Method and device for monitoring and analyzing encrypted traffic in real time
A real-time monitoring and flow technology, applied in the direction of security communication devices, digital transmission systems, electrical components, etc., can solve the problems of low security and stability of application servers, improve security and stability, improve work efficiency, reduce effect of complexity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] In order to make the purpose, technical solution and advantages of the present application clearer, the technical solution of the present application will be described in detail below. Apparently, the described embodiments are only some of the embodiments of this application, not all of them. Based on the embodiments in the present application, all other implementation manners obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present application.
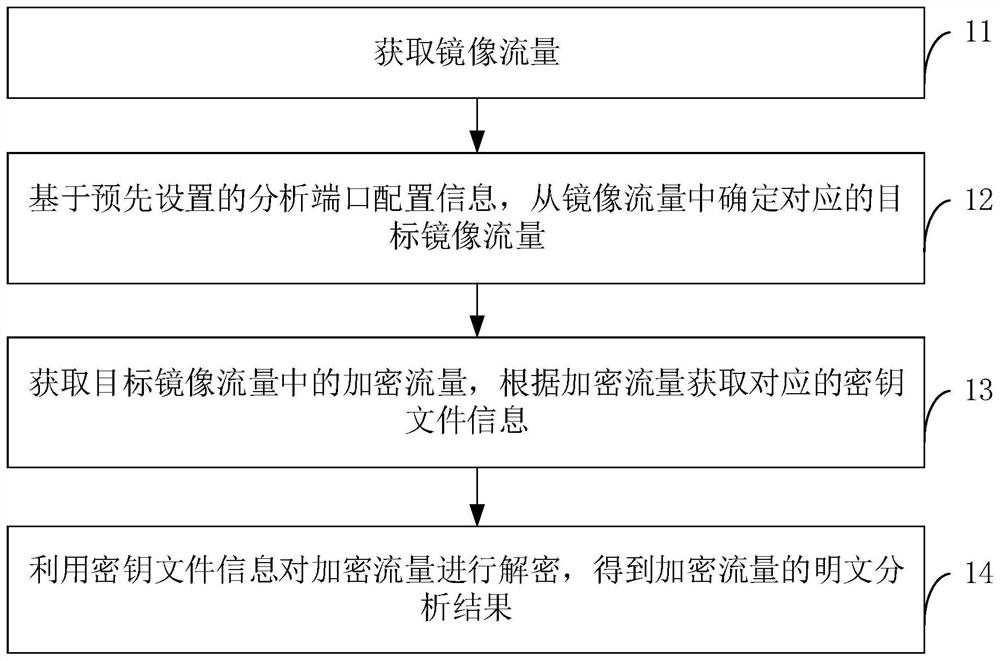
[0036] join figure 1 It is a flowchart of a method for real-time monitoring and analysis of encrypted traffic provided by an embodiment of the present application. Embodiments of the present application provide a method for real-time monitoring and analysis of encrypted traffic. As shown in the figure, the method may at least include the following steps:
[0037] Step 11. Obtain mirrored traffic.
[0038] During implementation, obtaining mirrored traffic is re...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More