Malicious code detection method, data interaction method and related equipment
A malicious code detection and malicious code technology, applied in the fields of data interaction methods and related equipment, malicious code detection methods, can solve the problems of being easily evaded and low recognition rate, and achieve the effect of improving the recognition rate
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Example Embodiment
[0055]In order to make the purpose, technical solutions and advantages of the present application, the present application will be described in further detail below with reference to the accompanying drawings and examples. It should be understood that the specific embodiments described herein are intended to explain the present application and is not intended to limit the present application.
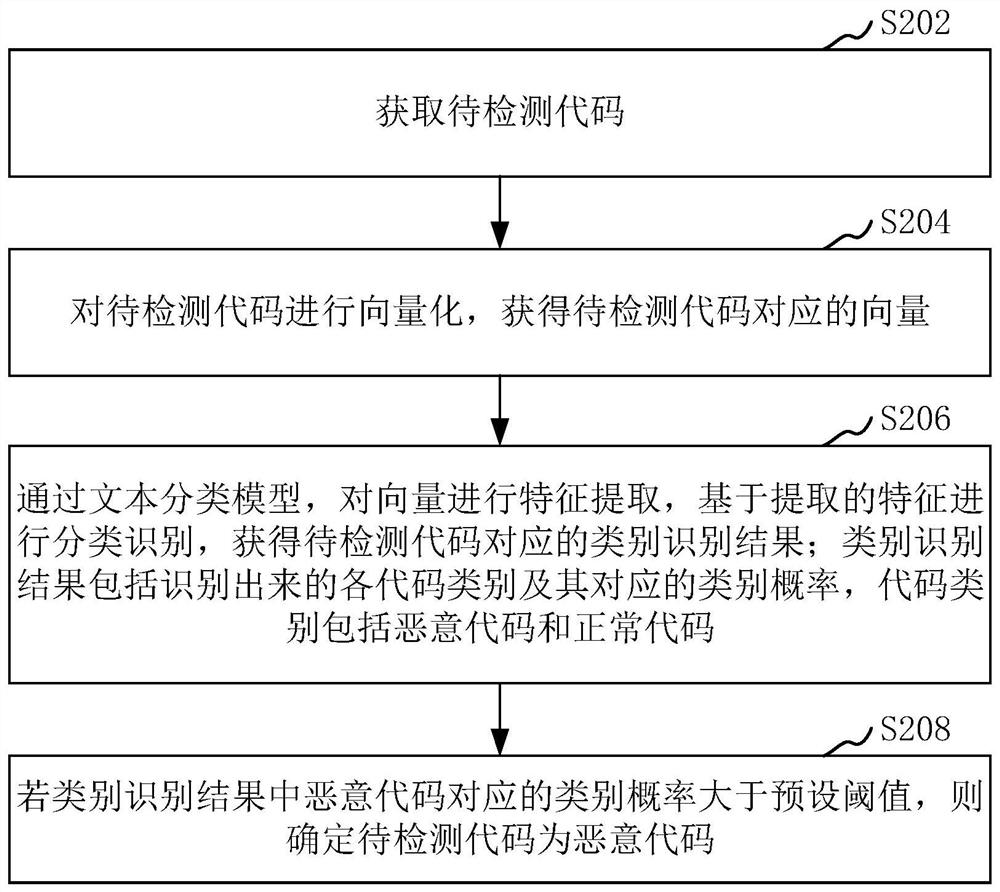
[0056]The malicious code detection method provided herein can be applied tofigure 1 The application environment is shown. The application environment relates to terminal 102 and server 104, terminal 102, and server 104 through a network connection. The user can access the web page through the terminal 102, and the server 104 can a web server. The terminal 102 and server 104 can perform malicious code detection. In one embodiment, the server 104 detects whether the page request data exists before the page request data transmitted by the terminal 102. When the page request data does not have malic...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More