Terminal authenticity verification method, apparatus and system
A verification method and terminal technology, applied in the Internet field
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0081] The following will clearly and completely describe the technical solutions in the embodiments of the application with reference to the drawings in the embodiments of the application. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
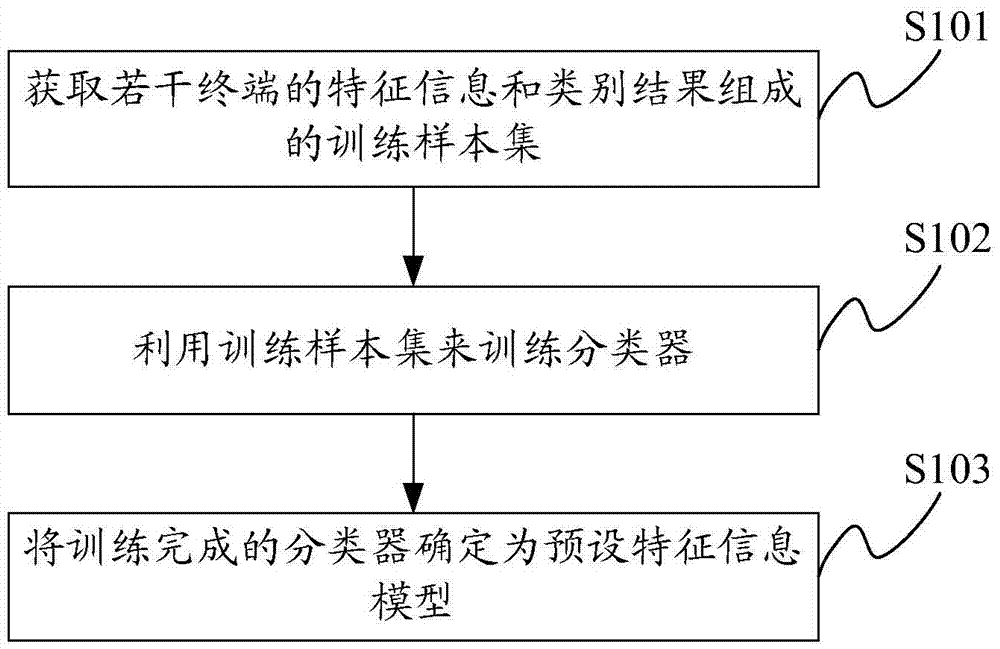
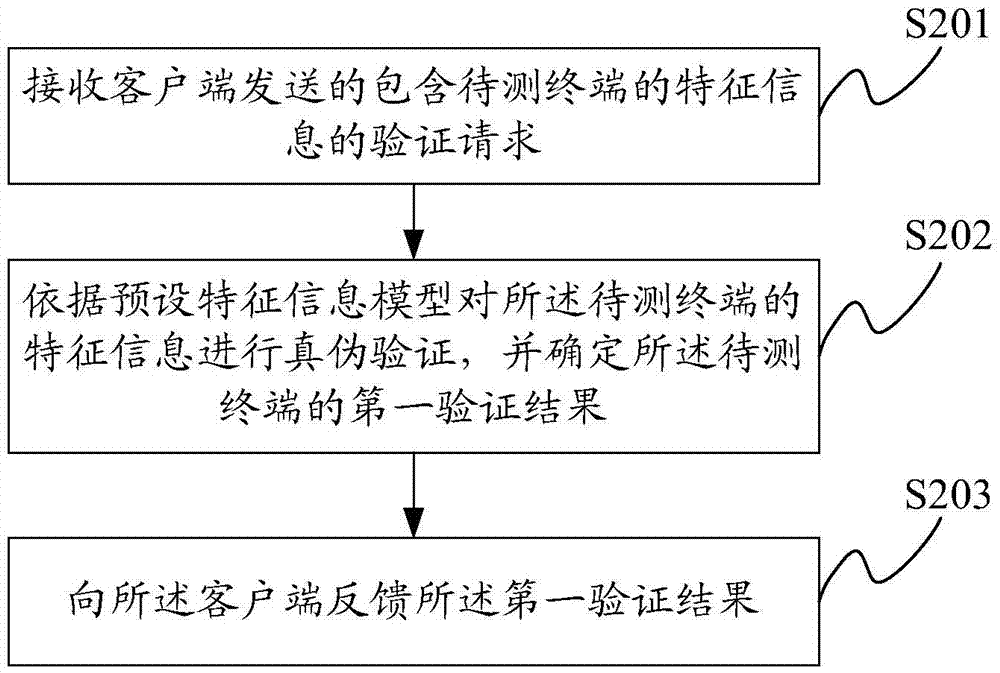
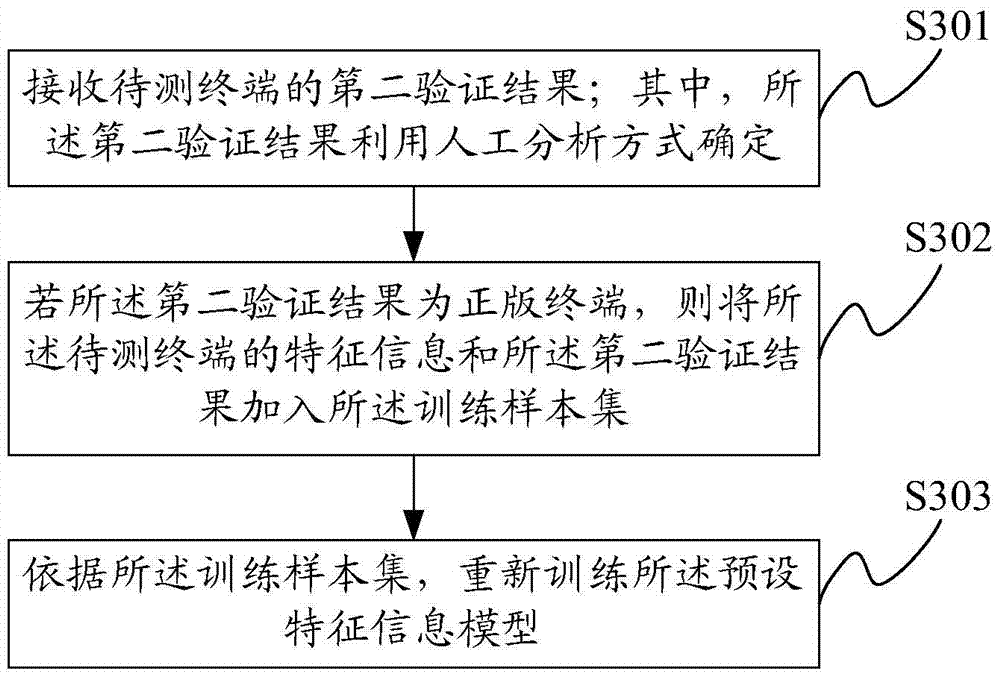
[0082] In order to accurately verify the authenticity of terminals for different batches of terminals, this application builds a preset feature information model on the server; where the preset feature information model is a training program based on the feature information and category results of several terminals. The classifier trained on the sample set is used to distinguish genuine terminals from pirated terminals based on feature information.
[0083] The following describes t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More