A detection method and device for malicious detection behavior
A behavioral and malicious technology, applied in the computer field, can solve problems such as poor detection results, false positives, and computer infection with Trojan horse viruses
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
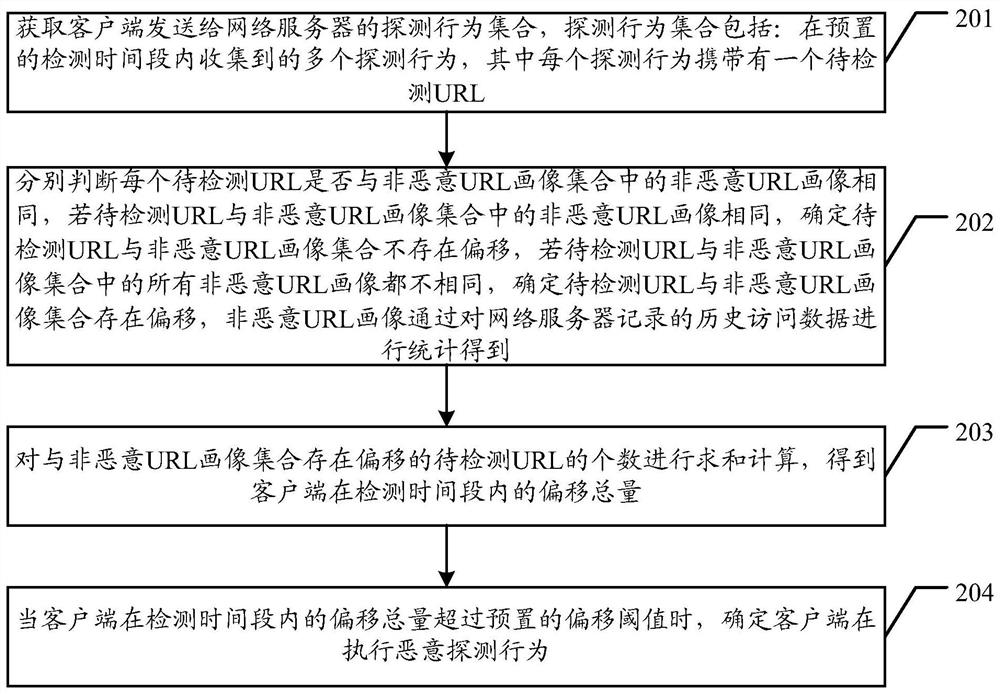
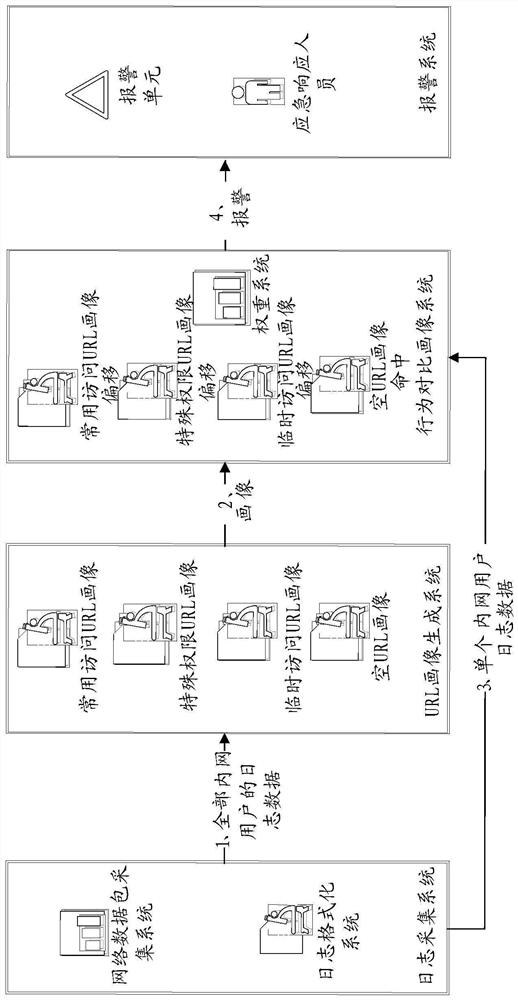
[0033] Embodiments of the present invention provide a detection method and device for malicious detection behaviors, which are used to effectively solve the detection problem of malicious detection behaviors and improve the detection effect of malicious detection behaviors.
[0034] In order to make the purpose, features and advantages of the present invention more obvious and understandable, the technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the following The described embodiments are only some, not all, embodiments of the present invention. All other embodiments obtained by those skilled in the art based on the embodiments of the present invention belong to the protection scope of the present invention.
[0035] The terms "comprising" and "having" in the description and claims of the present invention and the ab...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More