Database access control method and device
An access control and database technology, applied in the field of information security, can solve problems such as inability to complete access, waste of trial and error opportunities, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
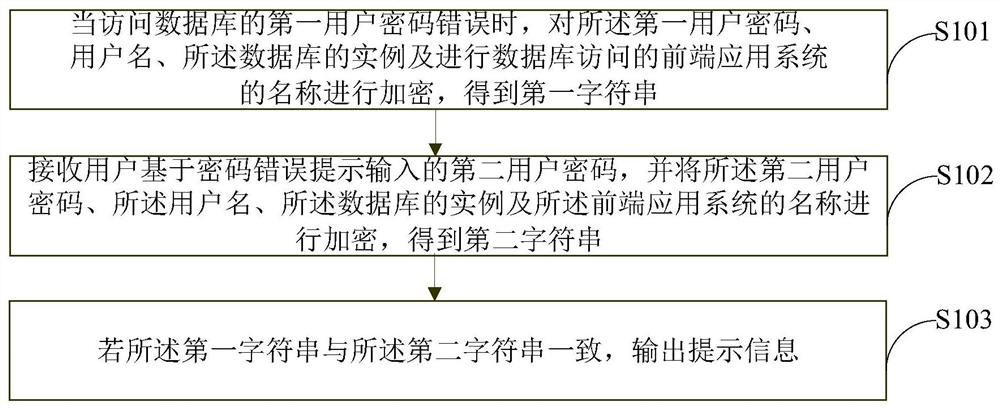
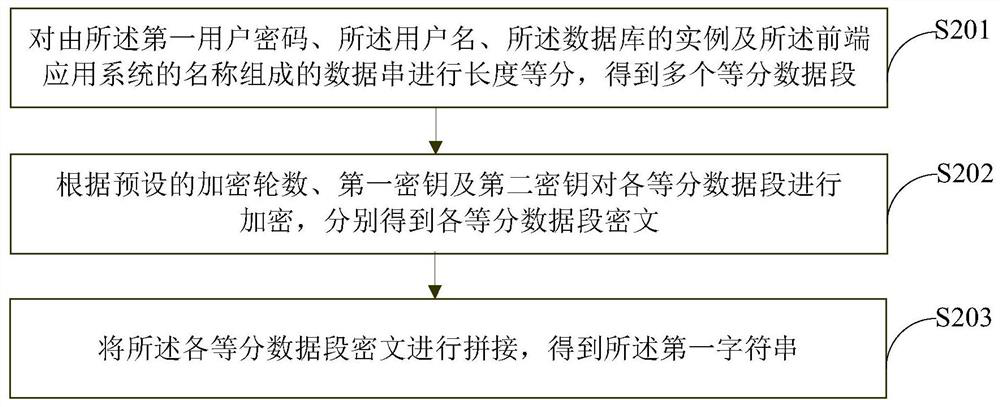
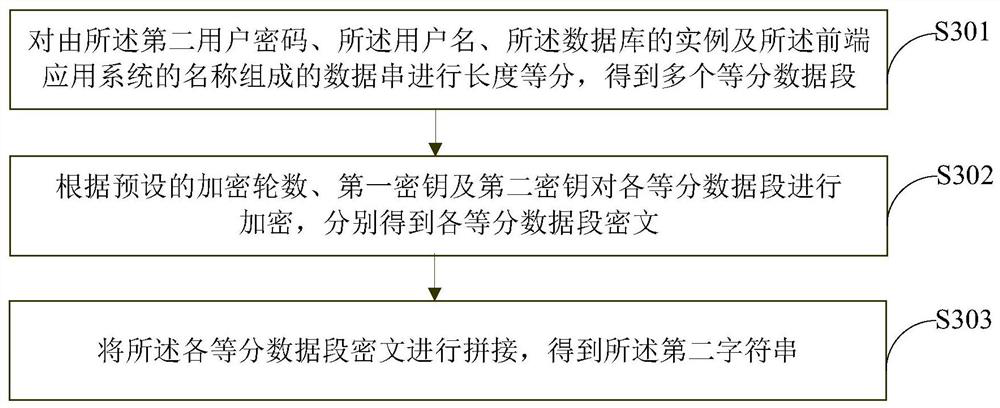
[0056] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some, not all, embodiments of the application. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0057]Under normal circumstances, the user needs to enter the correct user password (hereinafter also referred to as "database access password" or "password" for short) before being allowed to access the database. For the sake of information security, traditional access control mechanisms generally do not allow users to repeatedly try and make mistakes on user passwords, but set a reasonable threshold (such as three times) for the number of trials and mistakes to reduce illegal users from repeated...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More