Website abnormal access behavior detection method based on visual analysis
A detection method and behavior technology, applied in the field of network security visual analysis, to achieve high efficiency and clear effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
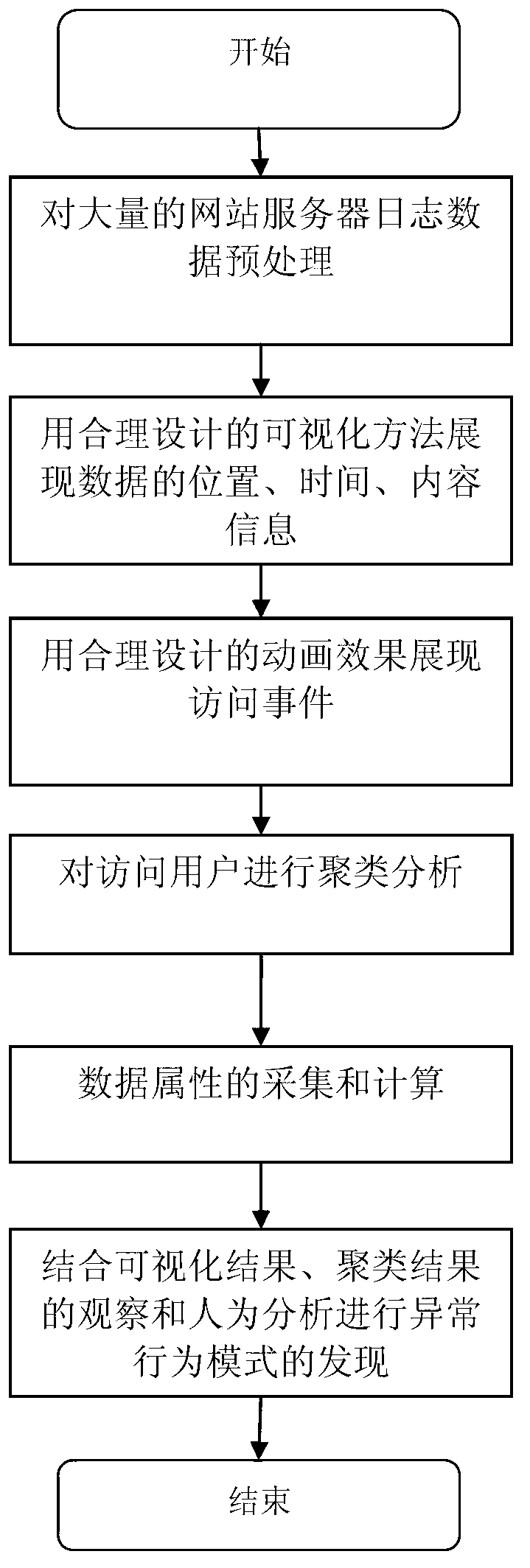
[0037] The invention proposes a method for analyzing and discovering website attack patterns based on visual analysis, and at the same time provides cluster analysis of malicious users and reproduction of attack behaviors. Through effective visualization methods and cluster analysis based on different parameters, this method enables users to find out malicious users in the iterative process of discovery, data mining, and discovery, and vividly reproduces the behavior of malicious users through animation. According to this method, the inventor has established a set of computer software system, which can efficiently analyze website log data, find several specific attack modes, find malicious users, and automatically recommend the corresponding ones according to the behavior characteristics of malicious users. Other users with similar behavior patterns of this user can intuitively display the information contained in the website logs and show the behavior patterns of website visit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More