System and a method for management of confidential data
a technology of confidential data and management method, applied in the field of systems and methods for managing confidential data, can solve problems such as untrustworthy services and confidentiality breaches
Active Publication Date: 2019-07-16
KMAAS APS +1
View PDF48 Cites 2 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
This approach enhances data confidentiality by distributing trust among multiple key servers, preventing a single point of attack and maintaining high performance through symmetric encryption, while ensuring secure encryption and decryption processes.
Problems solved by technology
Common to these cloud services is that they are untrusted services which are arranged in the cloud.
One problem with the traditional cloud services is that users must trust that the data that they store in the cloud service remains confidential, e.g., that the data stored in the cloud service is not misused due to the cloud service being compromised by hackers, due to corrupted cloud service administrators, or due to legal enforcements in the country where the cloud service is hosted.
Thereby there is a risk that a malicious attack is performed on the single point of trust, thereby gaining access to the encryption / decryption keys.
Accordingly, the central key generator constitutes a single point of trust, which may potentially be attacked, leading to a breach of confidentiality.
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
first embodiment
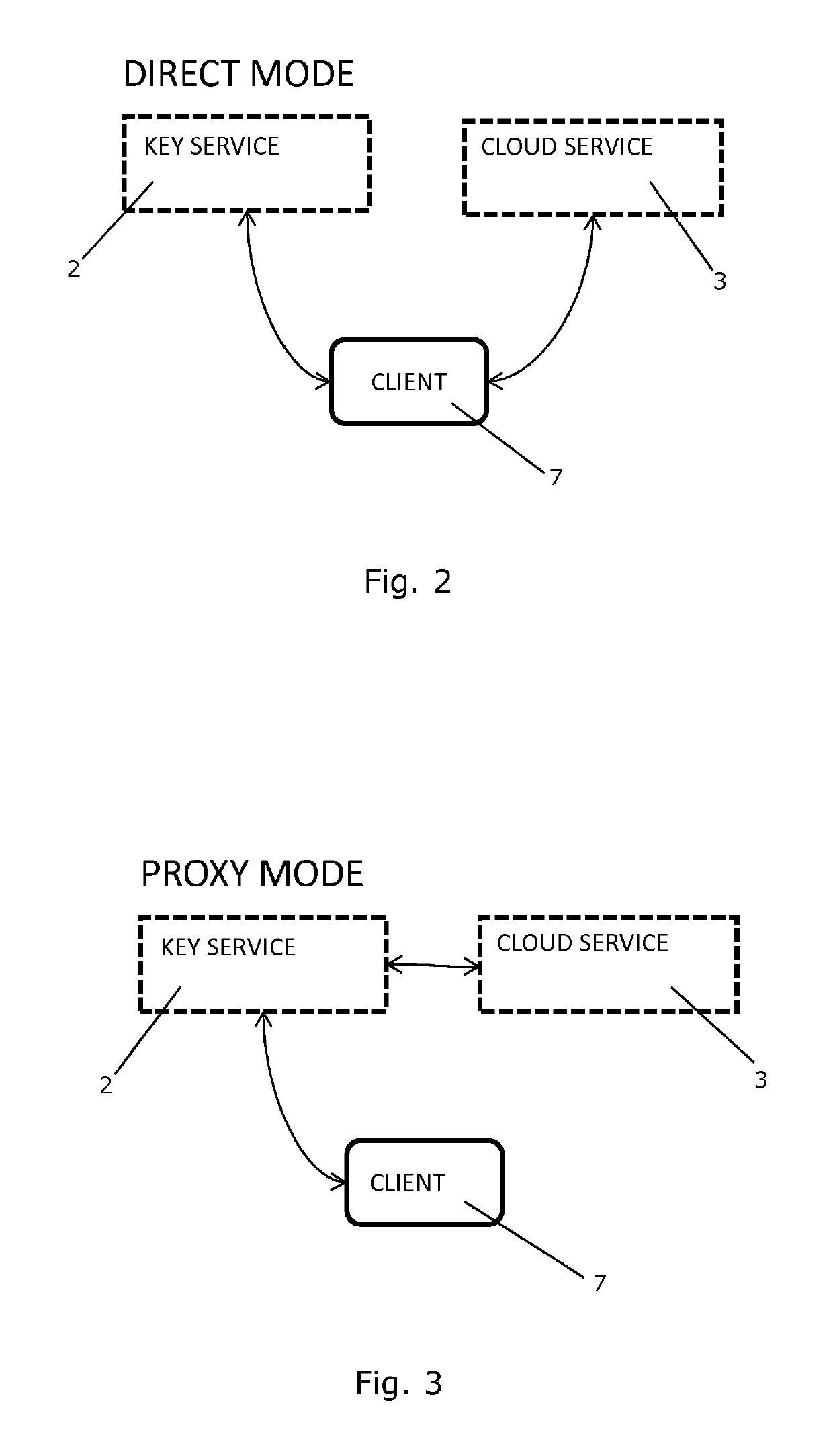
[0112]FIG. 2 illustrates communication between a client device, a cryptographic key service, and a cloud service according to the invention,
second embodiment
[0113]FIG. 3 illustrates communication between a client device, a cryptographic key service, and a cloud service according to the invention,
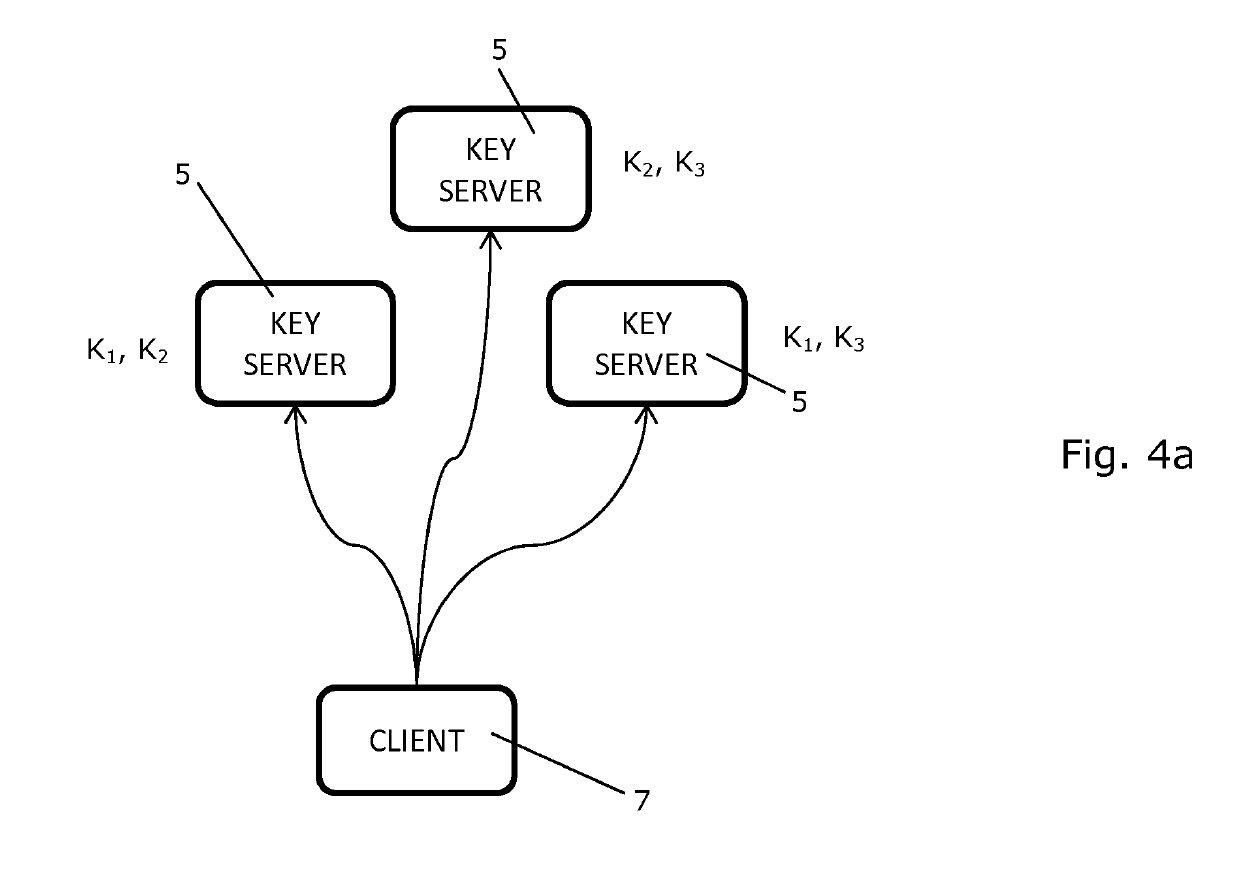
[0114]FIGS. 4a-4c illustrate various steps of a method according to an embodiment of the invention, and
[0115]FIG. 5 is a flow diagram illustrating a method according to an embodiment of the invention.
