitted by the above modules into encrypted methods. At present, there are few Internet-based labor service transaction systems,...
Embodiment 2
[0030] This embodiment is optimized on the basis of Embodiment 1. After the user enters the platform server by entering a key, he checks the encryption program built in the platform server and selects an encryption method. The secondary authentication through the key can effectively improve the security of the system platform.
Embodiment 3
[0032] This embodiment is optimized on the basis of the above embodiments. Users can also upload the encryption software in the U disk to the platform server for installation by accessing the U disk, and increase the encryption method of the platform server. It is more convenient to upload and install the encryption software after using the U disk to access, and the encryption software can be used faster.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More