Method, system, device and terminal for processing secret keys
A processing method and key technology, which is applied to the public key and key distribution of secure communication, can solve the problems of reducing the network security of the access network, and achieve the effect of improving network security and avoiding repeated use
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
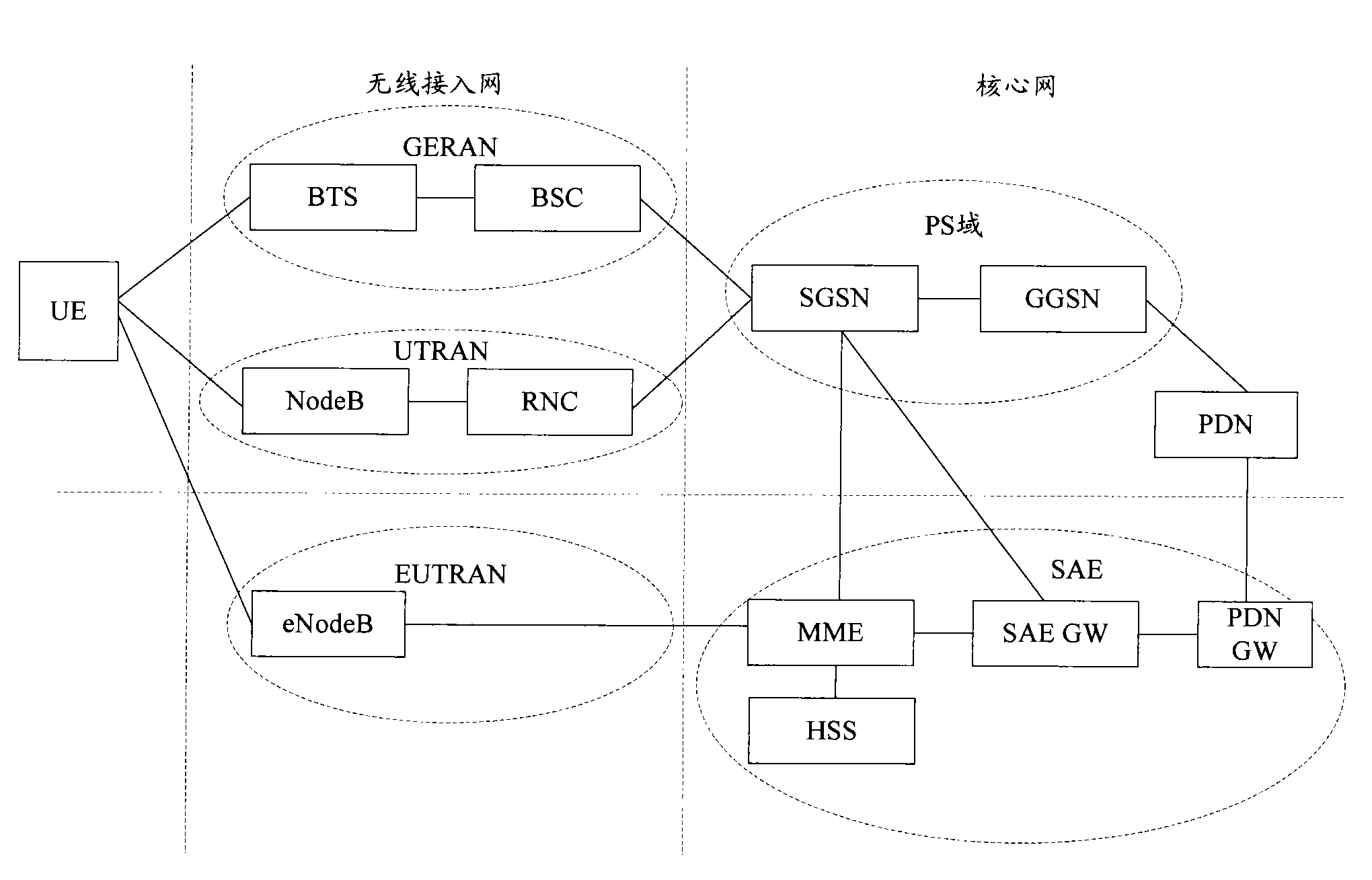
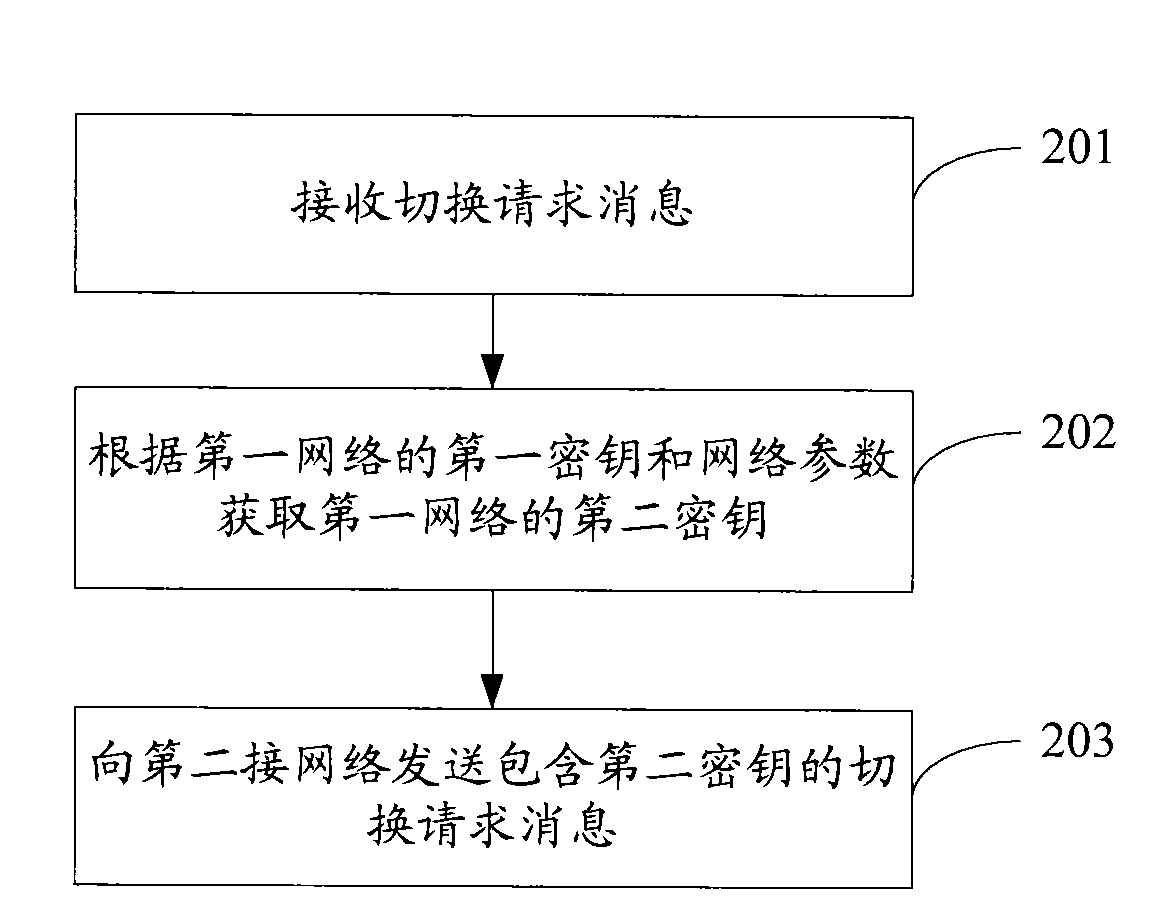
[0035] Embodiments of the present invention provide a key processing method, system, device, and terminal. On the network side, after receiving the handover request message, the second key of the first network is obtained according to the first key of the first network and network parameters, and is sent