Access control method and system in cloud computing system
An access control and cloud computing technology, which is applied in the transmission system, electrical components, data exchange through path configuration, etc., can solve the problems of aggravating the security of cloud computing applications and the impact of information services
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0063] In order to make the purpose, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined arbitrarily with each other.
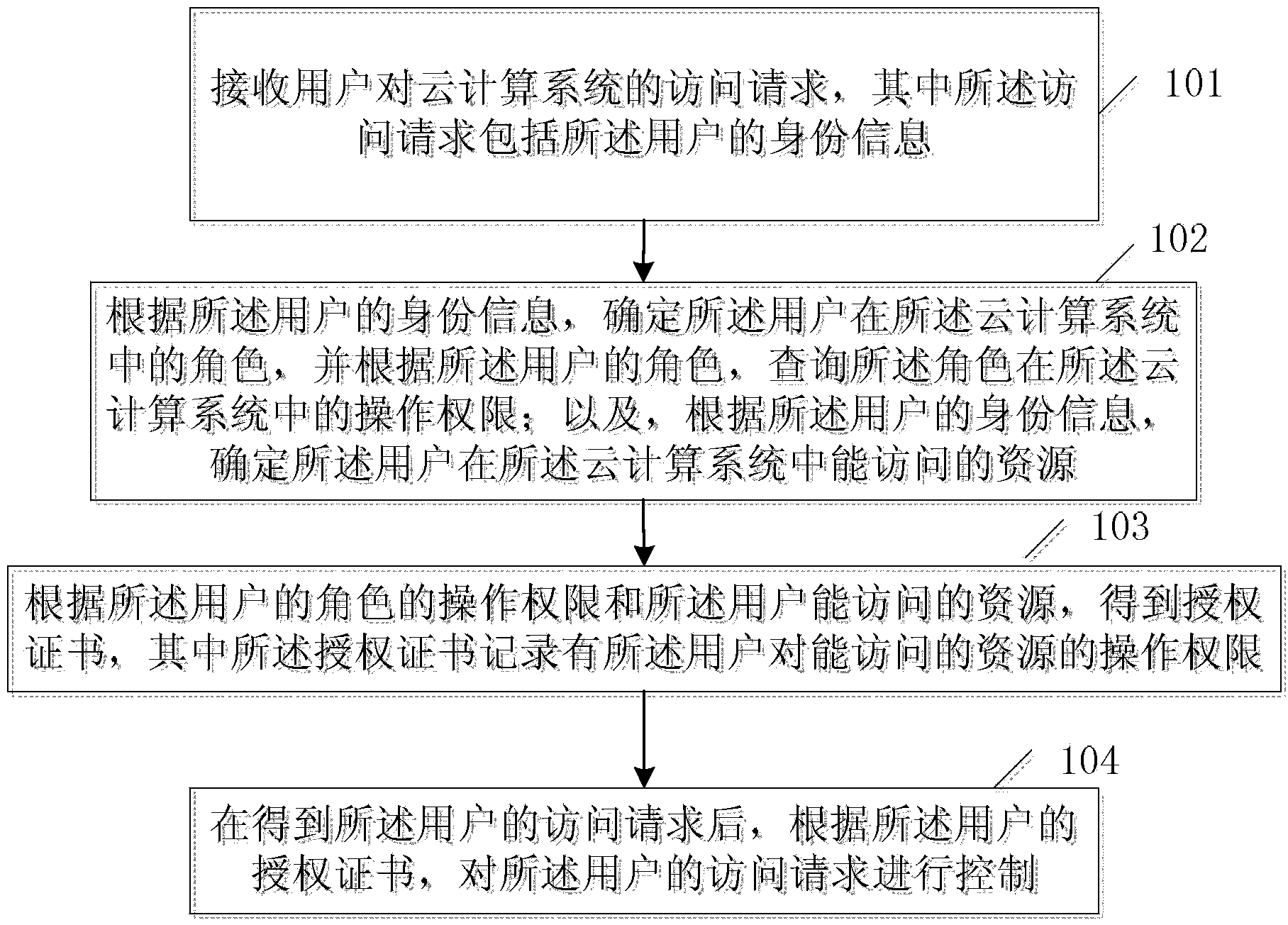
[0064] figure 1 It is a schematic flowchart of an embodiment of a method for access control in a cloud computing system provided by the present invention. figure 1 Embodiments of the methods shown include:
[0065] Step 101, receiving a user's access request to the cloud computing system, wherein the access request includes the user's identity information;
[0066] The user's identity information may be the user's name or ID information.
