Malicious program sample classification method and device
A malicious program and classification method technology, applied in computer security devices, instruments, calculations, etc., can solve the problem of low accuracy of clustering methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0049] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the embodiments of the present invention will be further described in detail below in conjunction with the accompanying drawings. Here, the exemplary embodiments of the present invention and their descriptions are used to explain the present invention, but not to limit the present invention.
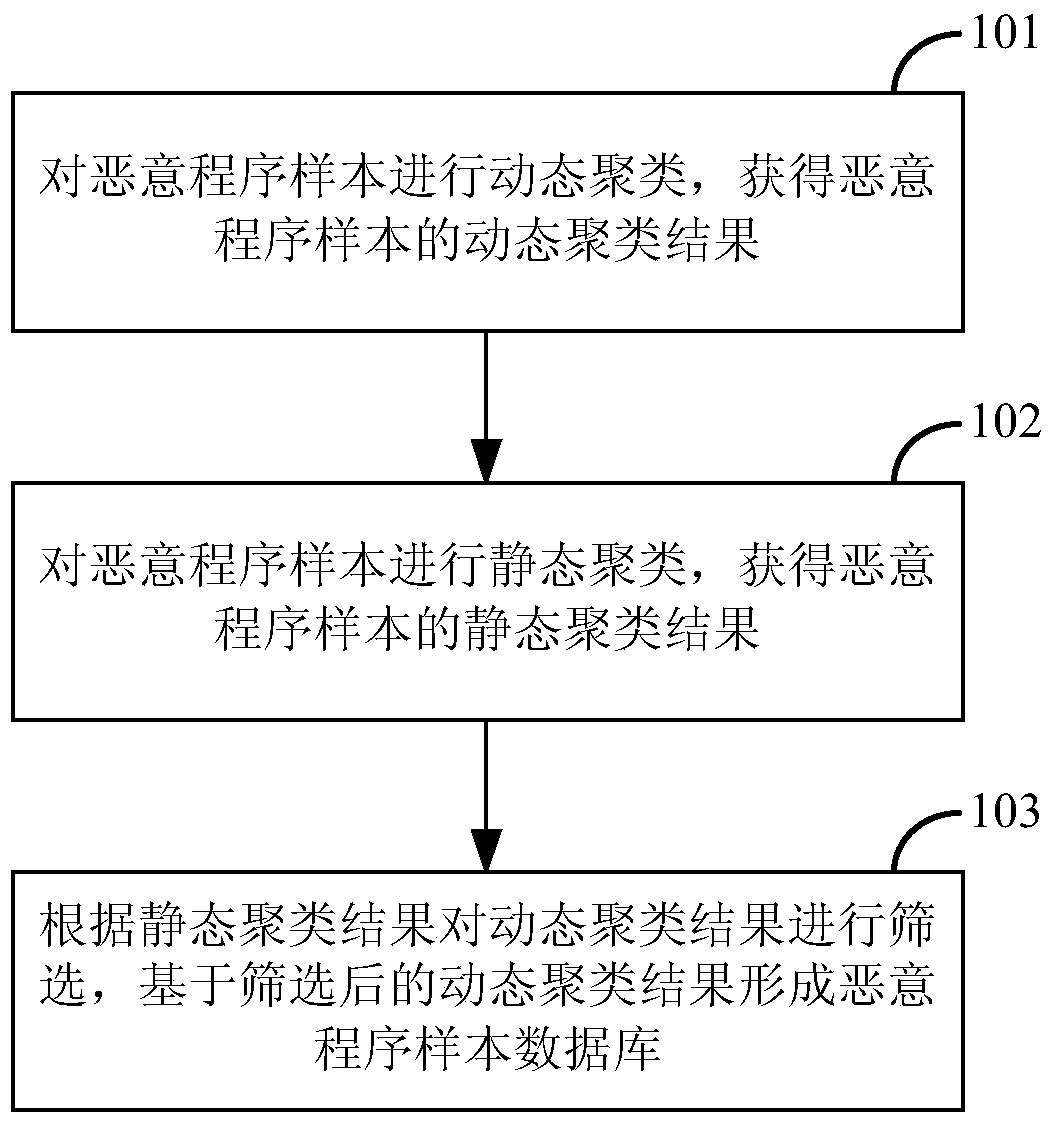