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
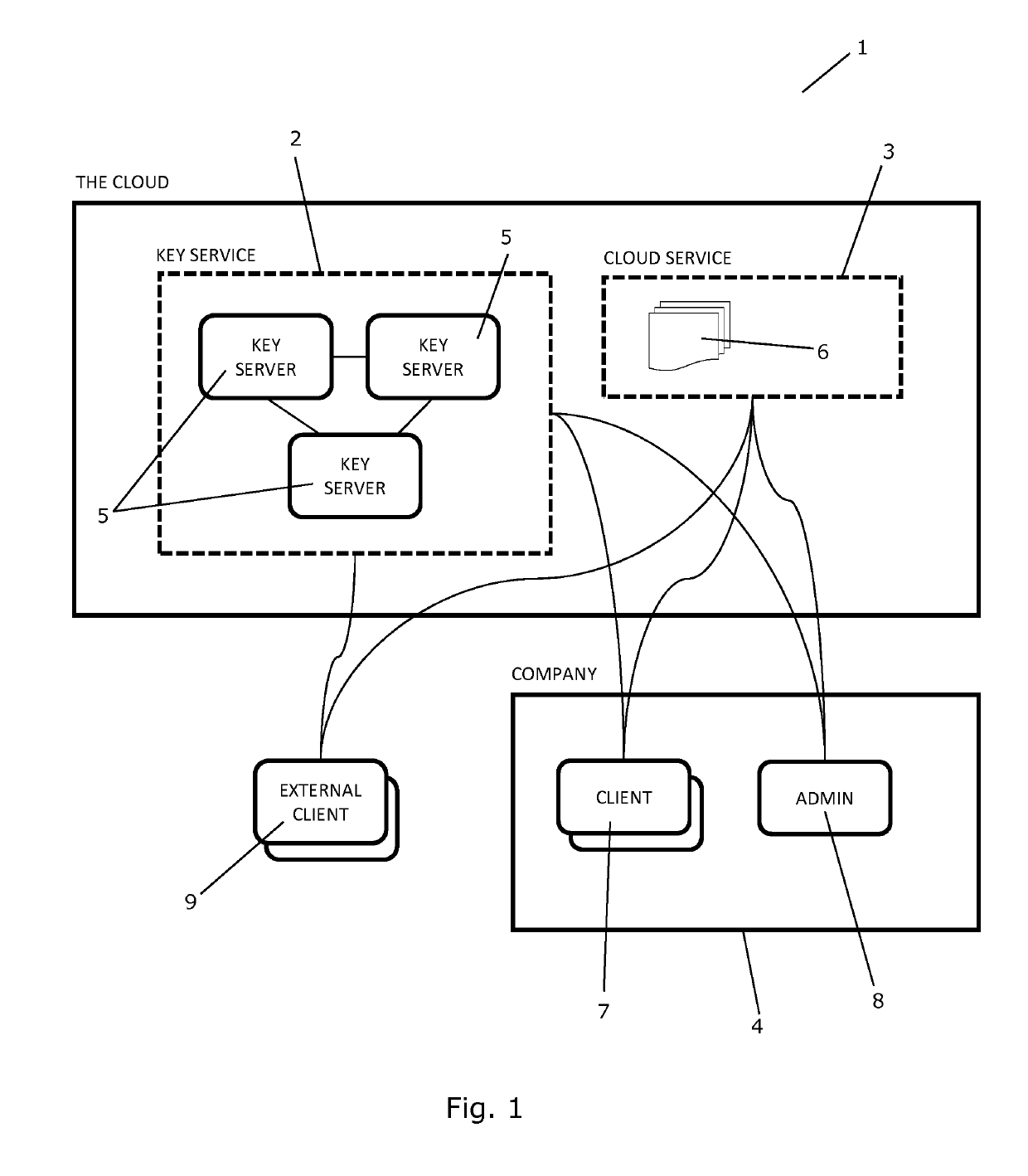
A system and a method for managing confidential data in a cloud service is provided. The system comprises a cryptographic key service comprising two or more cryptographic key servers, Si, each being arranged to compute file encryption keys, kj, on the basis of information regarding data and using one or more cryptographic keys, Kj. The cryptographic keys, Kj, are secretly shared among the cryptographic key servers, Si, and none of the cryptographic key servers, Si, possesses knowledge of all of the cryptographic keys, Kj. A single point of trust at the cryptographic key service is avoided.
Description
CROSS REFERENCE TO RELATED APPLICATIONS[0001]This is a national stage filing in accordance with 35 U.S.C. § 371 of PCT / EP2014 / 072491, filed Oct. 21, 2014, which claims the benefit of the priority of European Patent Application No. 13190481.5, filed Oct. 28, 2013, the contents of each are incorporated herein by reference.FIELD OF THE INVENTION[0002]The present invention relates to a system and a method for managing confidential data in a cloud service in a secure manner, i.e. in a manner which to the greatest possible extent guarantees the confidentiality of the data.BACKGROUND OF THE INVENTION[0003]It is sometimes desirable to store data files, or to provide other kinds of data, remotely from a local system or a closed local environment, e.g. in order to be able to access the data from various location and / or using various devices, and / or in order to be able to share the data among two or more users. To this end cloud services, such as Dropbox®, Google® Drive, SkyDrive®, Amazon® S3,...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More Patent Type & Authority Patents(United States)
IPC IPC(8): H04L9/08G06F21/62H04L29/06
CPCG06F21/6218H04L9/085H04L9/088H04L63/062H04L9/0861H04L63/0428H04L63/06H04L9/0819G06F21/602H04L9/0891H04L9/0894
Inventor DAMGARD, IVAN BJERREJAKOBSEN, THOMAS PELLEPAGTER, JAKOB ILLEBORG
Owner KMAAS APS