Method for NTRU-type fully-homomorphic encryption on LWE circle
A fully homomorphic encryption and ciphertext technology, applied in the field of encryption, can solve the problems of long ciphertext, poor encryption efficiency, poor efficiency, etc., and achieve the effect of short ciphertext and high encryption efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] The present invention will be further described below with regard to specific embodiments.
[0033] The fully homomorphic encryption method of NTRU type on the ring LWE of the present invention comprises the following steps:
[0034] 1. Define parameters:
[0035] For an integer q, define Encryption is in and R q =R / qR, where φ(x)=χ n +1 is a circular polynomial, n is a power of 2, q is a prime number and
[0036] If the polynomial f∈R satisfies ||f|| ∞ ≤ B, then f is said to be B-boundary;
[0037] {χ n}(n∈N) is a distribution set on R, if for any f←χ n Both ||f|| ∞ ≤ B, then it is called {χ n} is the B-boundary distribution, that is, a B-boundary distribution on R outputs a B-boundary polynomial;
[0038] Gaussian distribution has the following properties: for any real number Have:
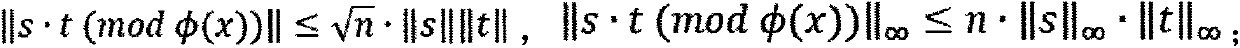
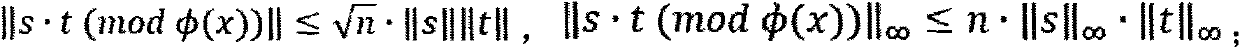
[0039] ring The product of the above elements has the following properties: | | s · t ( ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More