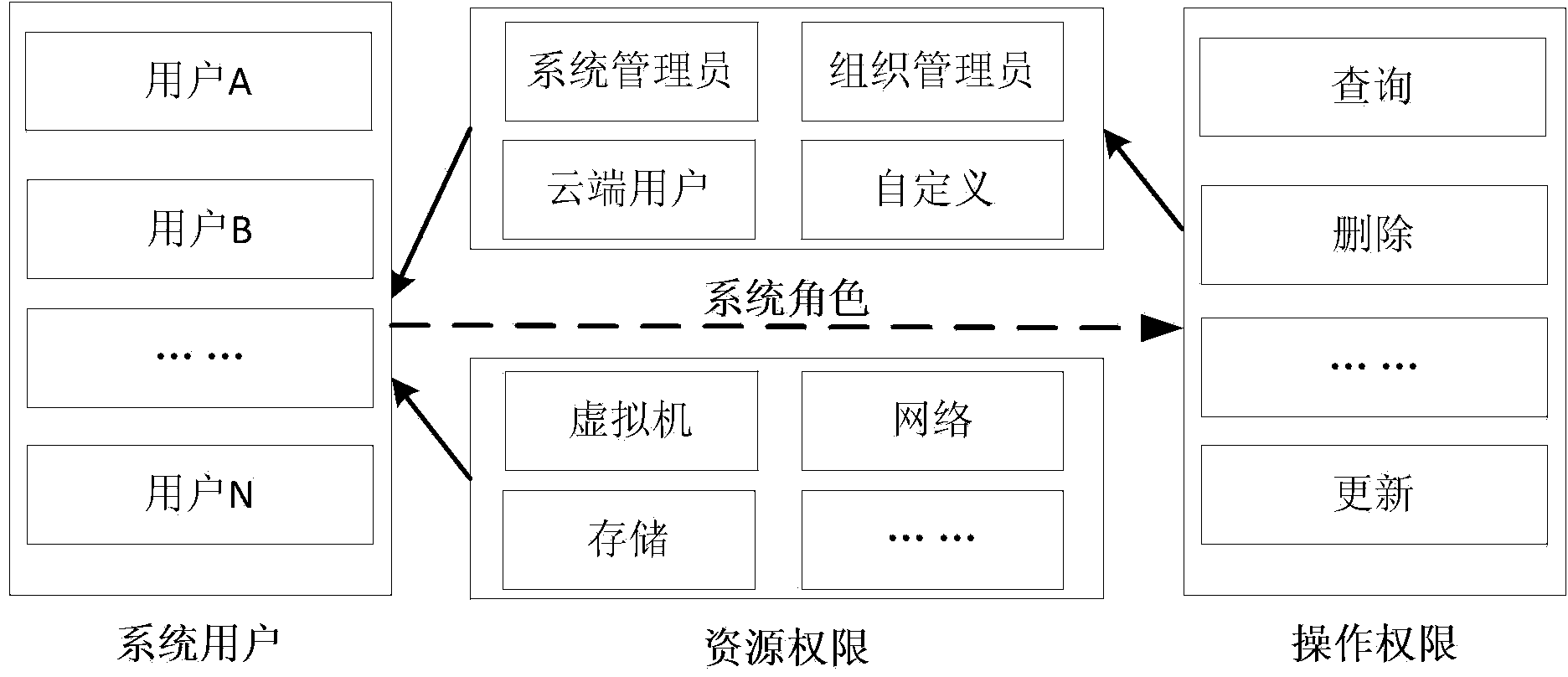
[0067] Step 102: Determine the user's role in the cloud computing system according to the user's identity information, and q...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com