Method and system for configuration protection group
A technology of protection group and configuration device, applied in the field of communication, can solve the problem of complicated operation of configuring protection group, and achieve the effect of simplifying the configuration operation of protection group
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
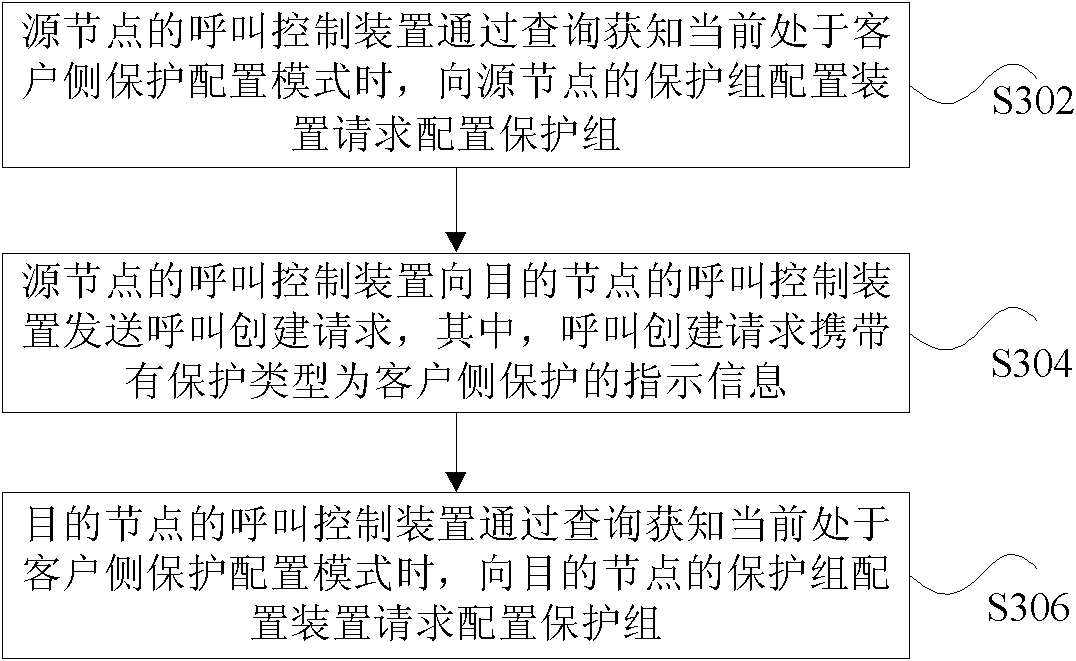
[0022] image 3 is a flowchart of a method for configuring a protection group according to an embodiment of the present invention. Such as image 3 As shown, the method for configuring a protection group mainly includes the following processing:
[0023] Step S302: When the call control device of the source node learns that it is currently in the client-side protection configuration mode through inquiry, it requests the protection group configuration device of the source node to configure a protection group;
[0024] Step S304: The call control device of the source node sends a call creation request to the call control device of the destination node, wherein the call creation request carries infor...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More