Method, device and system of data interception
A monitoring method and data technology, which is applied in the field of communication, can solve problems such as the inconvenient implementation of monitoring and increase the difficulty of system maintenance, and achieve the effect of simplifying the implementation of monitoring and reducing the difficulty of maintenance
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
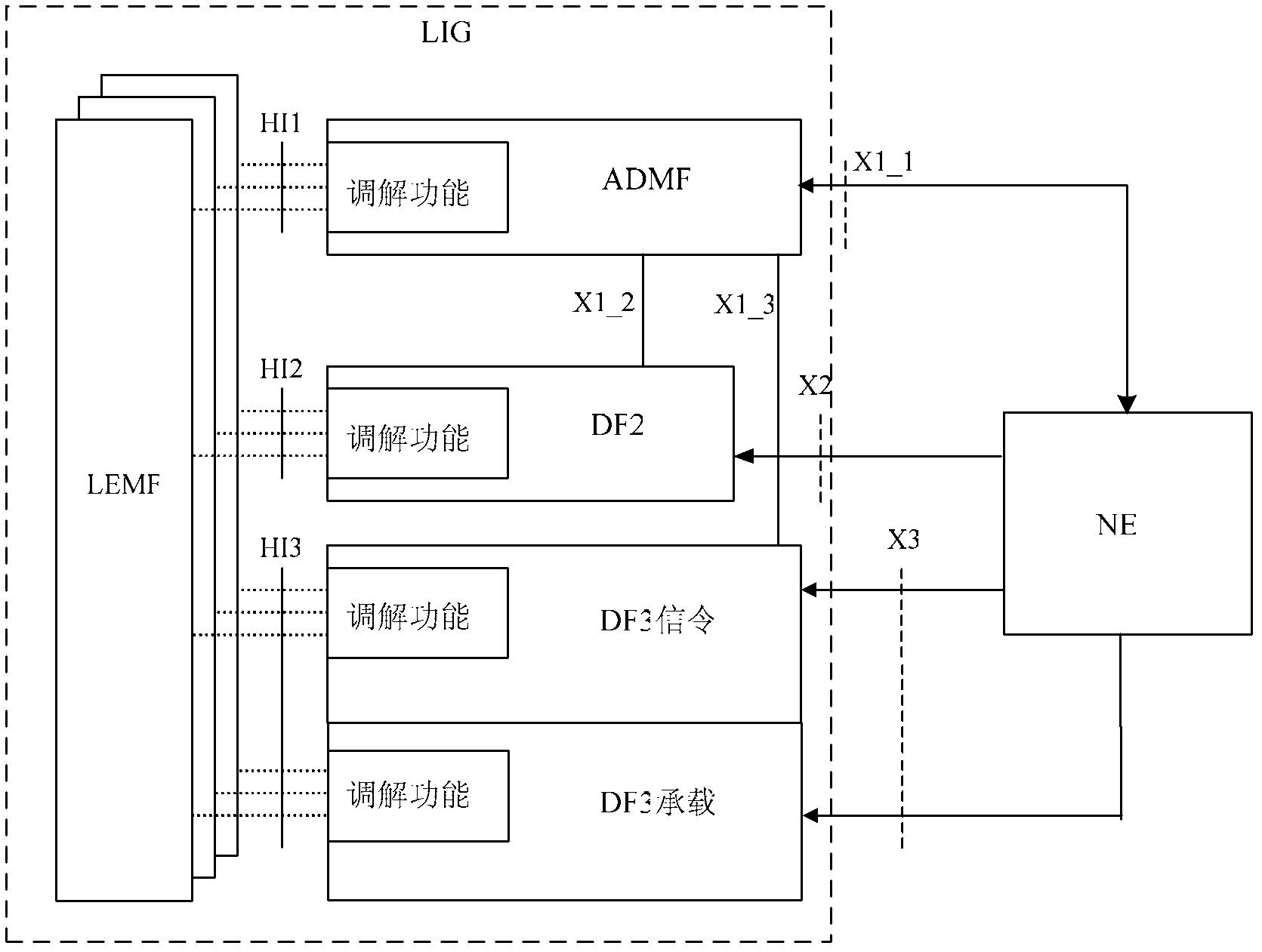
[0029] In this embodiment, a monitoring management node is introduced on the network element side, and the monitoring management node can be deployed on any network element on the network element side. In this embodiment, the network element on which the monitoring management node is deployed is called a monitoring management network. Yuan. That is, in this embodiment, one network element is configured as a monitoring management network element, and other network elements in the IMS are monitored and managed, and call-related messages reported by other network elements are merged into a set of unified call-related messages, so that the IMS Multiple network elements are virtualized into one network element, and only one network element is presented to the LIG, so that the LIG no longer merges the call-related information reported by each network element, and does not need to adapt and modify various monitoring services.
[0030] image 3 It is a flowchart of Embodiment 1 of th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More