to the The second network sends a handover request message including the second key; the second network acquires the key of the second network according to the second key, and sends a handover request response message to the first network.
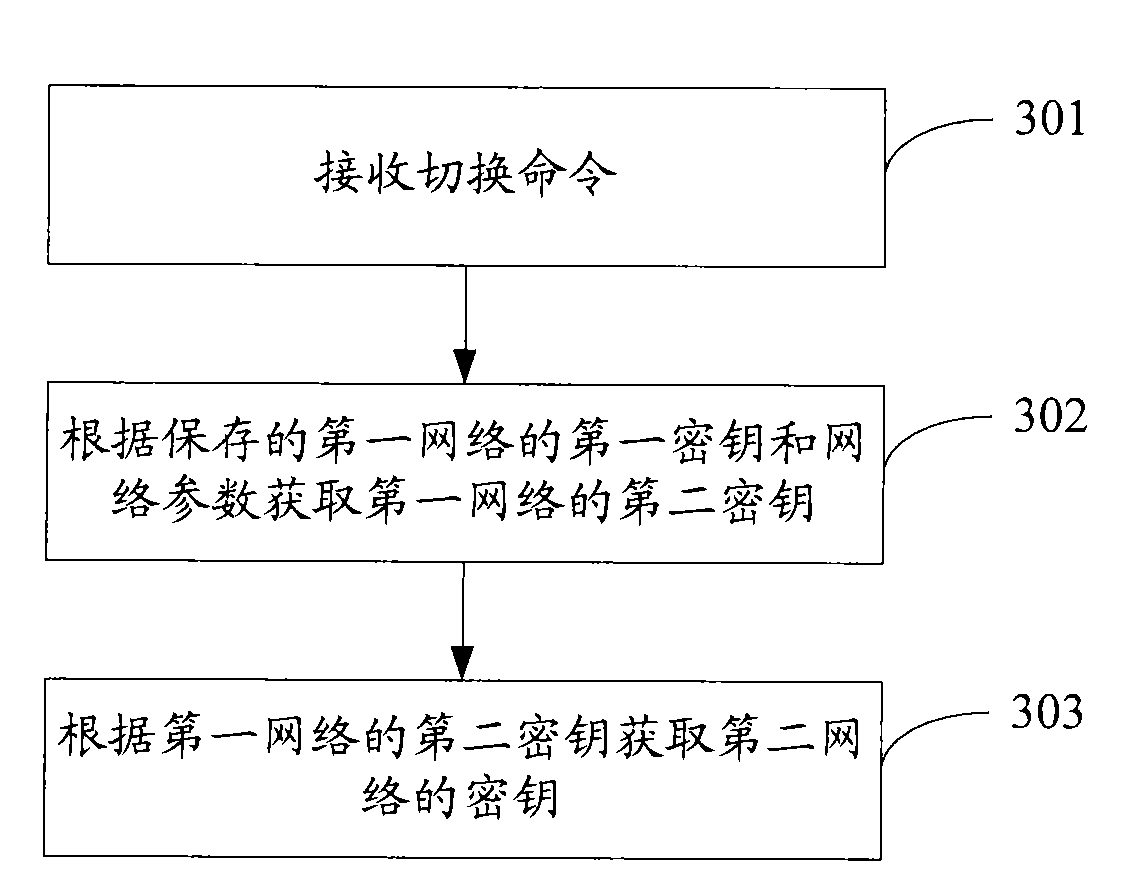
[0036] On the terminal side, after receiving the switching command, obtain the second key of the first network according to the saved first key and network parameters of the first network, and obtain the key of the second network according to the second key of the first network. In order to enable those skilled in the art to better understand the technical solutions provided by the embodiments of the present invention, the technical solutio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More