Protection method and corresponding device for industrial control network
An industrial control network and network technology, applied in the field of network security, can solve problems such as lack of security design, and achieve the effect of protecting business data
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] The preferred embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings, so that the advantages and features of the present invention can be more easily understood by those skilled in the art, so as to define the protection scope of the present invention more clearly.
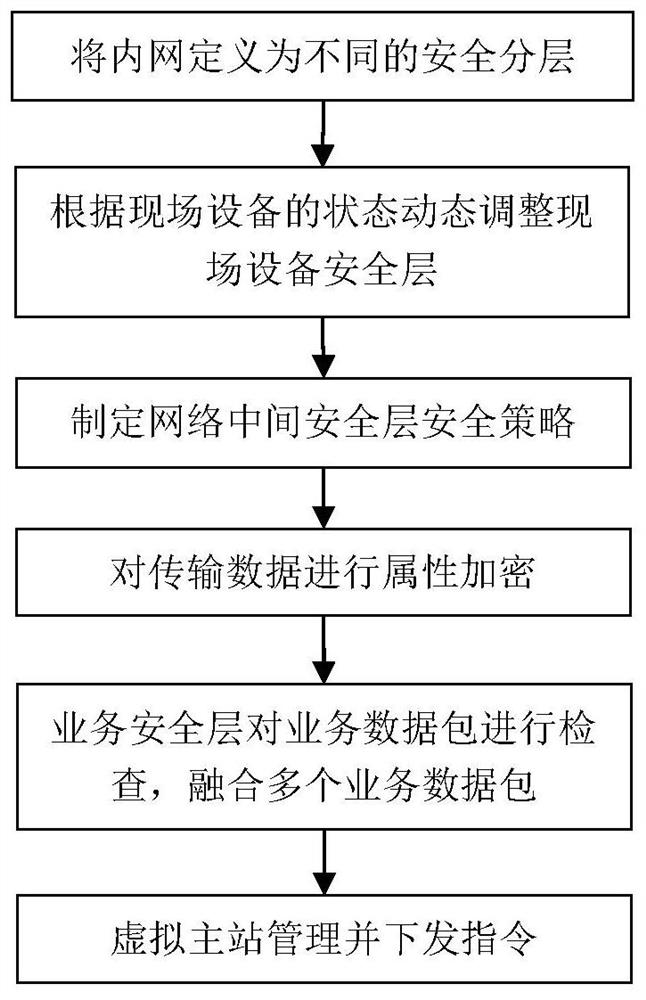
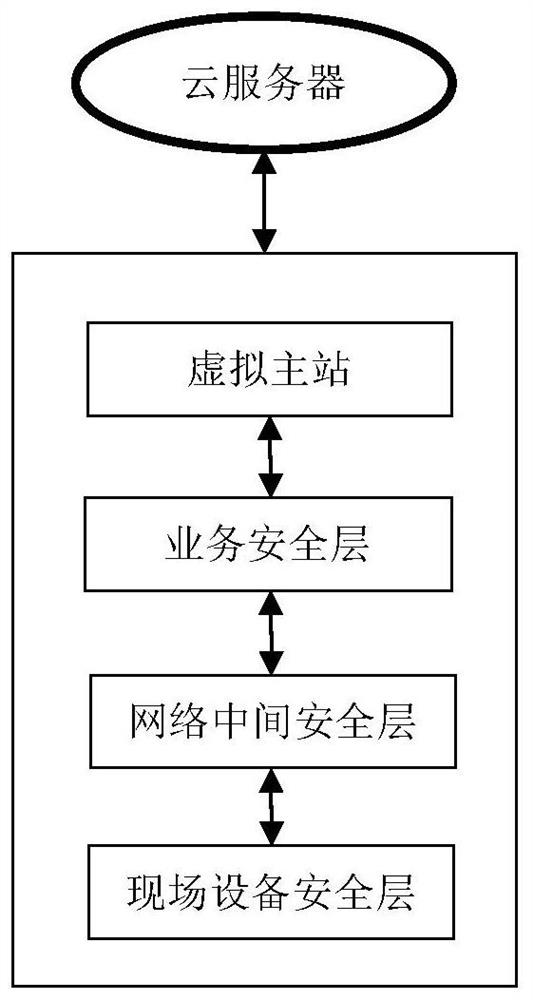
[0033] figure 1 A general flow chart of the protection method of the industrial control network provided by this application, the method includes:
[0034] Define industrial control network resources as field device security layer, network intermediate security layer, business security layer and virtual master station;
[0035] The field device security layer includes: periodically knowing the working status of the field devices in the industrial control network, activating dormant field devices, and dormant field devices with faults, removing the dormant field devices from the field device security layer; establishing a list of permissions , to e...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More