Network access method, device, system and equipment and storage medium
A technology for network access and network access control, applied in the fields of equipment and storage media, systems, devices, and network access methods, can solve problems such as time-out or failure of ticket acquisition, poor availability, frequent network access failures, etc., to improve stability and performance. The effect of usability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
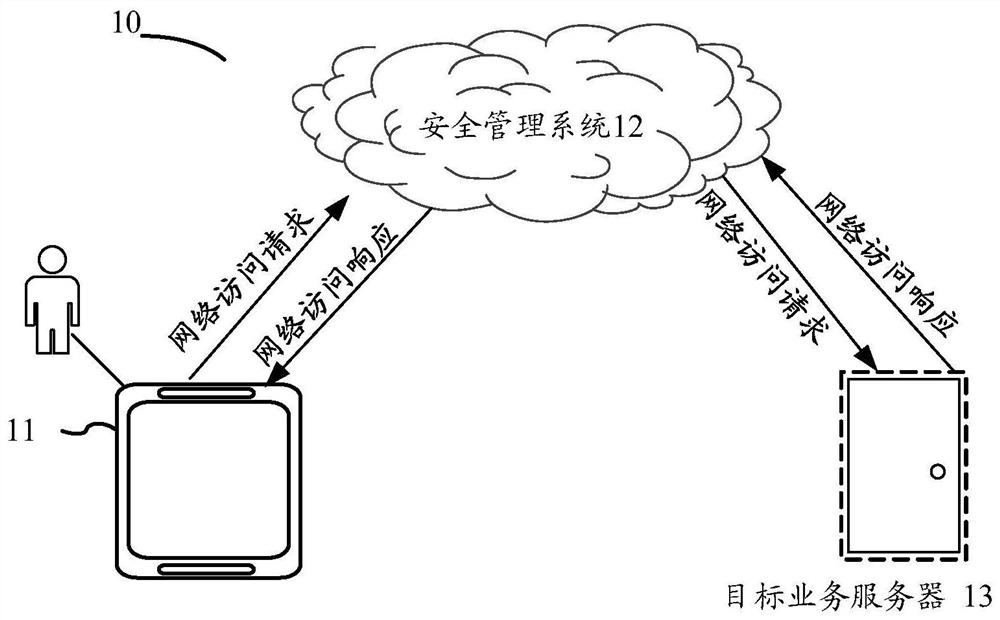
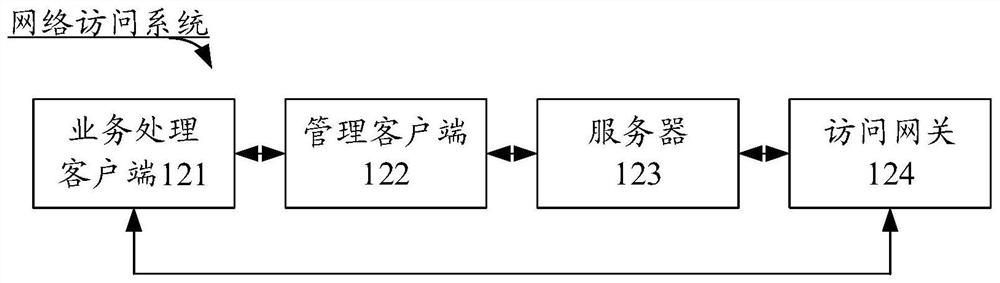
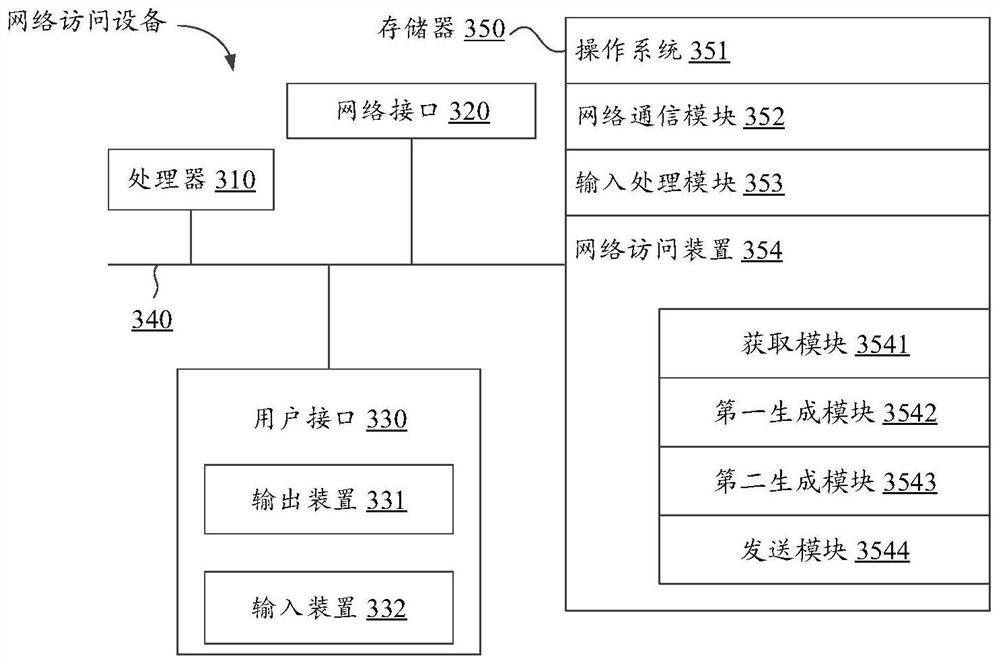
[0050] In order to make the purpose, technical solutions and advantages of the present application clearer, the present application will be described in further detail below with reference to the accompanying drawings. All other embodiments obtained under the premise of creative work fall within the scope of protection of the present application.
[0051] In the following description, reference is made to "some embodiments" which describe a subset of all possible embodiments, but it is understood that "some embodiments" can be the same or a different subset of all possible embodiments, and Can be combined with each other without conflict. Unless otherwise defined, all technical and scientific terms used in the embodiments of the present application have the same meaning as commonly understood by those skilled in the technical field belonging to the embodiments of the present application. The terms used in the embodiments of the present application are only for the purpose of ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More