Security policy validation for web services
A web service and security technology, applied in the field of security policy verification of web services, can solve problems such as full SOA environment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
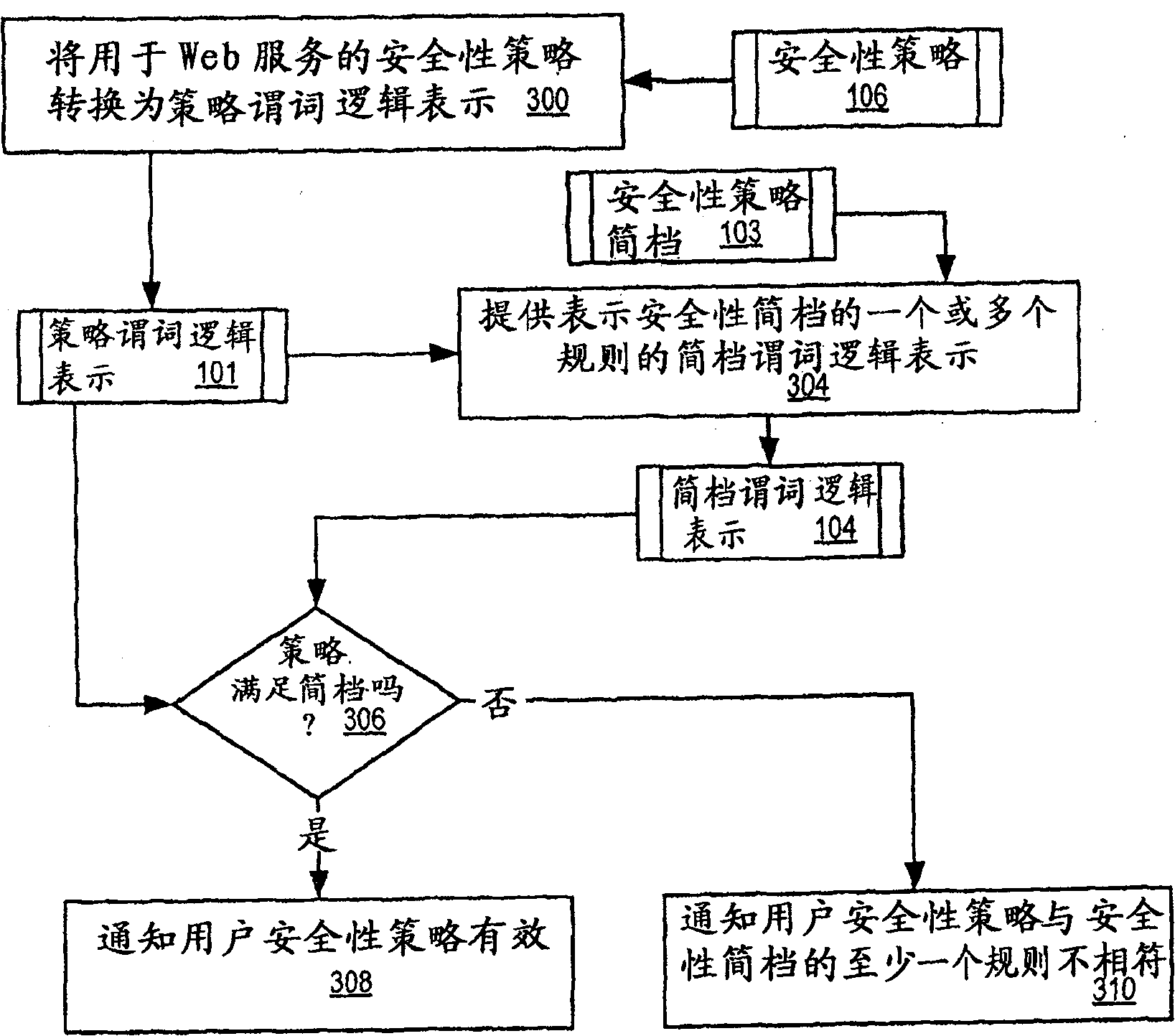
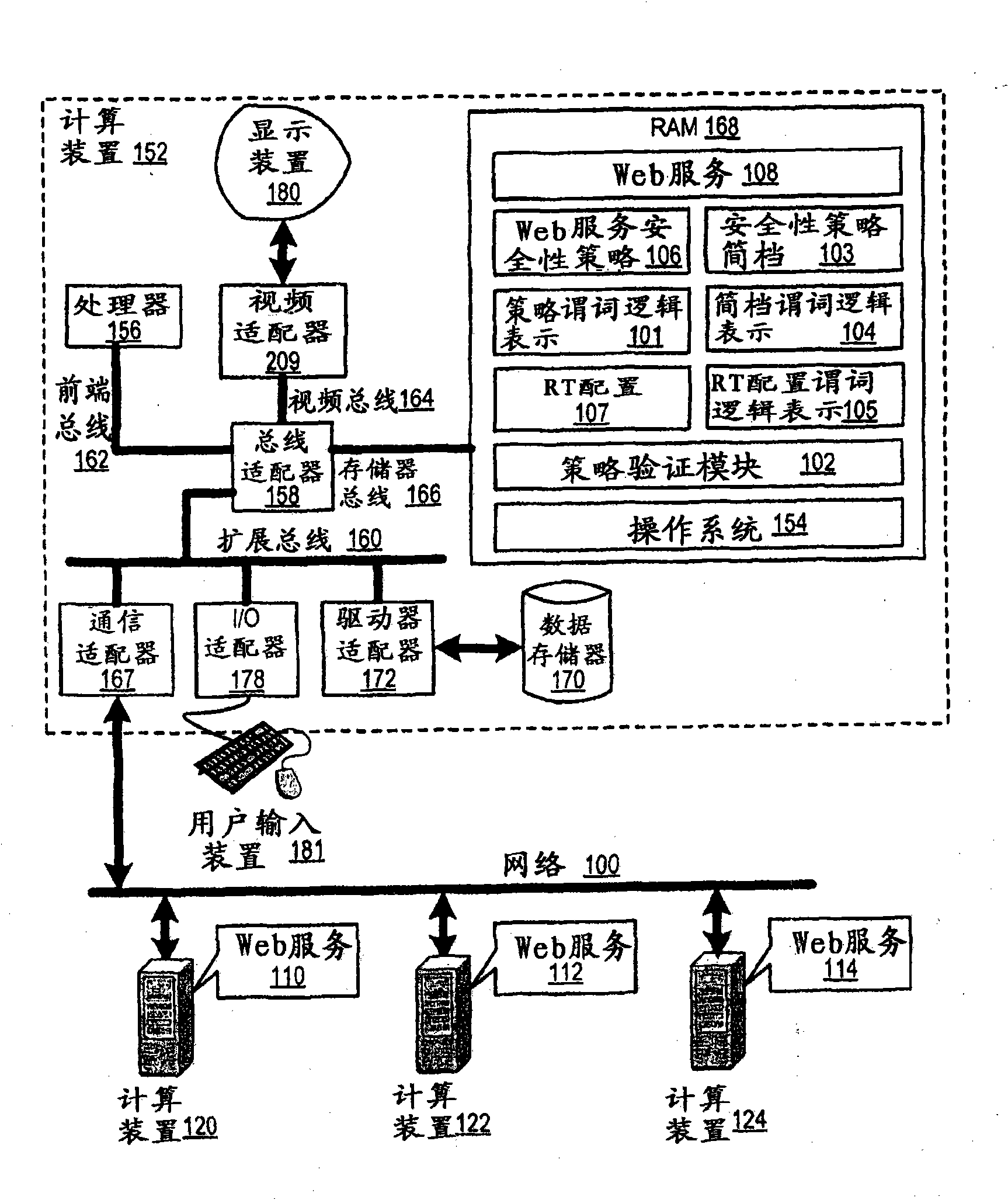
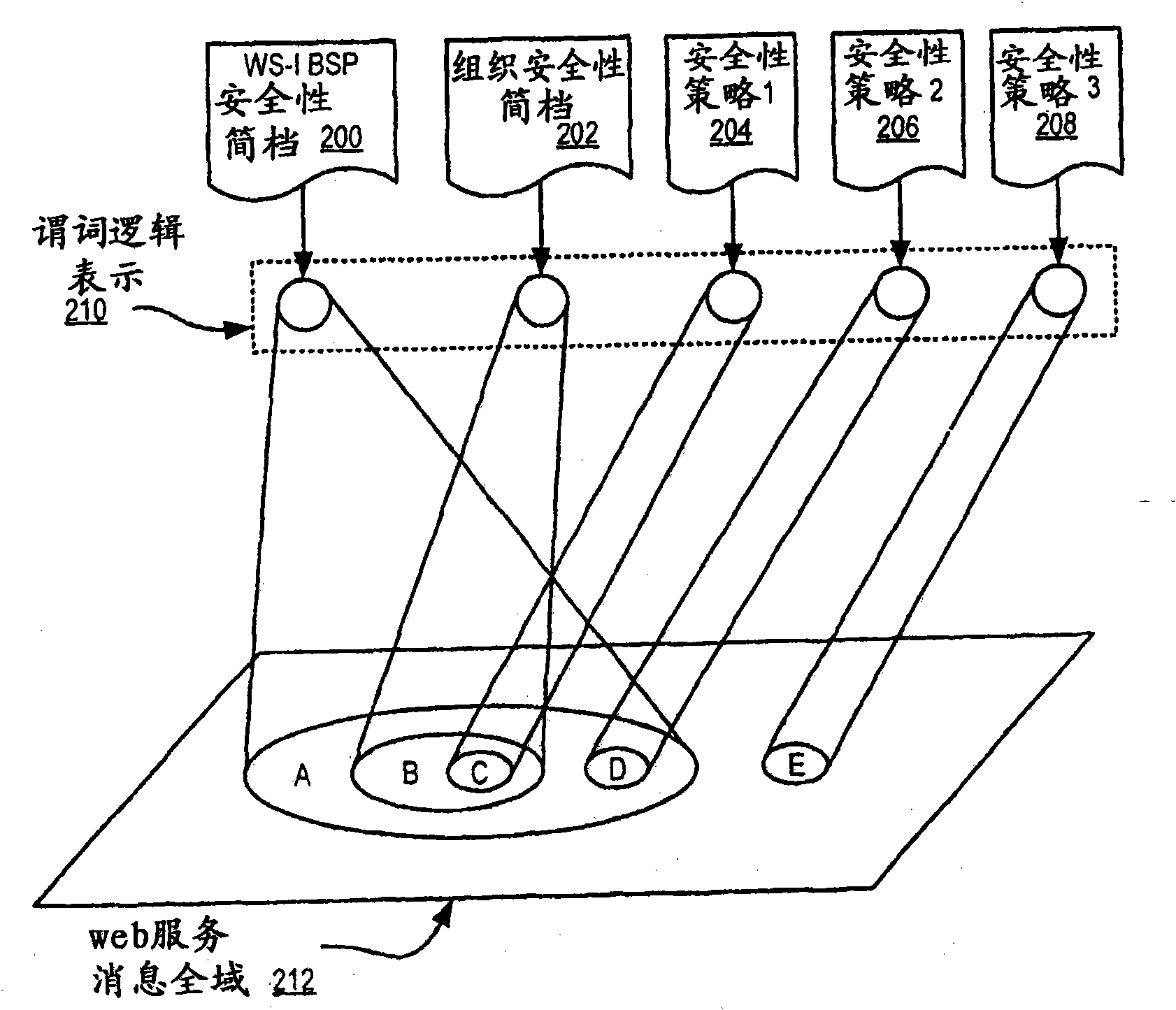
[0012] Starting from FIG. 1 , an exemplary method, device, and product for security policy verification of web services according to an embodiment of the present invention are described with reference to the accompanying drawings. FIG. 1 depicts a functional block diagram of an exemplary system capable of security policy validation for web services, according to an embodiment of the present invention. The exemplary system of FIG. 1 includes several computing devices (152, 120, 122, 124) connected together by a network (100) for data communication. A web service (108, 110, 112, 114) is installed on each computing device (152, 120, 122, 124), respectively. A web service is software designed to support interoperable machine-to-machine interactions over a network. Web services are frequently accessed over a network through a web application programming interface (API) and executed on a remote system that hosts the requested web service. APIs for web services are typically descri...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More