Method and device for constructing file derivative graph
A construction method and a technology of derived graphs, applied in the field of information security, can solve the problem of time-consuming and labor-intensive, unable to locate the equipment or employees that leak sensitive files, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
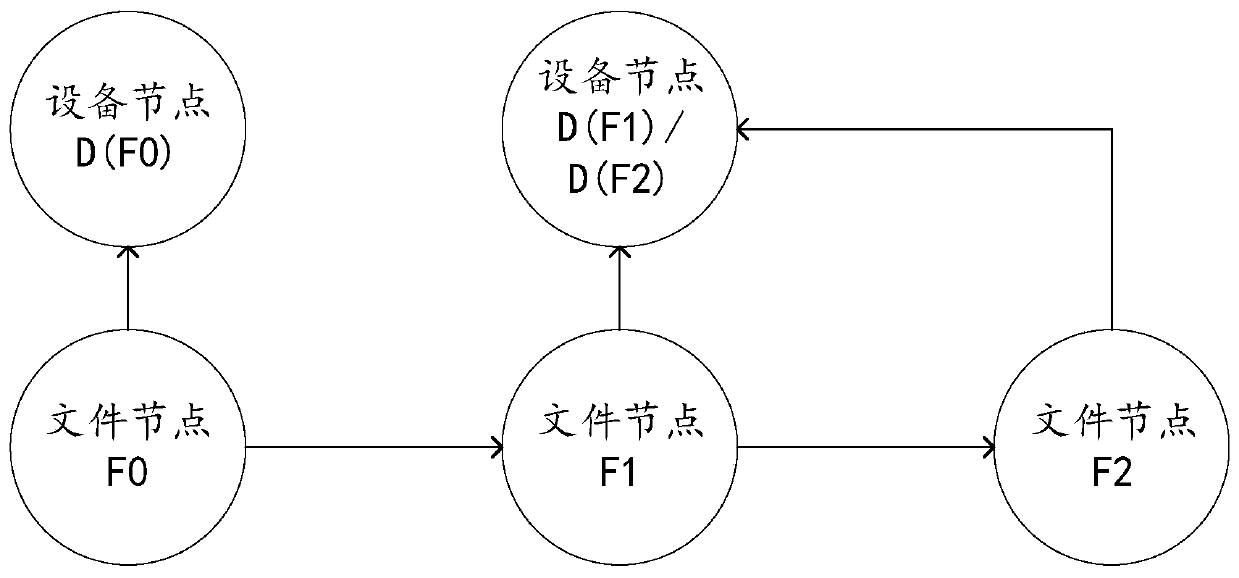
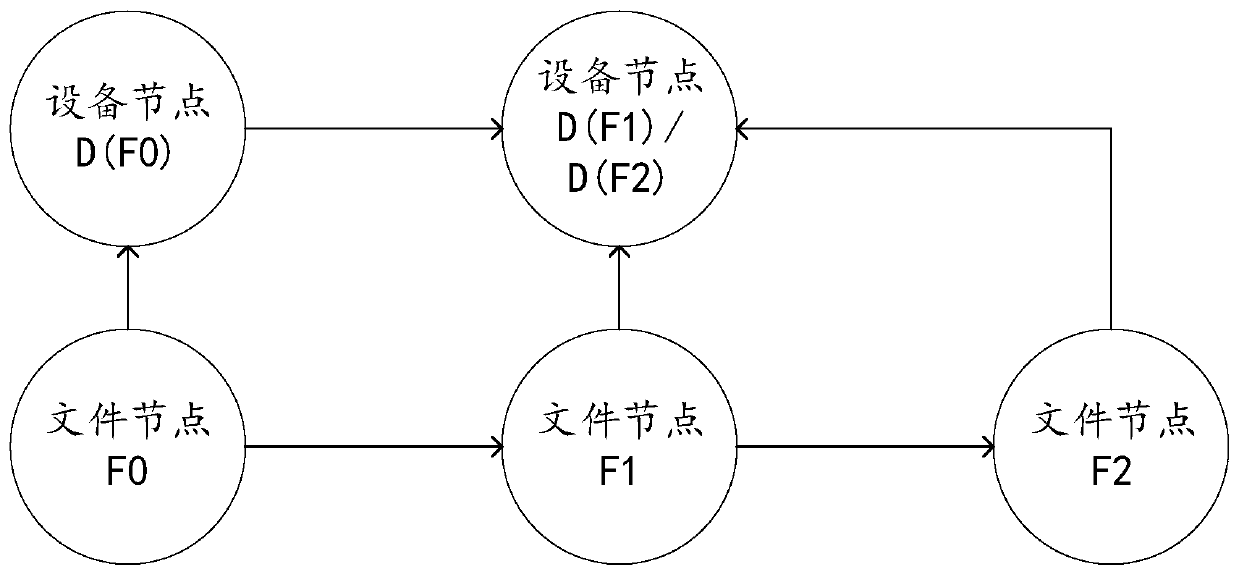
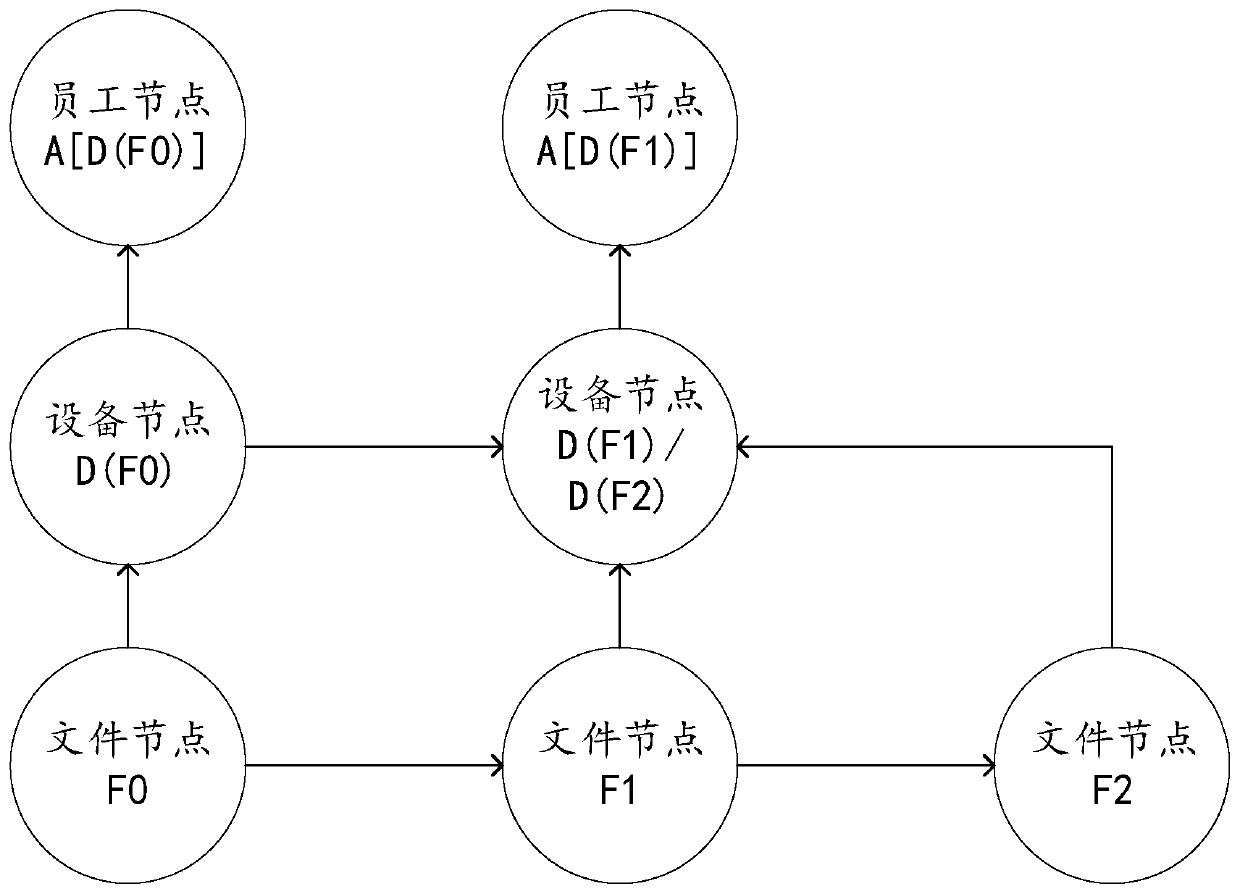
[0039] Many devices in the enterprise contain private data, that is, sensitive files, such as business confidential files or employee privacy files. The enterprise does not want these sensitive files to be leaked, and at the same time, these files need to be transferred between devices within the enterprise for business operations . Therefore, enterprises have a leak-proof security requirement for these sensitive files, which can allow these sensitive files to be transferred between internal devices of the enterprise without being leaked to the outside.
[0040] In order to prevent these sensitive files from being leaked, there are many imperfect anti-leakage strategies. For example, an anti-leakage program is installed on each device of the enterprise, and the anti-leakage program records the digital summaries of all sensitive file contents. When an employee copies or sends a file on an internal enterprise device, the anti-leakage program will calculate the content digital di...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More