Information risk prevention and control method, device and equipment
A risk, prevention and control technology, applied in the computer field
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
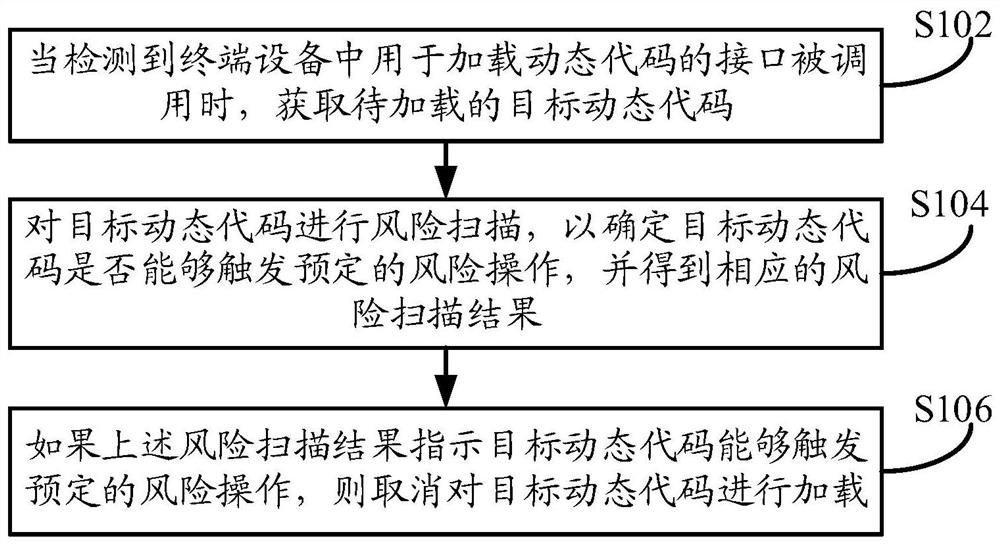
[0019] Such as figure 1 As shown, the embodiment of this specification provides a method for information risk prevention and control. The execution body of the method can be a server or a terminal device, wherein the terminal device can be a computer device such as a laptop or a desktop computer, or a mobile phone or Tablet PC and other mobile terminal equipment. The server may be a server for a certain business (such as transaction business or financial business, etc.) or a server that needs to prevent and control the risk of the code contained in the specified application program. Specifically, the server may be a payment business server, or It can be a server related to business such as finance or instant messaging. The execution subject in this embodiment is described by taking a terminal device as an example. For a case where the execution subject is a server, reference may be made to the following relevant content, and details are not repeated here. The method specific...
Embodiment 2
[0032] Such as image 3 As shown, the embodiment of this specification provides a method for information risk prevention and control. The execution body of the method can be a server or a terminal device, wherein the terminal device can be a computer device such as a laptop or a desktop computer, or a mobile phone or Tablet PC and other mobile terminal equipment. The server may be a server for a certain business (such as transaction business or financial business, etc.) or a server that needs to prevent and control the risk of the code contained in the specified application program. Specifically, the server may be a payment business server, or It can be a server related to business such as finance or instant messaging. The execution subject in this embodiment is described by taking a terminal device as an example. For a case where the execution subject is a server, reference may be made to the following relevant content, and details are not repeated here. The method specific...
Embodiment 3
[0053] The above is the information risk prevention and control method provided by the embodiment of this specification. Based on the same idea, the embodiment of this specification also provides an information risk prevention and control device, such as Figure 4 shown.
[0054] The risk prevention and control device for this information includes: a dynamic code acquisition module 401, a risk scanning module 402 and an unloading module 403, wherein:
[0055] The dynamic code obtaining module 401, when detecting that the interface for loading the dynamic code in the terminal device is called, obtains the target dynamic code to be loaded;
[0056] The risk scanning module 402 performs risk scanning on the target dynamic code to determine whether the target dynamic code can trigger a predetermined risk operation, and obtains a corresponding risk scanning result;
[0057] The unloading module 403, if the risk scanning result indicates that the target dynamic code can trigger a p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More