Authentication and key negotiation method, and authentication method, system and equipment
一种认证方法、设备的技术,应用在认证技术领域,能够解决无法抵抗重放攻击等问题
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0057] In order to make the purpose, technical solution and advantages of the present invention clearer, the following will further describe the implementation of the present invention in detail in conjunction with the accompanying drawings.
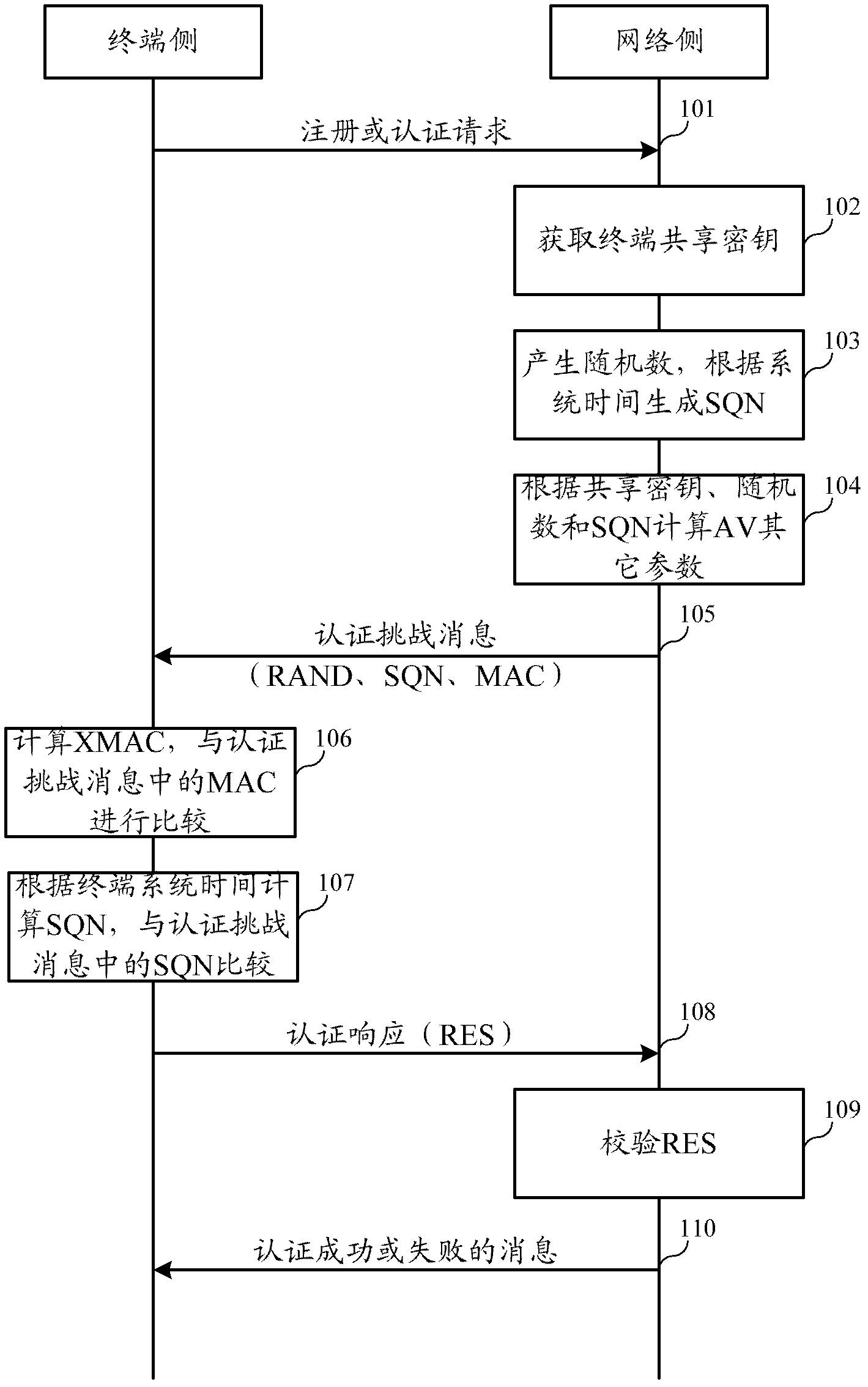
[0058] The first embodiment of the present invention relates to an authentication and key agreement AKA method. Compared with the existing AKA, the biggest difference between the two lies in the different SQN parameter setting methods. In the existing AKA, SQN is a counter concept. Both the user side and the network side maintain a counter and ensure synchronization. The user terminal can send the counter value (ie SQN) from the network side and the locally maintained counter value ( SQN) is consistent to determine whether the network device sending the SQN is legal. This method requires a user to uniformly maintain a SQN. When the SQN is stored on the user card, no matter how many terminals the user changes, the SQN can be maintained u...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More