Low-bitrate denial of service attack method based on data flow
A denial-of-service attack and data flow technology, applied in the direction of data exchange network, digital transmission system, electrical components, etc., can solve the problems of users sending data packets, unable to process data packets, data packet processing, etc., to achieve flexible attack process and improve The difficulty of detection and the effect of short statistical time slices
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
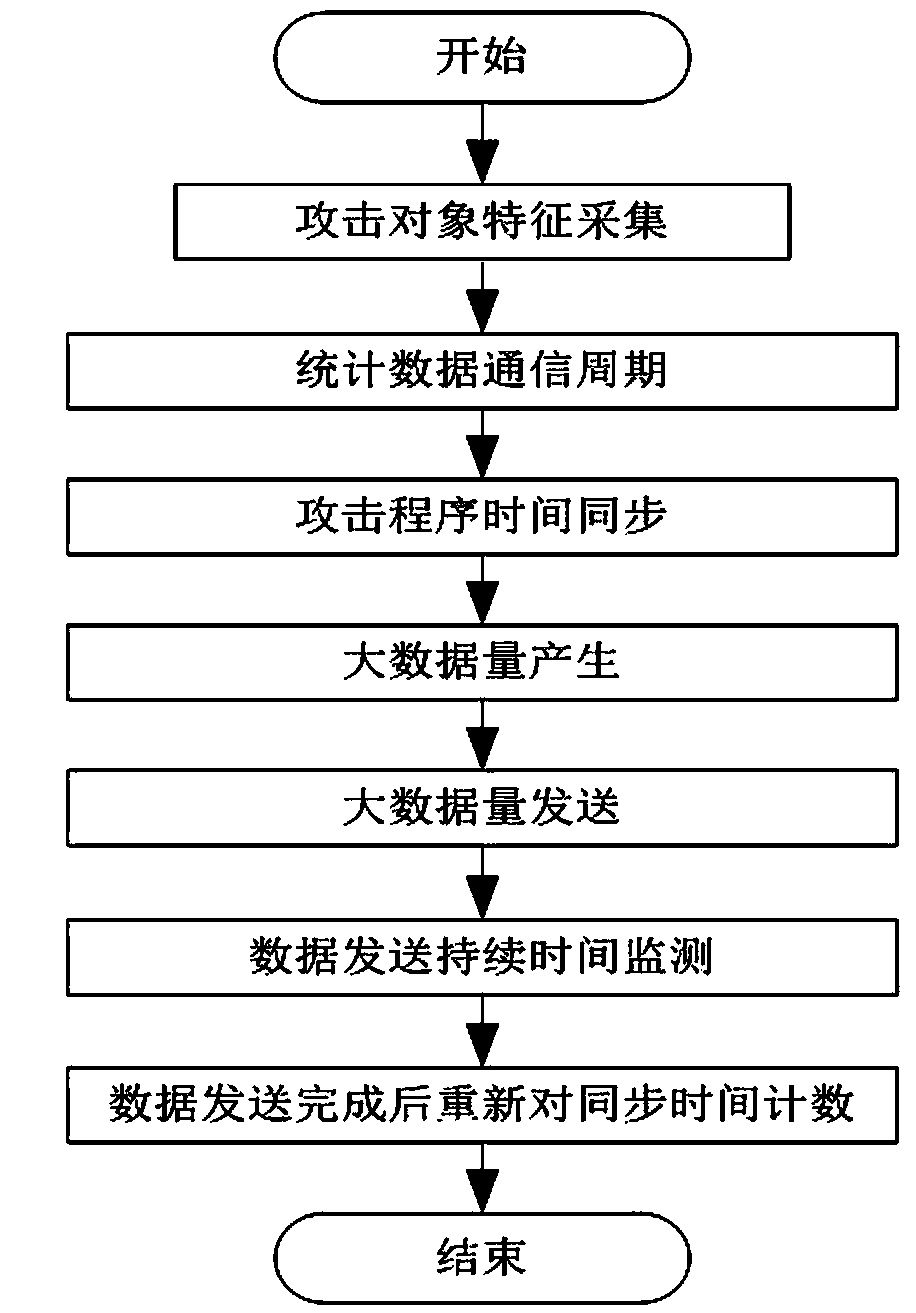
[0016] Low-rate denial-of-service attacks against applications with fixed communication cycles;
[0017] (1) Monitor the communication rules of the target application program on the network, and record the fixed communication cycle of the target application program;
[0018] (2) When it is necessary to carry out a low-rate denial-of-service attack against the application, first establish a synchronization relationship with a communication data packet of the application;
[0019] (3) The denial-of-service attack program periodically sends out denial-of-service attack data in accordance with the synchronized time node and the previously recorded time period;
[0020] (4) The denial-of-service attack process is completely aimed at the application program with a fixed communication cycle.
Embodiment 2
[0022] An example of an application denial of service attack targeting irregular communication cycles.
[0023] (1) Analyze the communication rules of the target application program, and determine that the application program is an application program with an irregular communication cycle;
[0024] (2) When it is necessary to carry out a denial of service attack against the application, first monitor the characteristics of the application, IP address, port number or some identifying fields in the data packet on the network;
[0025] (3) When the special identifier of the target application program appears on the network, an instant low-rate denial of service attack data is launched on the network;
[0026] (4) After the denial-of-service attack program sends data, continue to monitor the communication data flow on the network, and continue to initiate low-rate denial-of-service attack data until a new special identifier of the application is found.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More