Mining-based continuous attack detection method and system
An attack detection and encryption algorithm technology, applied in transmission systems, digital transmission systems, and key distribution, can solve the problem of separation of persistent network attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] The preferred embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings, so that the advantages and features of the present invention can be more easily understood by those skilled in the art, so as to define the protection scope of the present invention more clearly.
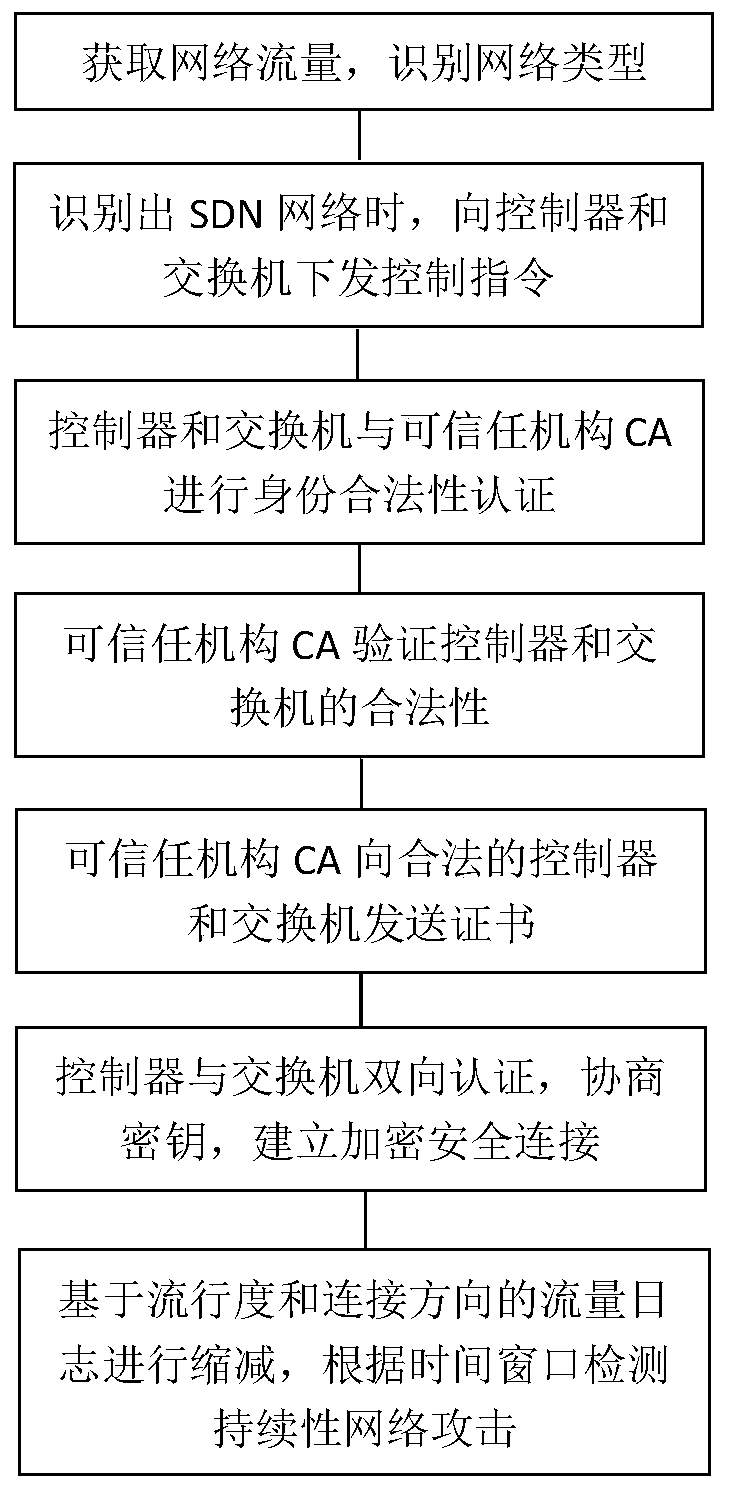
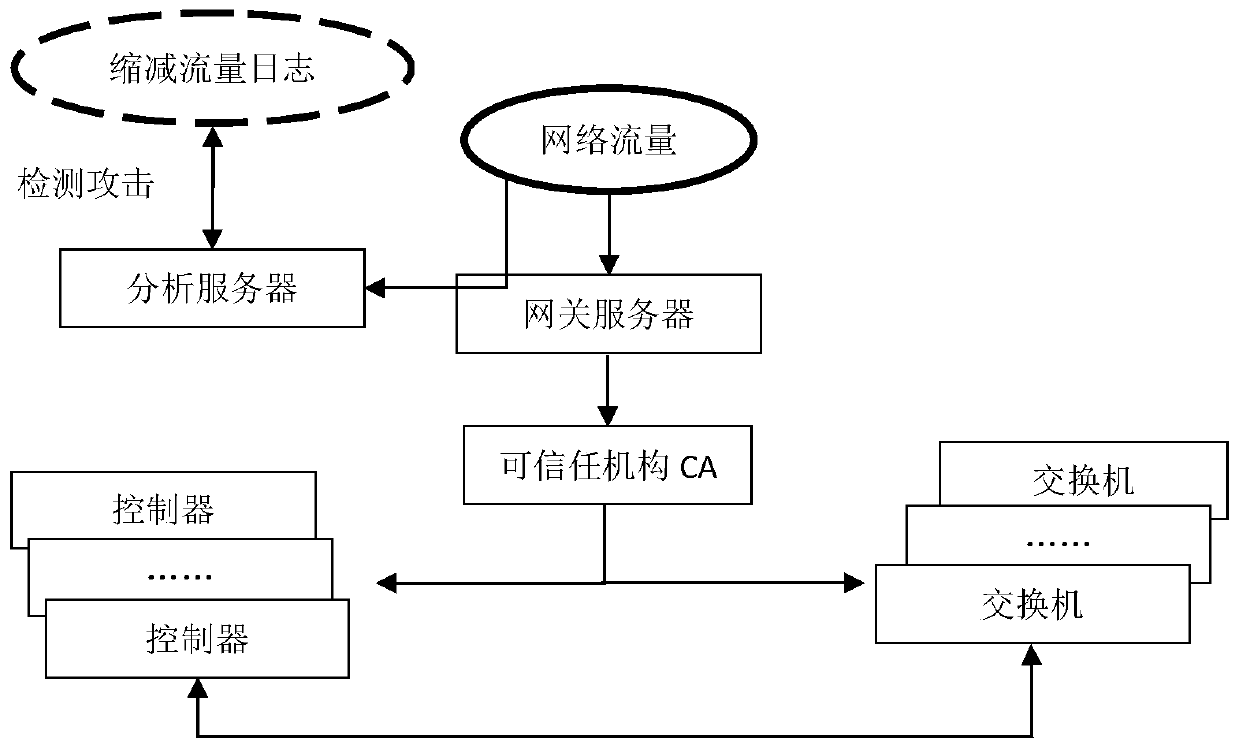
[0045] figure 1 A flow chart of the mining-based continuous attack detection method provided by this application, the method includes:
[0046] Obtain network traffic data and identify network types based on network characteristics;
[0047] When the network is identified as an SDN network, a control command is sent to the controller and the switch, and the control command carries the identification and address of the trusted agency CA in the middle of the network;
[0048] The controller and the switch receive the control instruction, and respectively send an identity authentication request to the network intermediate trusted institution CA, an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More