Social engineering attack defense method and device
An engineering and social technology, applied in the field of defense against social engineering attacks, can solve problems such as failure to meet user security protection needs, single protection mechanism, limitations, etc., and achieve the effect of meeting security protection needs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
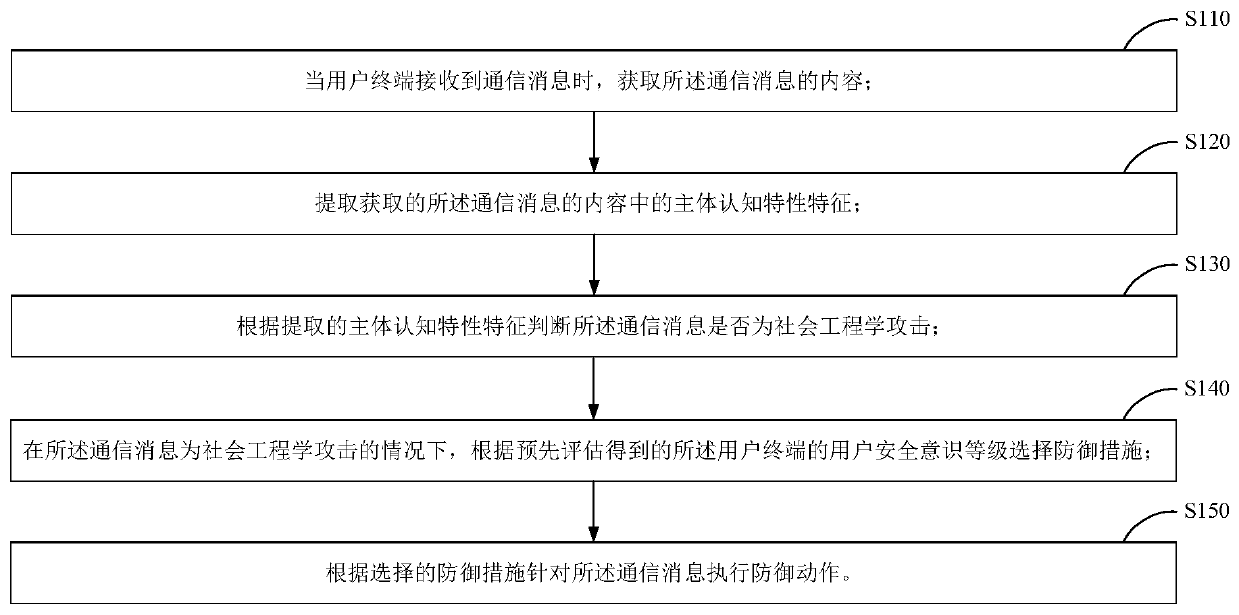
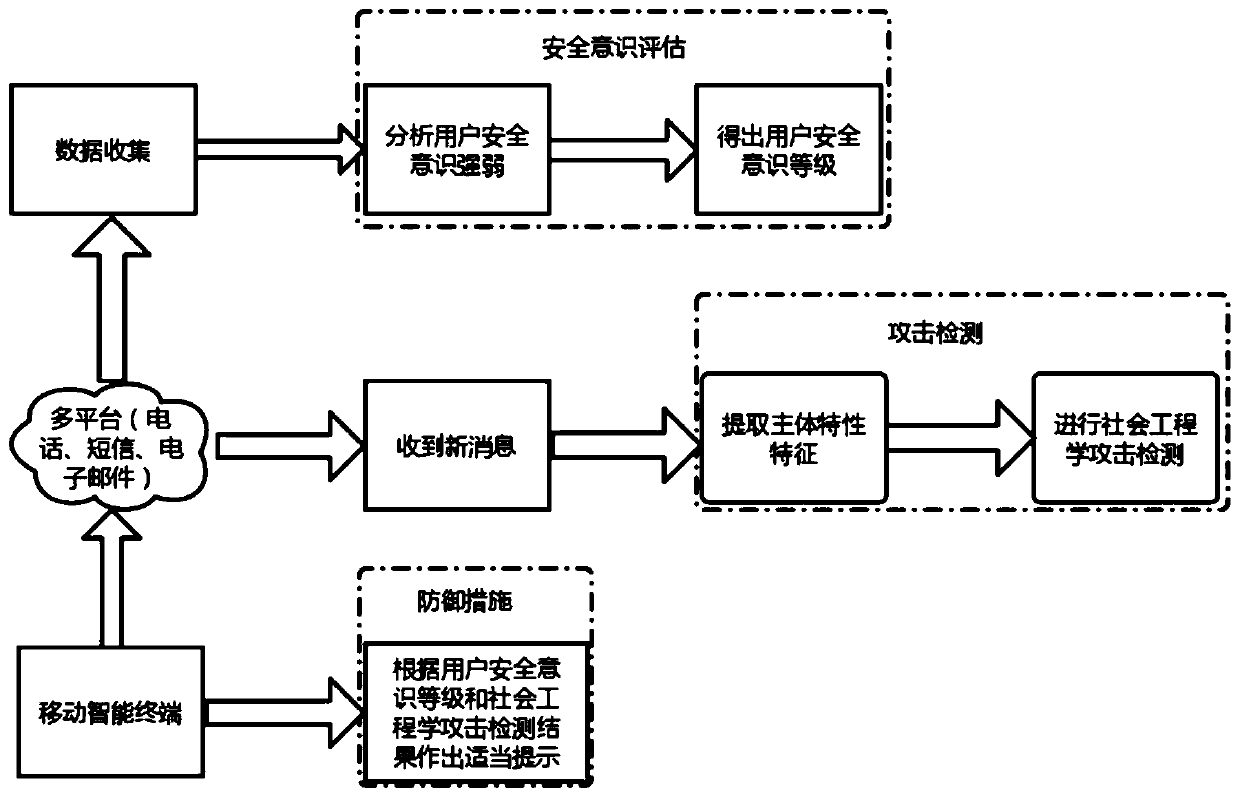
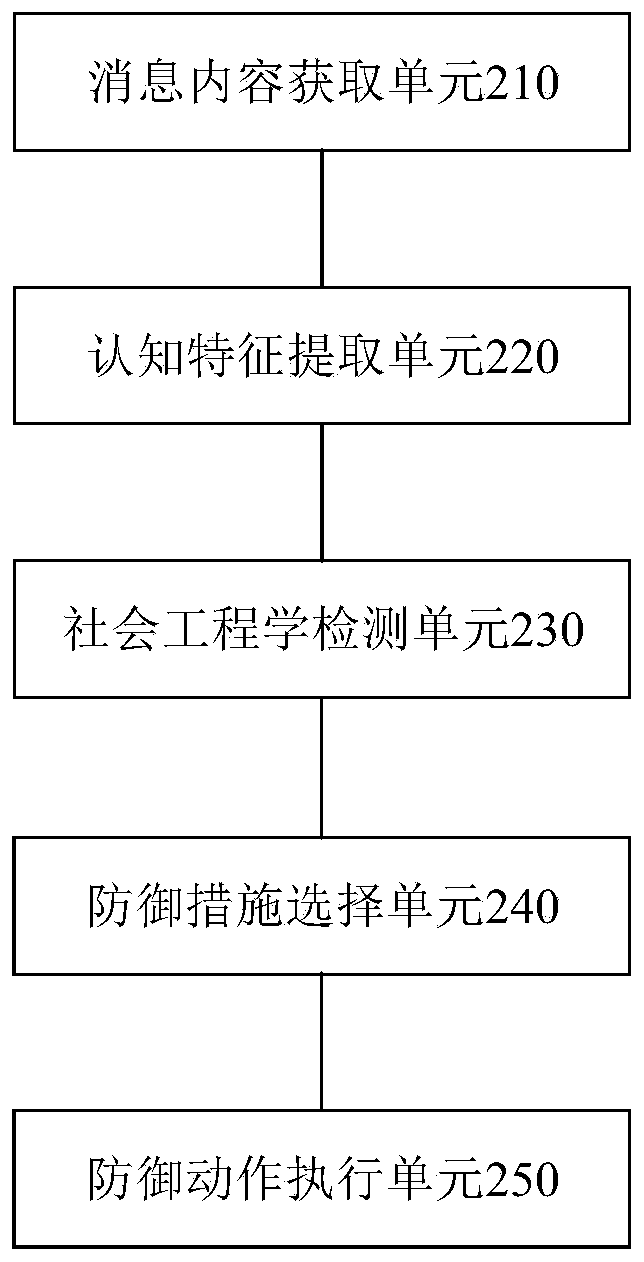
[0021] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the embodiments of the present invention will be further described in detail below in conjunction with the accompanying drawings. Here, the exemplary embodiments and descriptions of the present invention are used to explain the present invention, but not to limit the present invention.
[0022] A user terminal (for example, a mobile phone, a tablet computer) may have multiple communication platforms, for example, China Mobile, China Unicom, WeChat, email, and the like. Users can communicate with the outside world or other terminals or servers through various communication platforms on the user terminal. For example, you can receive incoming calls or text messages through China Mobile or China Unicom, and you can receive text or voice messages, audio / video call requests, etc. through WeChat. Attackers can conduct social engineering attacks on users of...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More