Realizing method of general-purpose digital signing scheme
A technology of digital signature and implementation method, applied in the field of information security, can solve the problems of difficulty in implementing a threshold digital signature scheme and an unsatisfactory digital signature scheme, and achieve the effects of saving communication bandwidth, reducing signature length and high efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
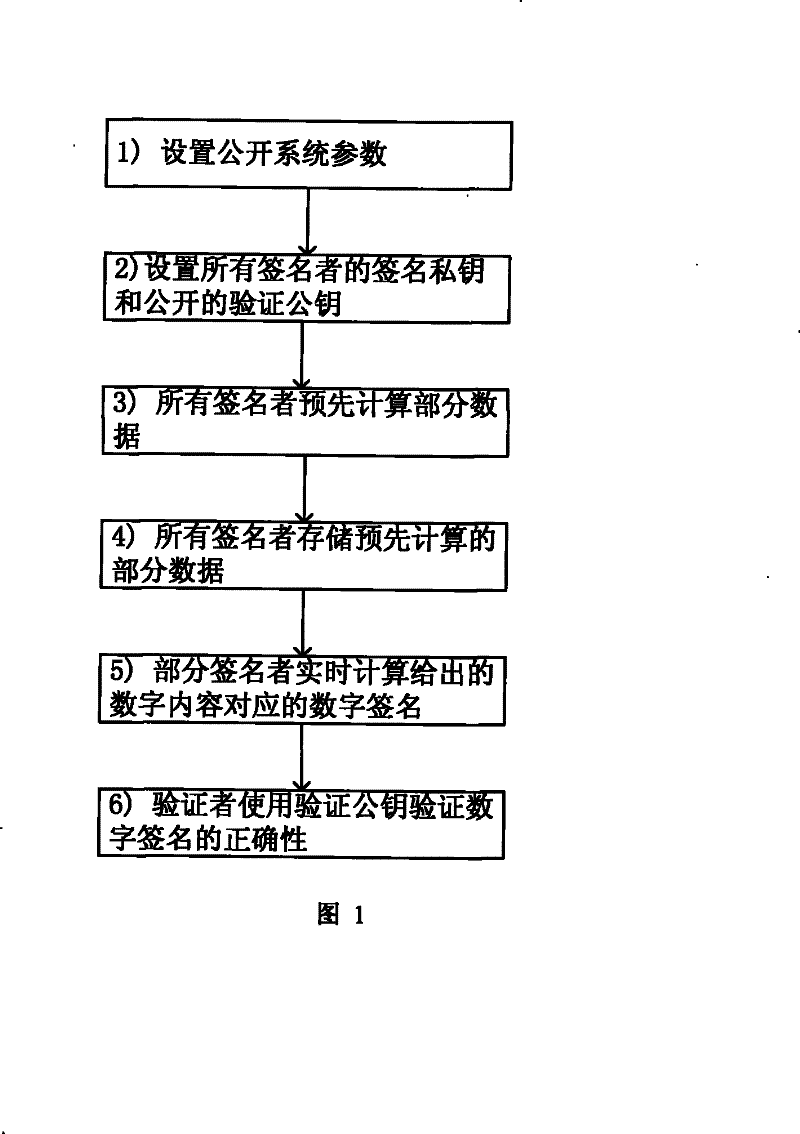
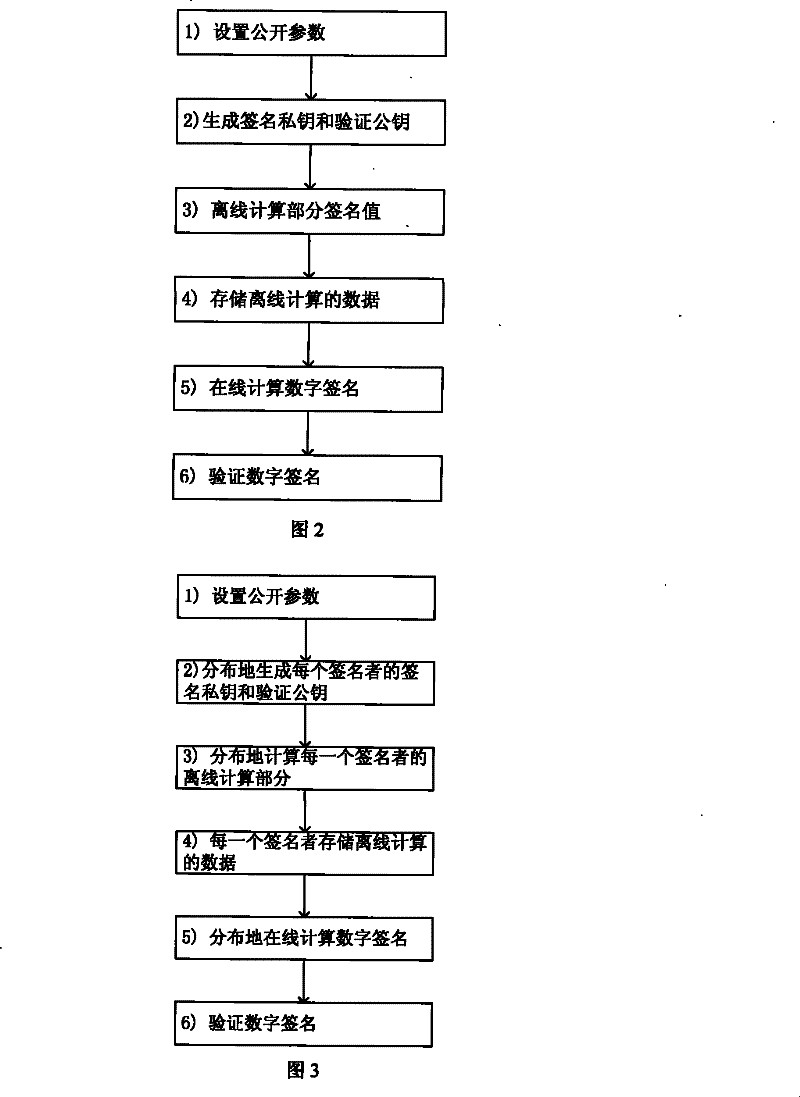
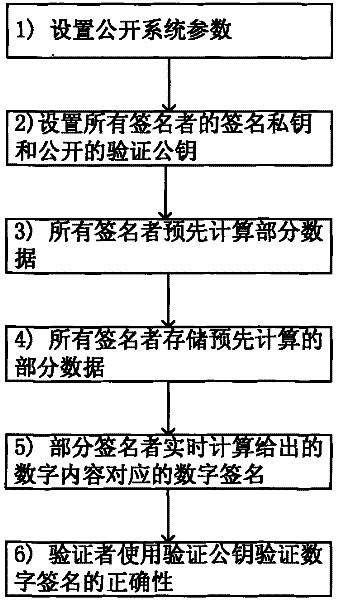
Method used
Image
Examples
Embodiment Construction
[0040] Taking the smart card as an example to illustrate the specific implementation of the digital signature scheme when n=1 and the safe storage area is 100 data pairs in the present invention.
[0041] 1. For the smart card implementing the digital signature scheme in the present invention, it is necessary to store the following public information {E, p, q, P, G, f, H, (JG, JS, JV), (VK, Y, h, σ) } and the following secret information {(SK, x, k * ), (k i , k i P), i ∈ {1...100}}
[0042] Among them, the public information (JG, JS, JV) is any provably secure digital signature algorithm, here selected as the Boneh-Lynn-Shacham short signature algorithm, the signature length is 160 bits, and the parameters of the signature algorithm (E, p, q, k, P, G) are suggested as follows:
[0043] E: y 2 =x 3 +3
[0044] Q=p=1461501624496790265145448589920785493717258890819
[0045] q=1461501624496790265145447380994971188499300027613
[0046] MOV degree k=12
[0047] P=(x,y)
...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap