Method and system for access control of storage device
A storage device and access control technology, applied in the computer field to achieve the effect of access security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
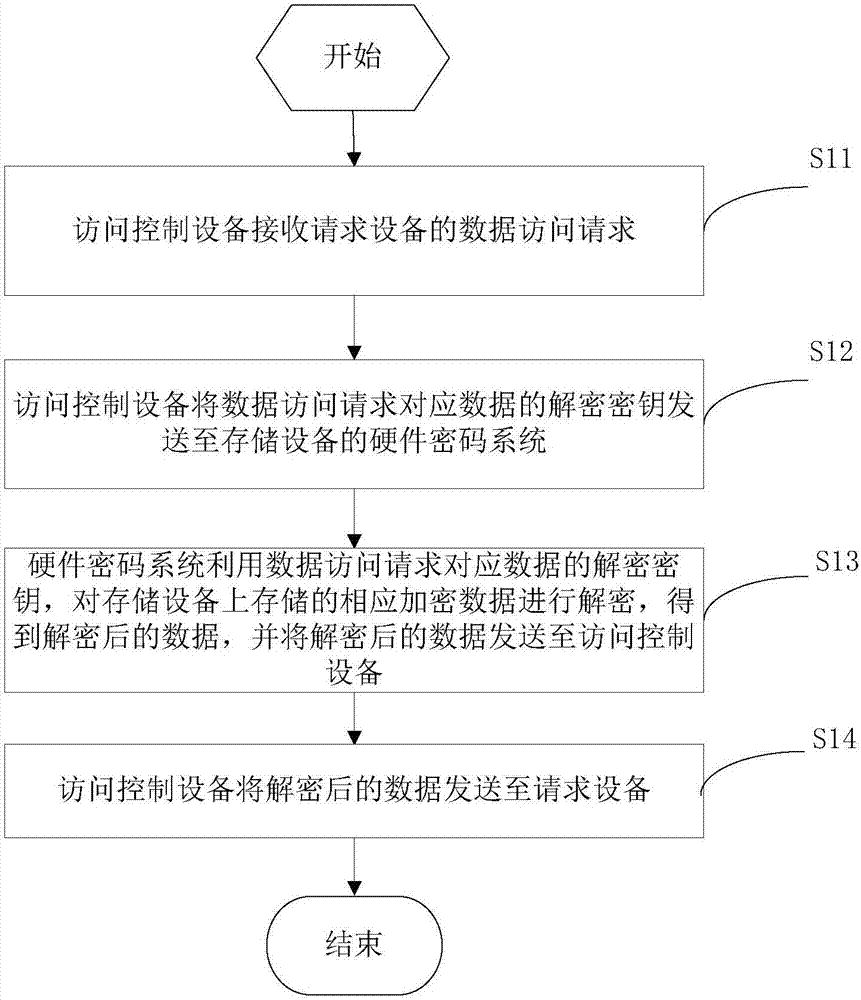
[0046] See figure 1 , which shows a flow chart of a storage device access control method provided by the present application, which may include the following steps:
[0047] Step S11: the access control device receives the data access request from the requesting device.
[0048] In this embodiment, the data access request includes information about the data to be accessed.
[0049] Step S12: the access control device sends the decryption key of the data corresponding to the data access request to the hardware cryptographic system of the storage device.
[0050] The access control device determines the decryption key of the data corresponding to the data access request according to the information of the data to be accessed in the data access request, and sends the decryption key to the hardware cryptosystem of the storage device. Wherein, the data corresponding to the data access request is the data to be accessed by the requesting device.
[0051] Step S13: The hardware cr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More