Reading method and device for verification information
A technology for verifying information and verifying terminals, which is applied in the field of controlling application programs to read verification information, so as to prevent the theft of verification information and ensure information security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
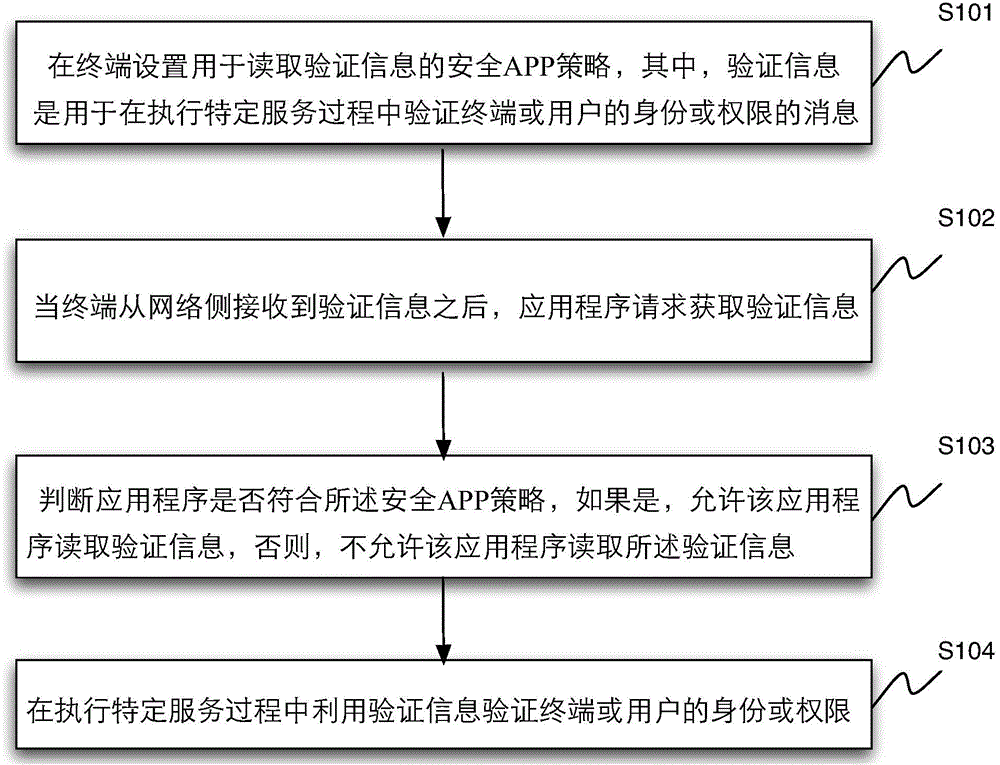
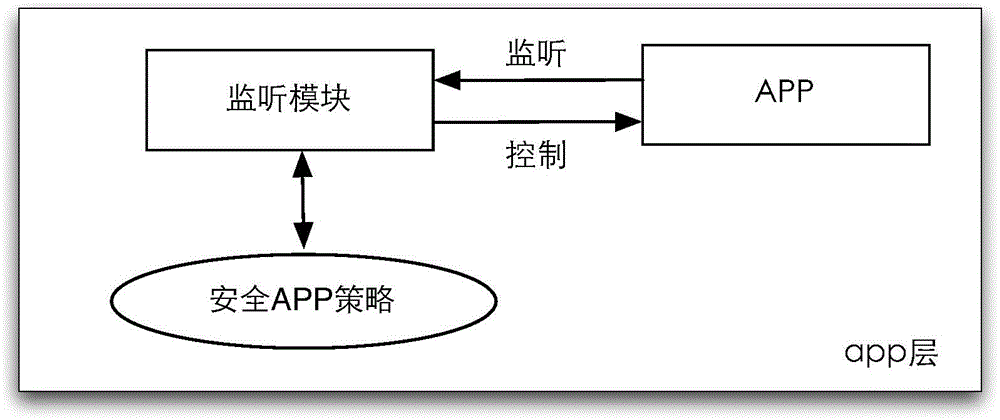
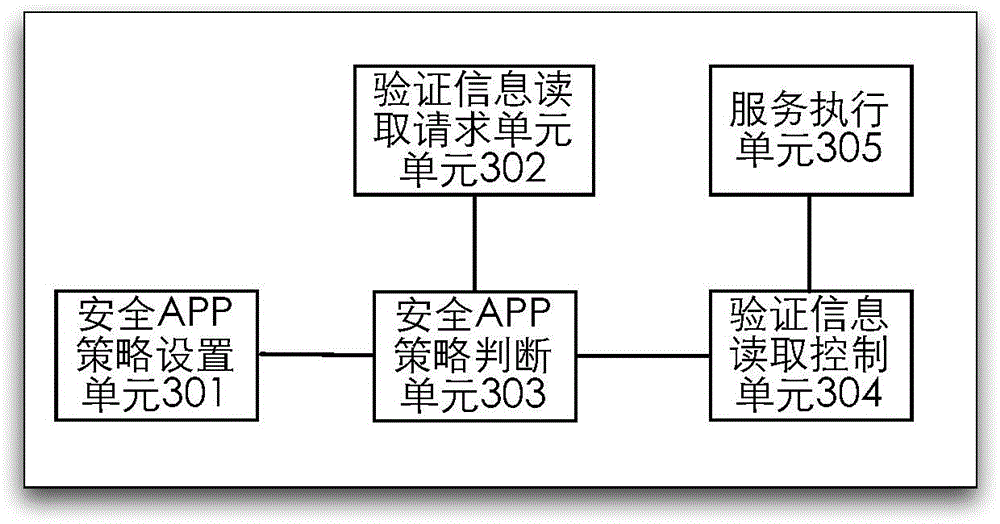
Method used
Image
Examples
Embodiment Construction
[0039] Exemplary embodiments of the present disclosure will be described in more detail below with reference to the accompanying drawings. Although exemplary embodiments of the present disclosure are shown in the drawings, it should be understood that the present disclosure may be embodied in various forms and should not be limited by the embodiments set forth herein. Rather, these embodiments are provided for more thorough understanding of the present disclosure and to fully convey the scope of the present disclosure to those skilled in the art.
[0040] As mentioned above, in the prior art, for example, adopting SMS to obtain verification information is the last security measure, but since malicious Trojans can read text messages, this last so-called safe mobile phone text message verification is not so safe. The core problem of this situation is that any application program (or called: software, APP) may directly read the verification code text message, so that when there i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More