Network attack tracing method and device
A network attack and attack graph technology, applied in the computer field, can solve problems such as inability to carry out effective protection, and achieve the effect of improving traceability efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0046] In order to make the purpose, technical solutions and advantages of the embodiments of the present application clearer, the technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the drawings in the embodiments of the present application.
[0047] In the embodiment of the present application, a network attack source tracing method is provided in order to solve the problem of relying too much on manpower and low tracing efficiency in attack source tracing. This method can be applied to any electronic device, such as a server that manages each host, and the like.
[0048] It should be noted that the host in this embodiment of the present application refers to devices such as network servers.
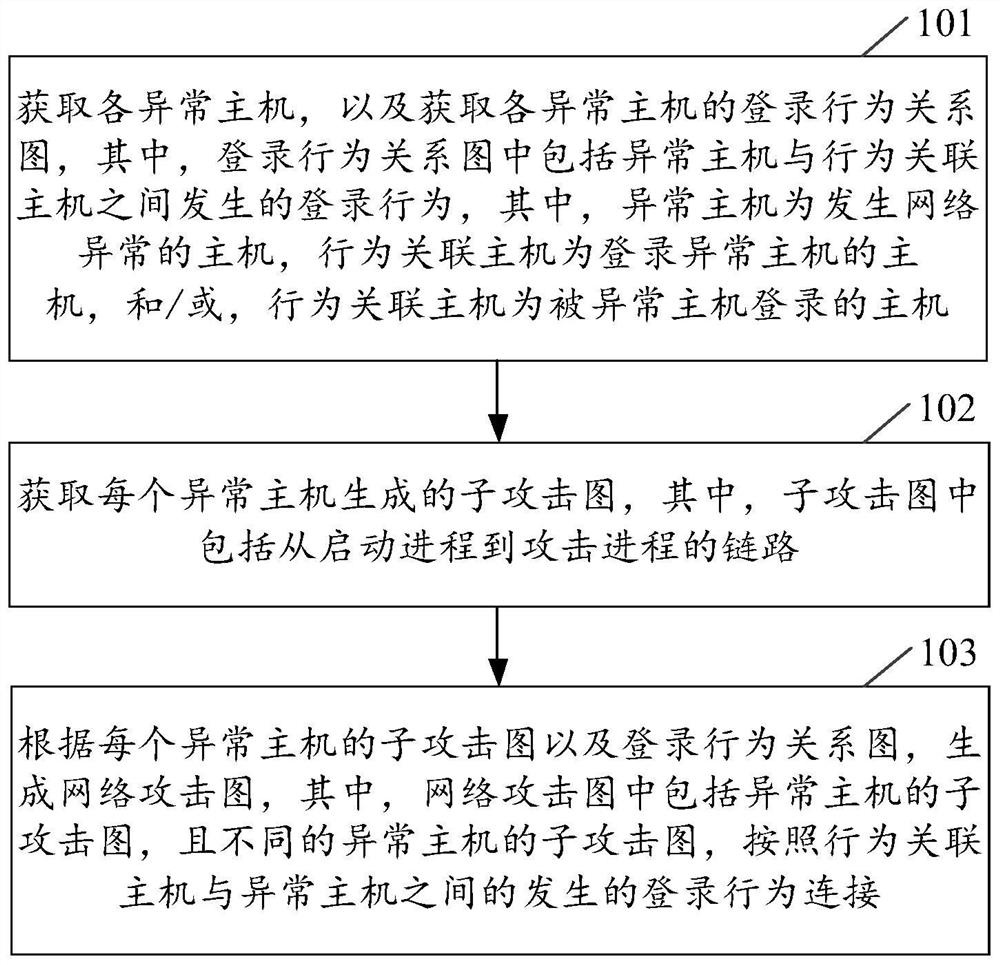
[0049] Such as figure 1 As shown, the specific process of network attack source tracing is as follows:
[0050] Step 101, obtaining each abnormal host and the login behavior relationship diagram of each ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More