Service access method, device and equipment and computer readable storage medium
A business access and business technology, applied in the computer field, can solve problems such as unusable products, and achieve the effect of improving user experience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
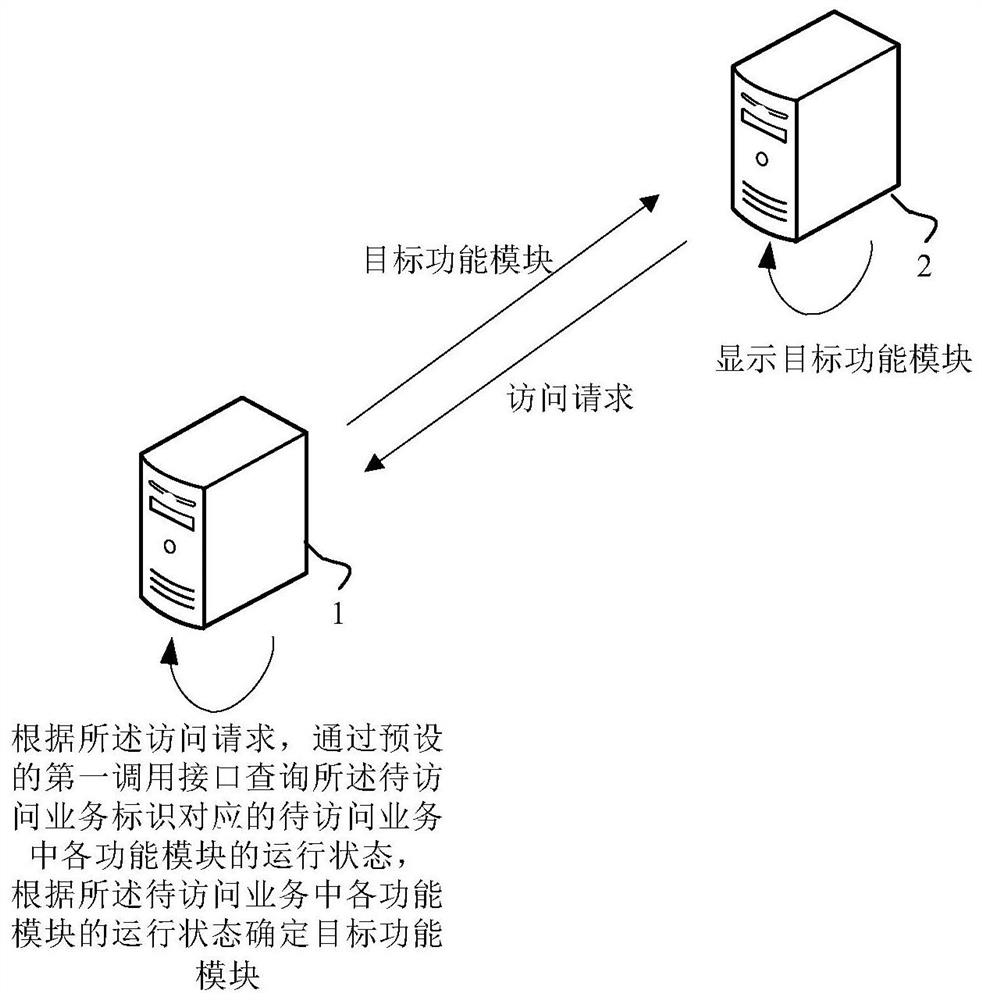
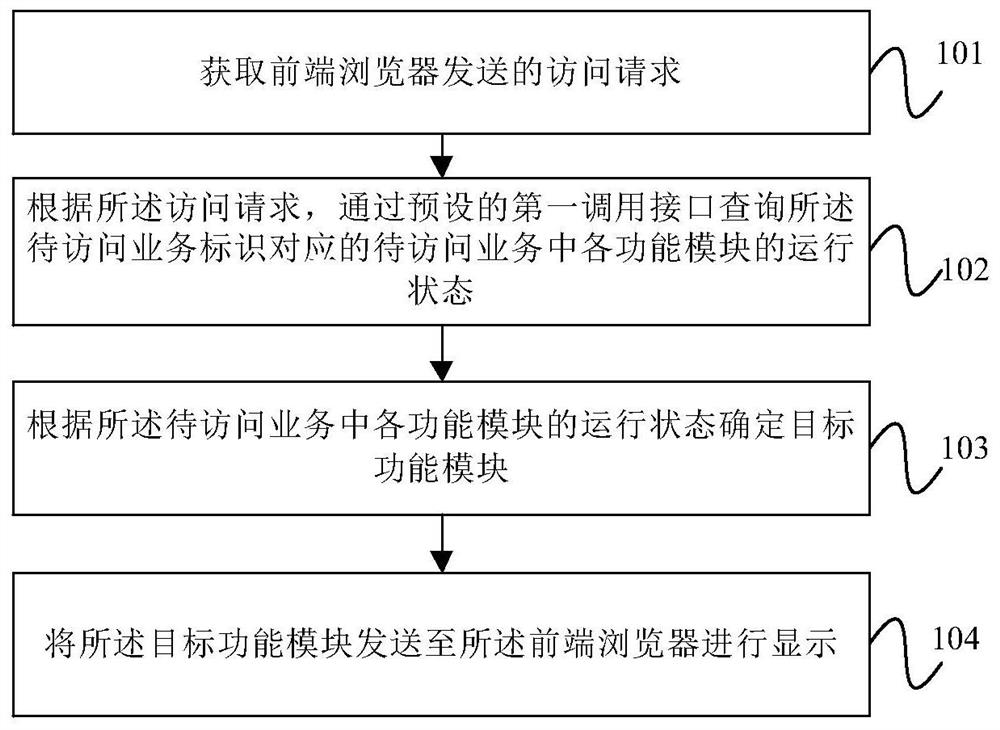
[0041] figure 2 A schematic flowchart of the service access method provided by Embodiment 1 of the present disclosure, as shown in figure 2 As shown, the method includes:
[0042] Step 101. Obtain an access request sent by a front-end browser, where the access request includes an identifier of a service to be accessed.
[0043] The implementation subject of this embodiment is a service access device, which can be coupled to a server. The server can communicate with the front-end browser, so as to exchange information with the front-end browser.
[0044] In this embodiment, the user can trigger an access request on the front-end browser. Specifically, the front-end browser can be provided with a plurality of icons corresponding to different services to be accessed, and the user can trigger the icon to generate an access request according to actual needs, wherein the trigger operation can be single click, double click, long press, etc.
[0045] After the front-end server g...
Embodiment 2
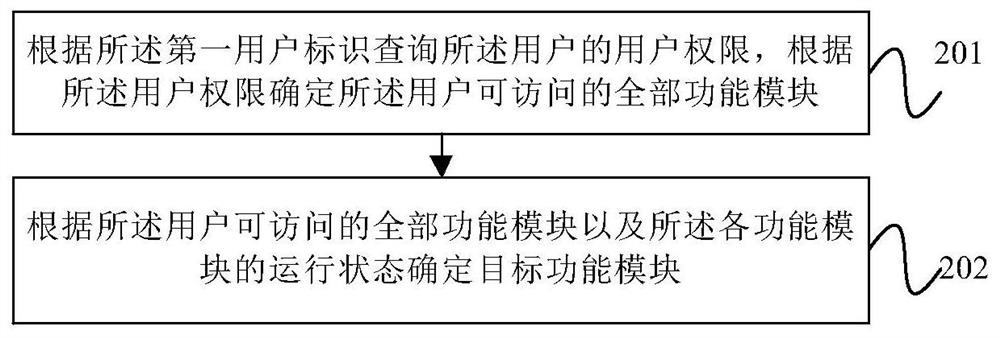
[0058] image 3 It is a schematic flowchart of the service access method provided in Embodiment 2 of the present disclosure. On the basis of Embodiment 1, the access request may further include the first user identifier corresponding to the user who triggered the access request. The first user identifier can uniquely represent the identity of the user. After step 102, the method also includes:
[0059] Step 201: Query the user authority of the user according to the first user identifier, and determine all functional modules accessible to the user according to the user authority.
[0060] Step 103 specifically includes:
[0061] Step 202: Determine a target function module according to all function modules accessible to the user and the running status of each function module.
[0062] In this embodiment, the access request may further include a first user identifier corresponding to the user of the access request. Therefore, the user authority of the user can be determined ...
Embodiment 3
[0071] Figure 4 The schematic flowchart of the service access method provided by Embodiment 3 of the present disclosure, on the basis of any of the above embodiments, after step 103, further includes:
[0072] Step 301. According to the first user identifier, determine whether the first user identifier satisfies a preset filtering rule.
[0073] Step 302, if it is satisfied, obtain the function module to be updated.
[0074] Step 303 , sending the function module to be updated and the target function module to the front-end browser for display, so that the user can invoke the function module to be updated and the target function module.
[0075] In this embodiment, when the product corresponding to the service identifier to be processed has a new function on the line, because some new functions may put a lot of pressure on the server, or the new function may not be perfect, the new function cannot be fully launched for all users. Function.
[0076] Or, when the product is ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com