Access control method of network security group and security computer
A security computer and network security technology, applied in the access control method of security group and security computer field, can solve the problem of low efficiency of access control of network security group, and achieve the effect of improving the efficiency of access control
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0063] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
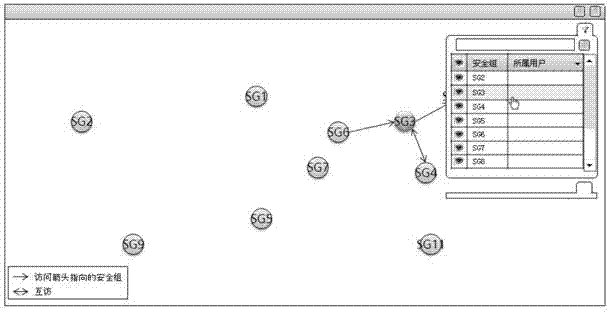
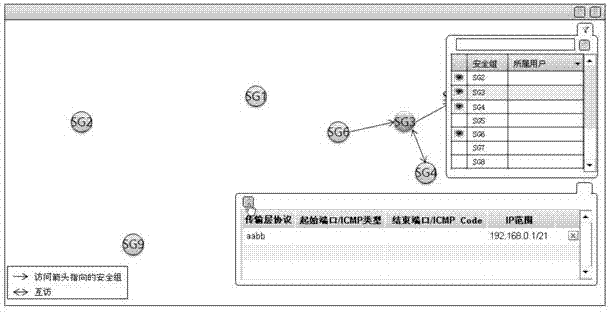
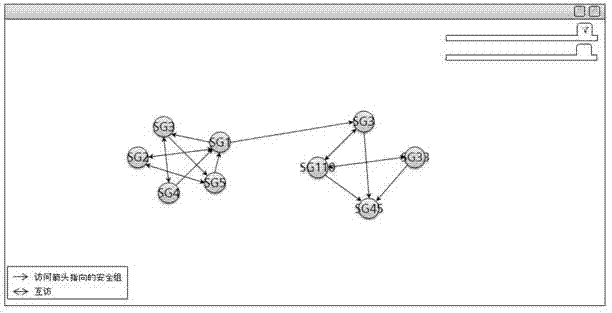
[0064] In the embodiment of the present invention, all network security groups in the system are output in the same human-computer interaction interface, the user's mouse drag operation in the human-computer interaction interface is detected, and the initial position corresponding to the mouse drag operation is established. The access relationship between the network security group and the network security group corresponding to the end position, so that users can quickly, accurately and efficiently establish the access control relationship between network security groups from a global perspective, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More