Network device access control list management method and network device access control list management device
A technology for access control lists and network equipment, which is applied in data exchange networks, electrical digital data processing, special data processing applications, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
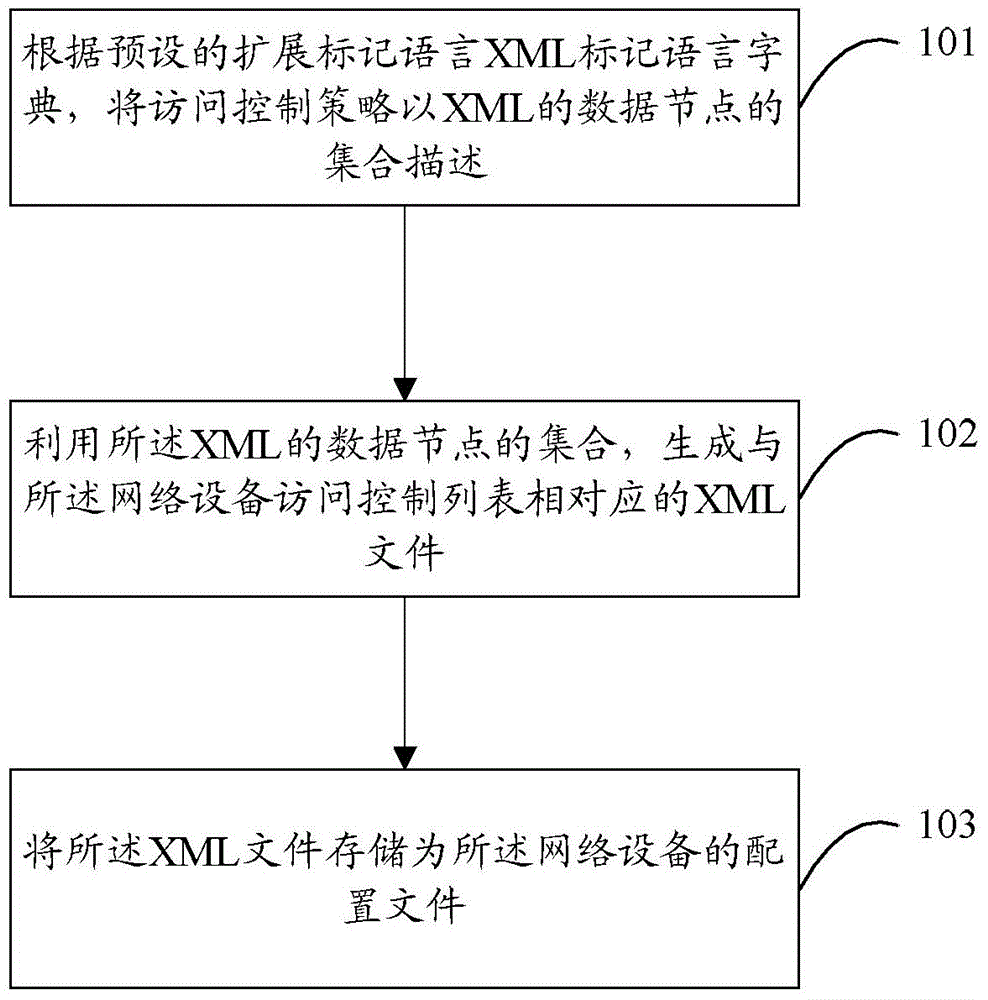
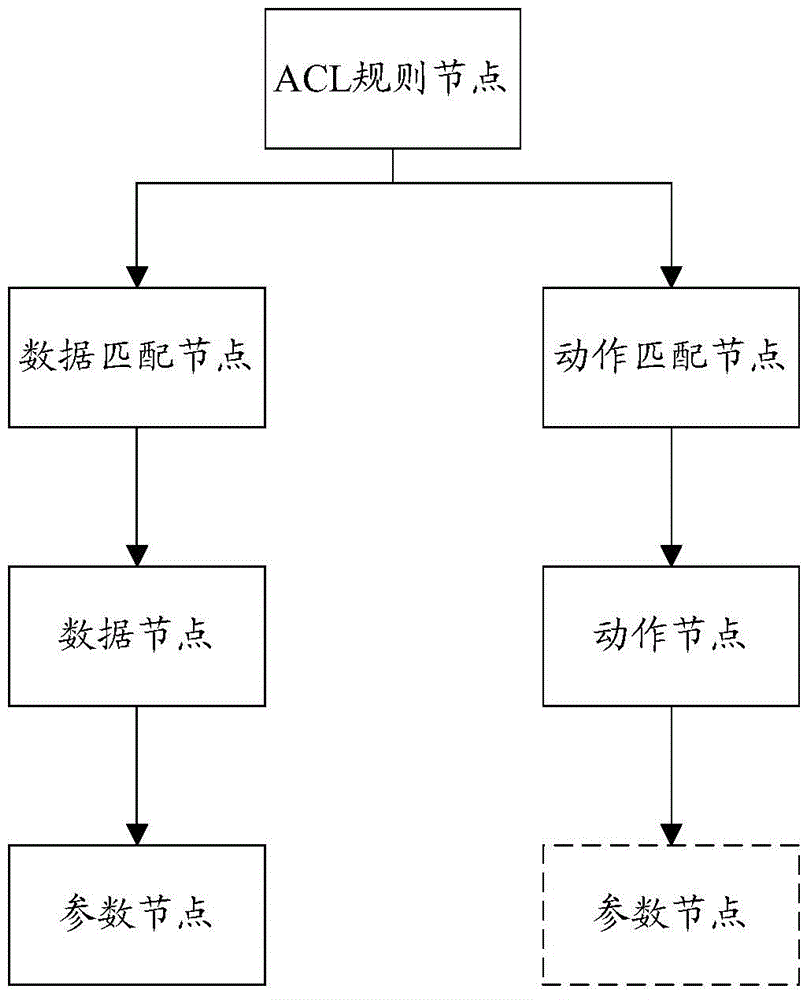
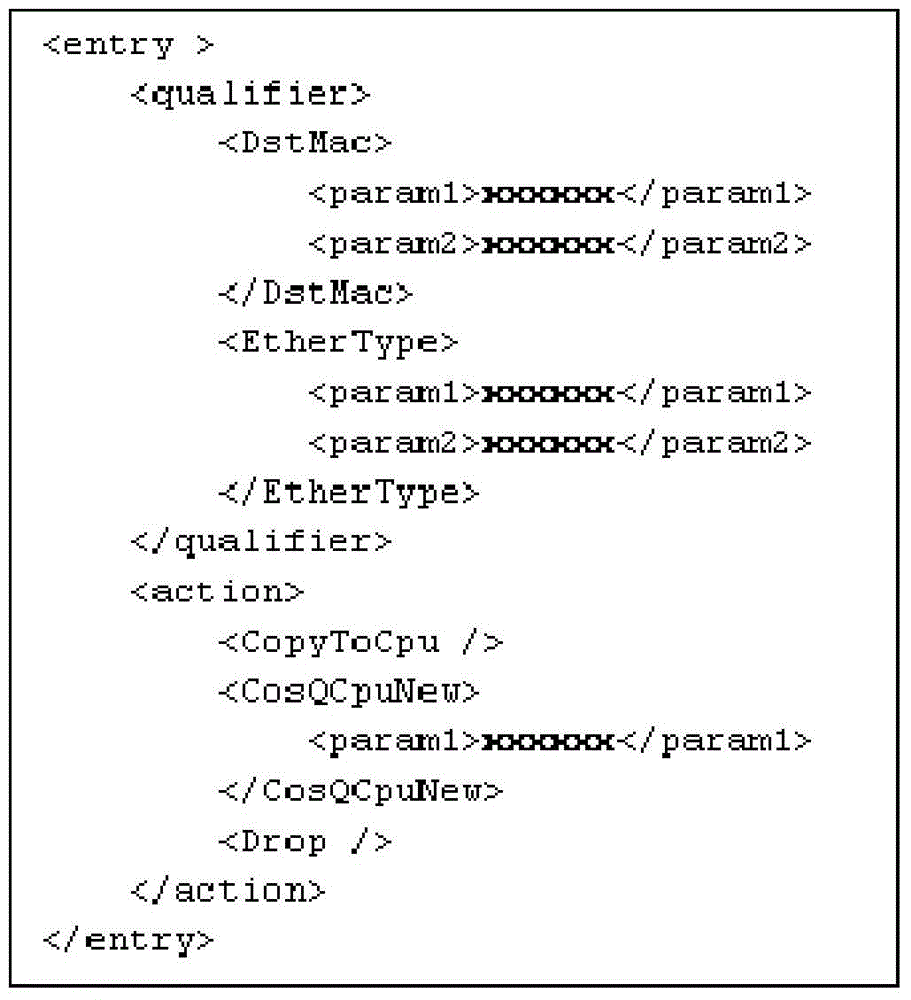
Method used
Image
Examples
Embodiment Construction
[0038] In order to illustrate the embodiments and technical solutions of the present invention more clearly, the technical solutions of the present invention will be described in more detail below in conjunction with the accompanying drawings and embodiments. Obviously, the described embodiments are part of the embodiments of the present invention, not all of them. Example. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without any creative effort fall within the protection scope of the present invention.
[0039] In this embodiment of the present invention, the access control policy of a network device refers to the set of access control rules of the device, including the access control rules of the network device that the developer of the network device wishes to implement through the internal ACL and the user of the network device that wishes to pass the user Access control rules for network devices ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More