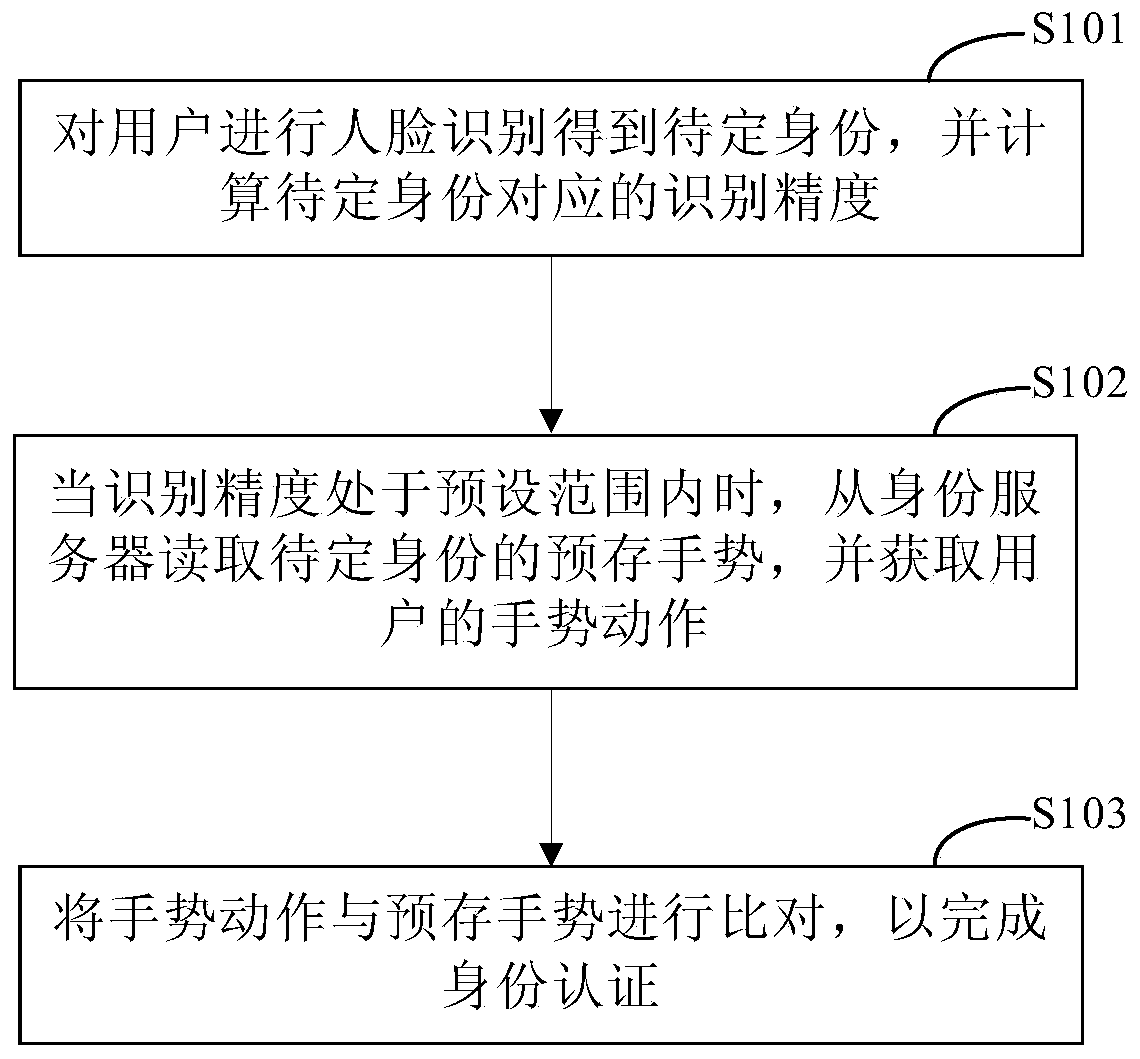
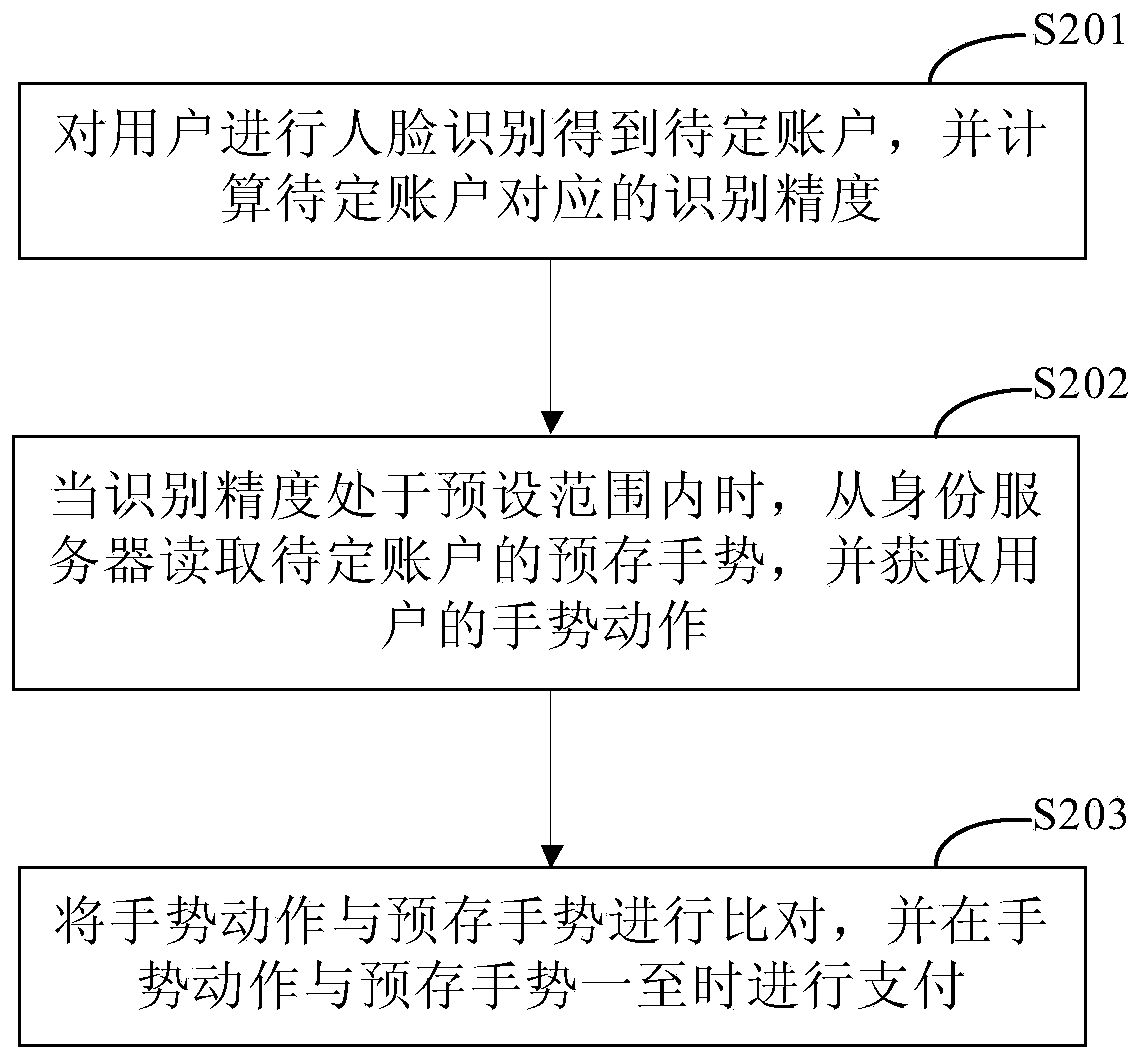
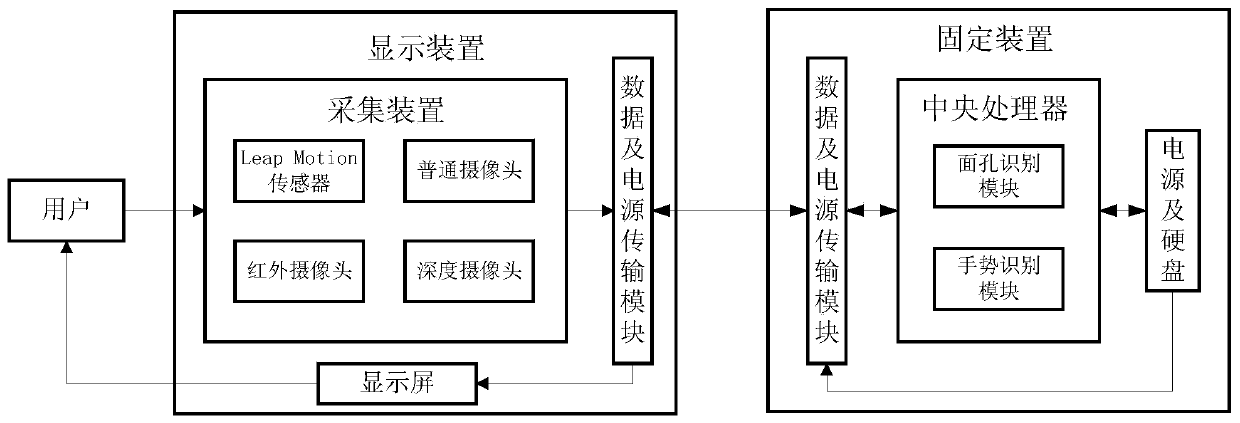
Identity authentication method, payment method and payment equipment
An identity authentication and identity technology, applied in the computer field, can solve problems such as time-consuming
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0074] Exemplary embodiments of the present invention are described below in conjunction with the accompanying drawings, which include various details of the embodiments of the present invention to facilitate understanding, and they should be regarded as exemplary only. Accordingly, those of ordinary skill in the art will recognize that various changes and modifications of the embodiments described herein can be made without departing from the scope and spirit of the invention. Also, descriptions of well-known functions and constructions are omitted in the following description for clarity and conciseness.
[0075] It should be noted that, in the case of no conflict, the embodiments of the present invention and the technical features in the embodiments can be combined with each other.
[0076] Most of the verification methods of the existing face recognition methods are in the form of verifying the mobile phone number, which takes a certain amount of time. For this reason, the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More