Application hosting within a secured framework in a fueling environment
A safety and security technology that addresses increased security risks in applications such as coin-free or similar appliances, coin-operated devices for controlling the dispensing of fluid/particulate materials from containers, software for automated teller machines, etc. And other issues
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0020] Reference will now be made in detail to various aspects, one or more examples of which are illustrated in the accompanying drawings. Each example is provided by way of explanation, not limitation. In fact, those skilled in the art will recognize that modifications and variations can be made to the aspects described without departing from the scope or spirit thereof. For example, features illustrated or described as part of one example can be used on another example to yield yet a further example. Thus, it is intended that the described aspects cover such modifications and variations as come within the scope of the appended claims and their equivalents.
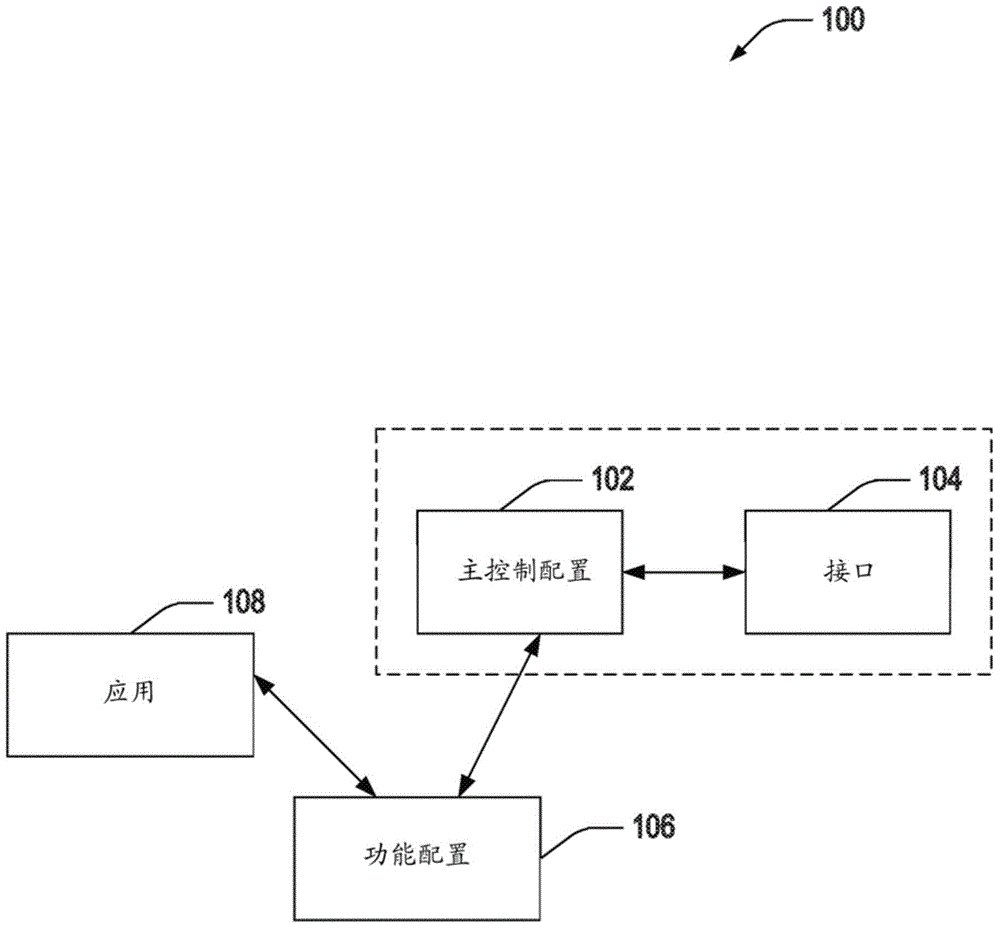
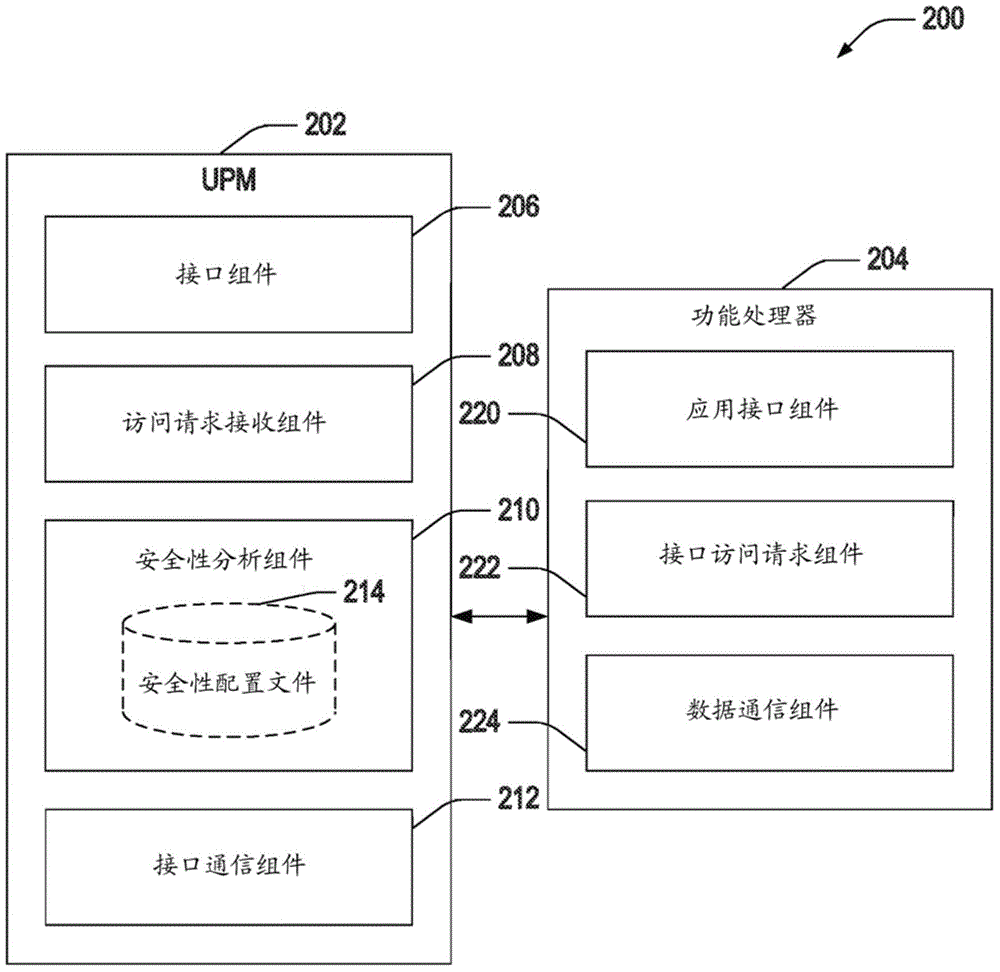
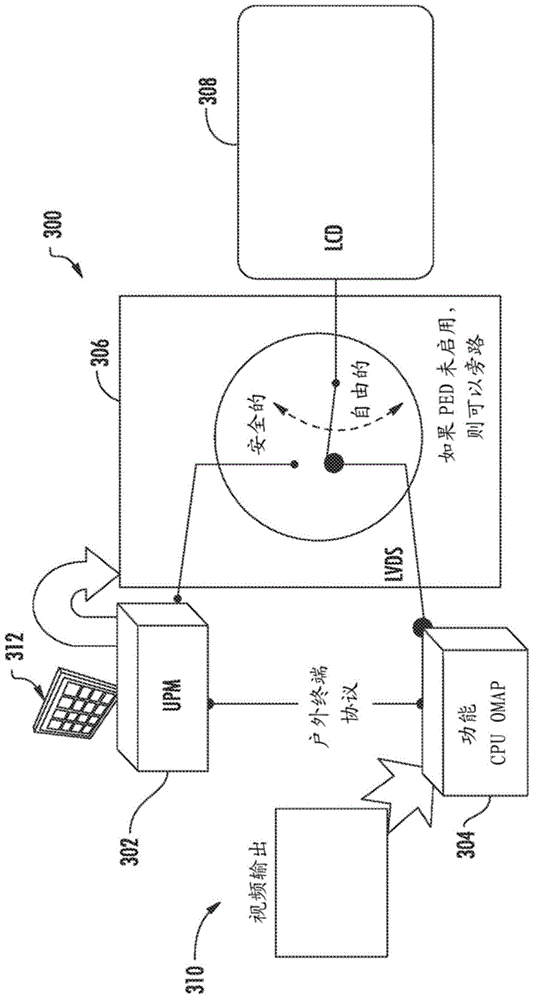
[0021] Described herein are various aspects related to hosting secure and non-secure applications in a secure framework. The framework includes at least one control master configuration as a hardware configuration in which the security application can be executed. Controlling the access of unsafe applications execute...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More