Authentication implementing method and device
An implementation method and authentication technology, applied in the field of communication, can solve the problems of unsafe login, easy to steal of business accounts, etc., to achieve the effect of improving security and preventing easy to be stolen.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
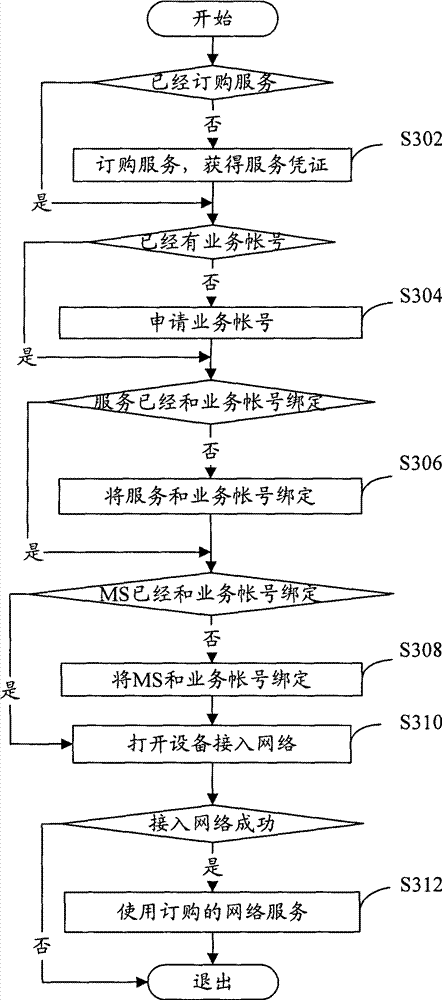
[0030] The preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
[0031] Functional Overview
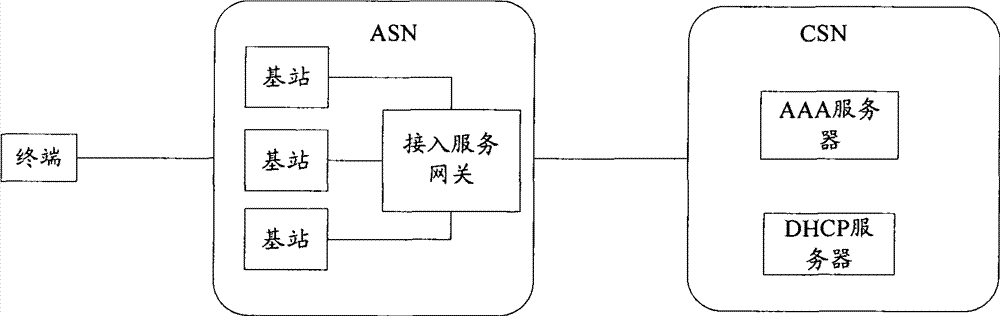
[0032] The main idea of the present invention is: the AAA (Authentication Authorization and Accounting, authentication, authorization and accounting) server identifies the MS through the binding of the MS (Mobile Station, mobile terminal) and the service account, and then through the binding of the service account and the service certificate The service ordered by the user is identified by establishing a relationship, and the AAA server assigns the corresponding service to the MS.
[0033] method embodiment
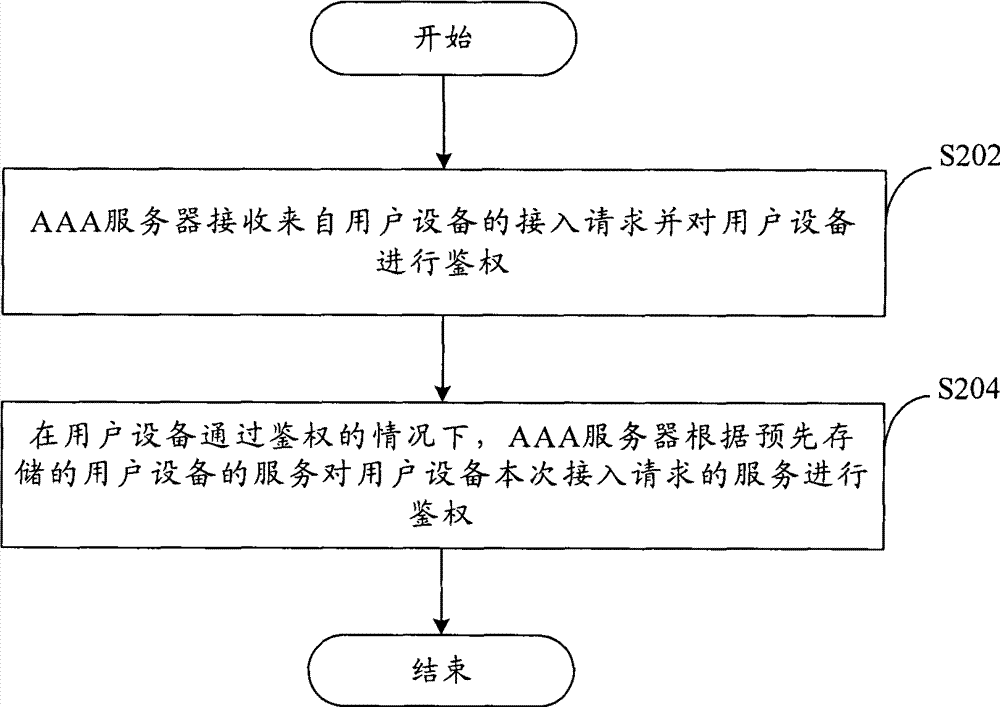
[0034] According to an embodiment of the present invention, an authentication implementation method is provided.
[0035] fig...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More