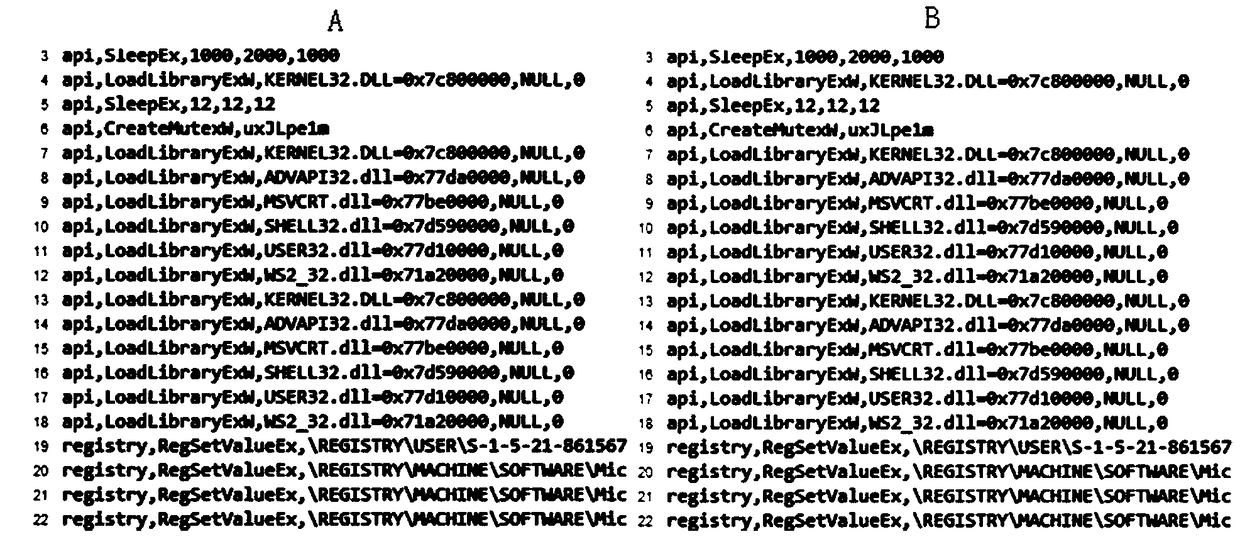
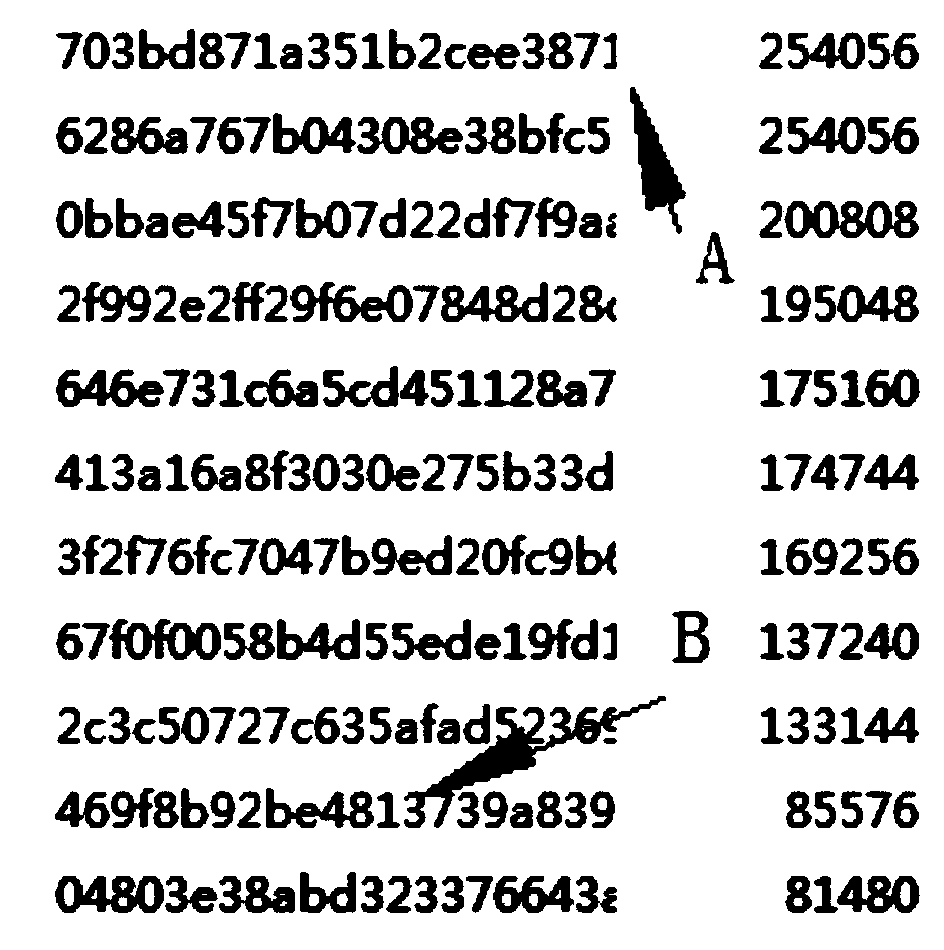
[0050] The inventors found that the existing clustering methods for malicious program samples include dynamic clustering and static clustering. However, no matter whether dynamic clustering or static clustering is performed on malicious program samples, the clustering results obtained are not accurate. For example, some behaviors of samples may not be triggered during dynamic clustering, resulting in incomplete collection of sample behaviors. At this time, the clustering results are not very accurate. If dynamic clustering and static clustering can be combined, t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com