Method for attacking elliptical curve encryption algorithm and attacking device
An elliptic curve encryption and attack device technology, applied in the field of information security, can solve the problems of difficult to control the timing of error injection, injection errors, and low attack efficiency.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0078] In order to facilitate the understanding of those skilled in the art, the present invention will be further described below in conjunction with the accompanying drawings, which cannot be used to limit the protection scope of the present invention. It should be noted that, in the case of no conflict, the embodiments in the present application and various manners in the embodiments can be combined with each other.
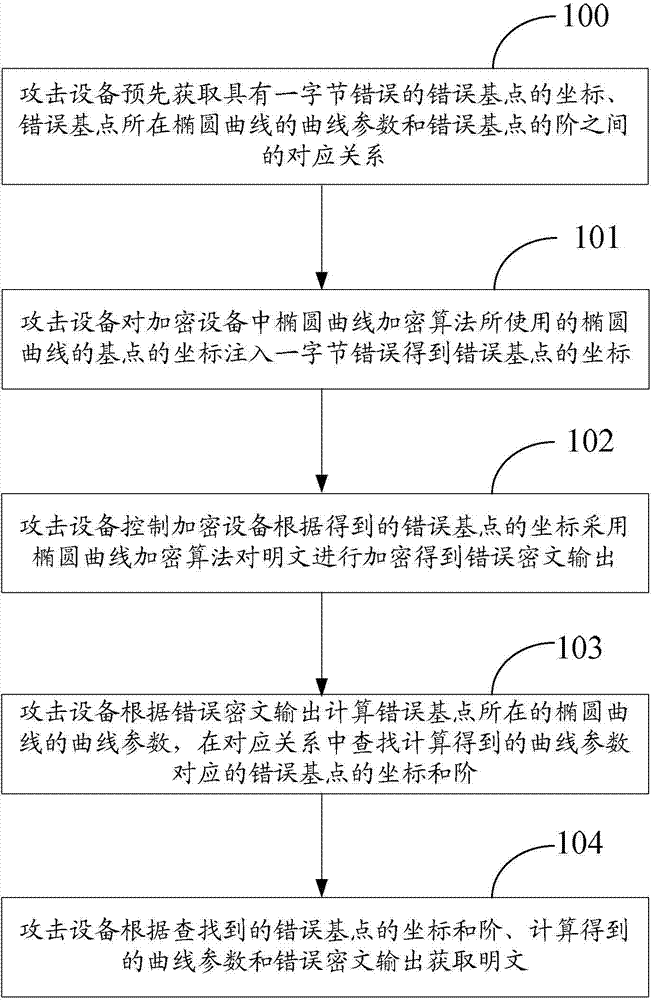
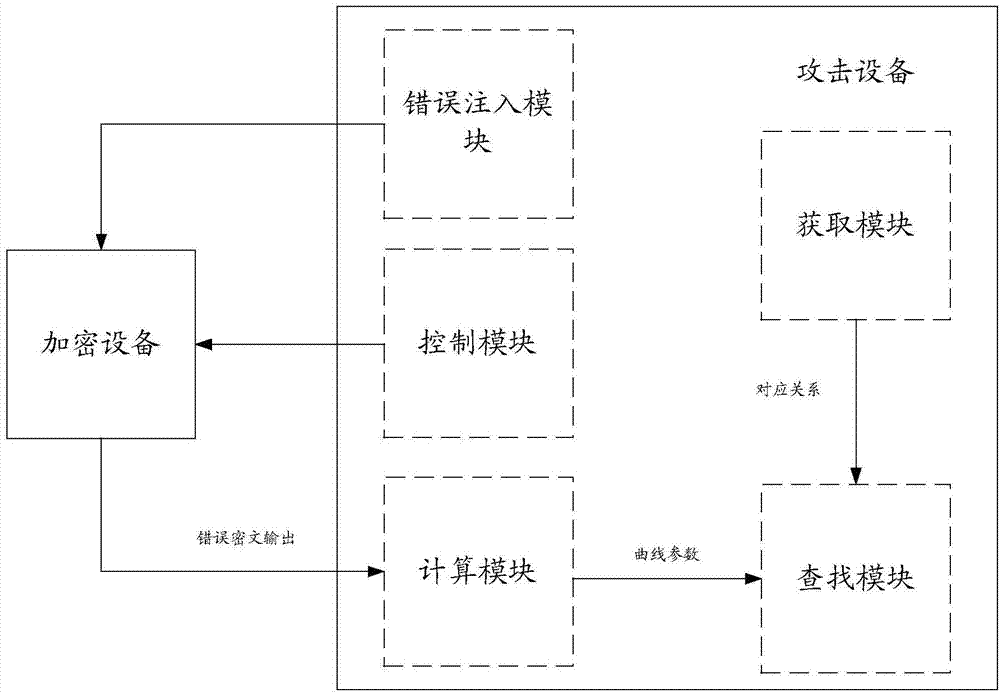
[0079] see figure 1 , the present invention proposes a method of attacking the elliptic curve encryption algorithm, comprising:
[0080] Step 100, the attacking device obtains in advance the correspondence between the coordinates of the wrong base point with a one-byte error, the curve parameters of the elliptic curve where the wrong base point is located, and the order of the wrong base point.
[0081] In this step, the order is the order in which the length of the largest prime factor is less than or equal to a preset threshold.
[0082] In this step, the ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More