Electronic medical record signature method and device
An electronic medical record and electronic signature technology, which is applied to secure communication devices, electrical components, user identity/authority verification, etc. sexual effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
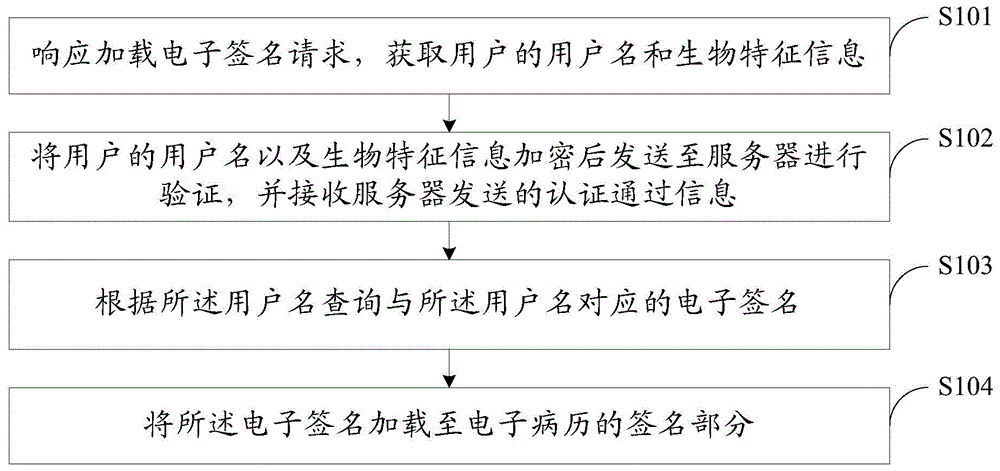
[0063] see figure 1 , which is a flow chart of Embodiment 1 of an electronic medical record signature method provided by the present invention.
[0064] The electronic medical record signature method provided by this embodiment is applied to the client, and the method includes the following steps:
[0065] Step S101: Responding to the upload electronic signature request, obtain the user's username and biometric information.
[0066] In practical applications, when the user finishes editing the electronic medical record, he needs to click the electronic signature load button in the electronic medical record to load the electronic signature. After receiving the upload electronic signature request sent by the user, the client obtains the user's username and biometric information. The user needs to log in to the electronic medical record system before opening the electronic medical record. If the user uses a user name to log in, the user name can be directly extracted from the s...
Embodiment 2
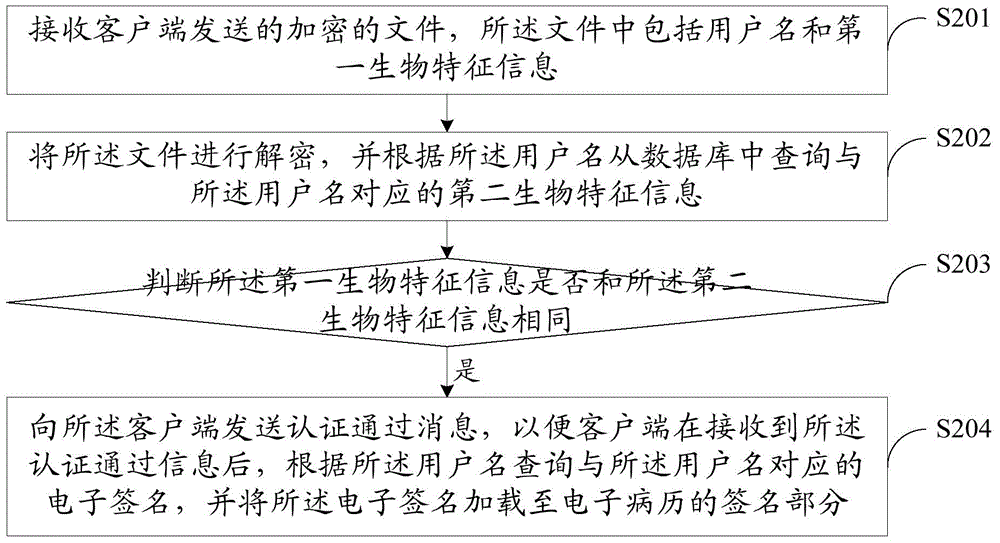
[0088] see figure 2 , which is a flow chart of Embodiment 2 of an electronic medical record signature method provided by the present invention.
[0089] The electronic medical record signature method provided by this embodiment is applied to the server, and the method includes the following steps:
[0090] Step S201: Receive the encrypted file sent by the client, the file includes the user name and the first biological feature information.
[0091] In this embodiment, the biological characteristics refer to the unique physiological characteristics that everyone has, such as fingerprints, palmprints, faces, voices, irises, retinas, and the like. Utilizing the biometric feature for authentication is not only convenient, the user does not need to memorize the password like the prior art 1, nor does it need to carry a U-shield like the prior art 2, and it is safe and reliable, not easy to be stolen, let alone will be lost. Among all kinds of biometric information, since each p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More