An end-to-end communication authentication method and device
An authentication method and authentication mode technology, which is applied in the field of network security, can solve problems such as unreasonable, inability to handle authentication methods in a unified way, and duplication of interactive messages, and achieve the effect of simplifying authentication steps and flexible content
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
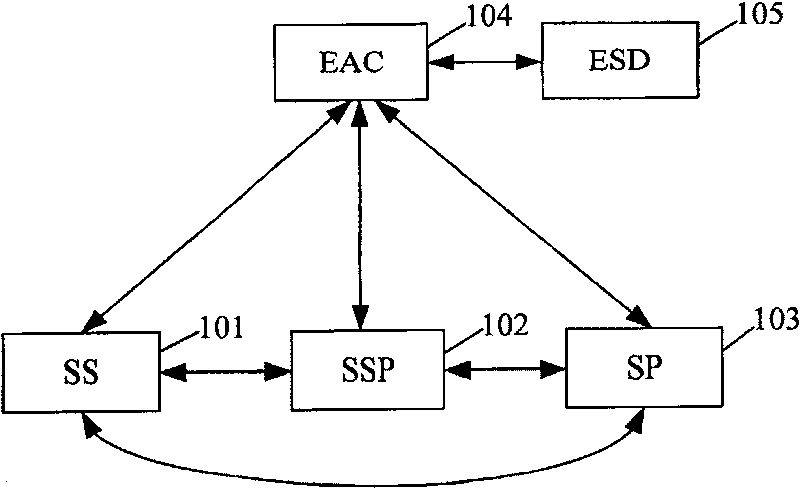
Image
Examples
Embodiment Construction
[0048] The present invention will be further described below with reference to the accompanying drawings and examples, but it is not intended to limit the present invention.
[0049] The end-to-end communication authentication method of the present invention is as follows:
[0050] First define the authentication mode:
[0051]The E2E authentication mode is mainly determined by the authentication methods of SS and EAC, and sometimes also by the authentication methods of SS and SP. In the authentication mode, the authentication method of SS and EAC, the authentication method of SP and EAC, the authentication method between SS and SP, and the session key generation method are set; for different authentication modes, only the above authentication methods can be set one or more of. For example, in the case where SS and SP can directly authenticate and establish a secure connection, there is no need to perform authentication between SS and EAC and SP and EAC, then only need to se...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More