Intrusion detection methods, detection rule generation method, device and system
An intrusion detection and rule technology, applied in the field of network security, can solve the problem of inability to confirm the success of a specific type of file intrusion, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
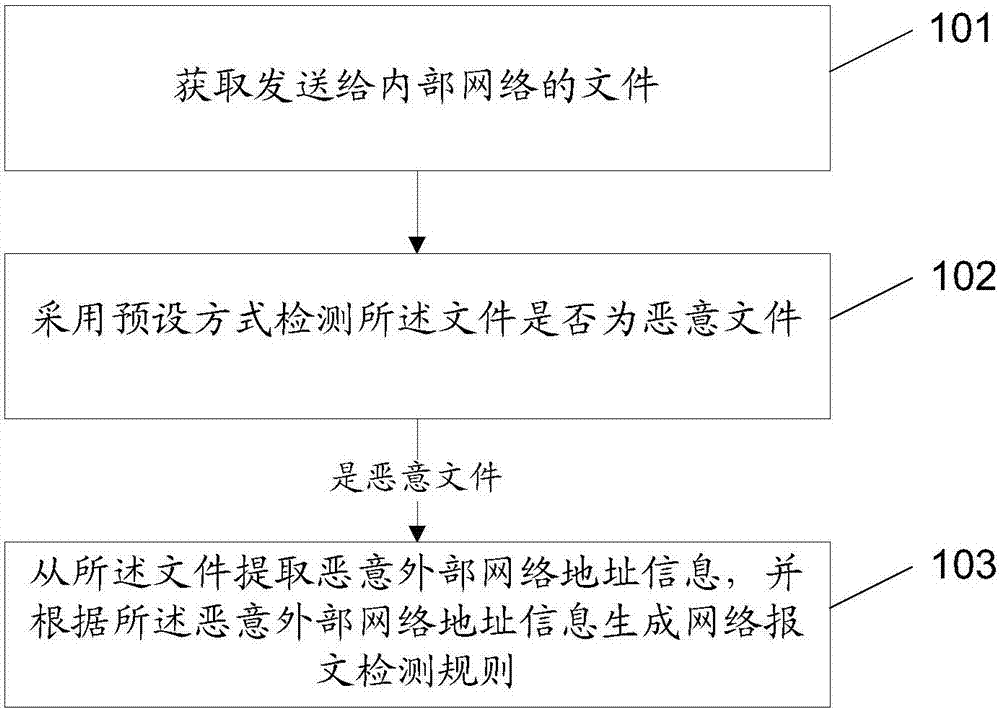
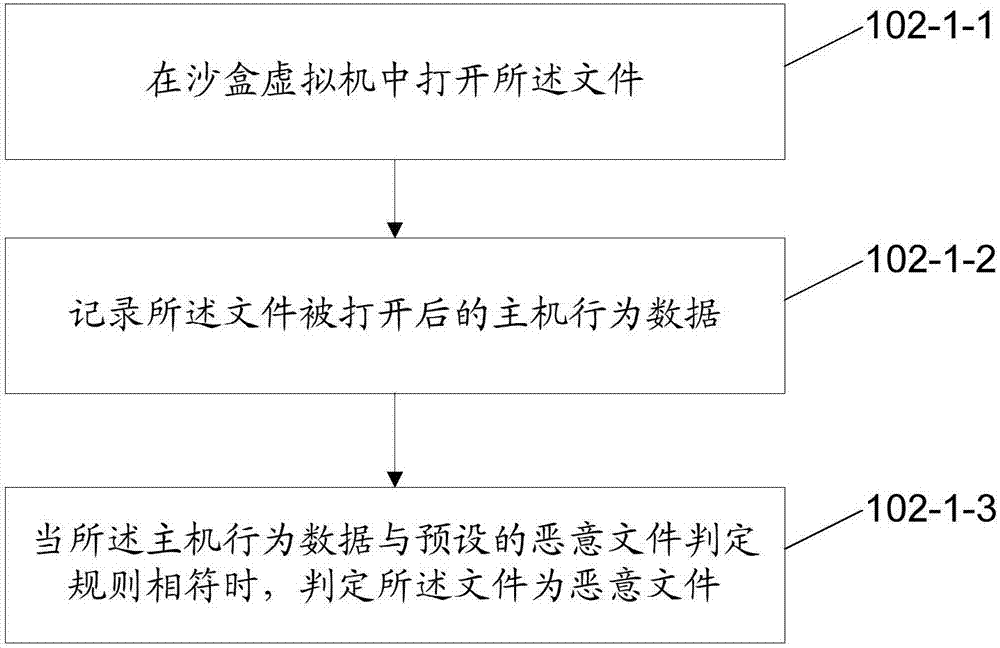
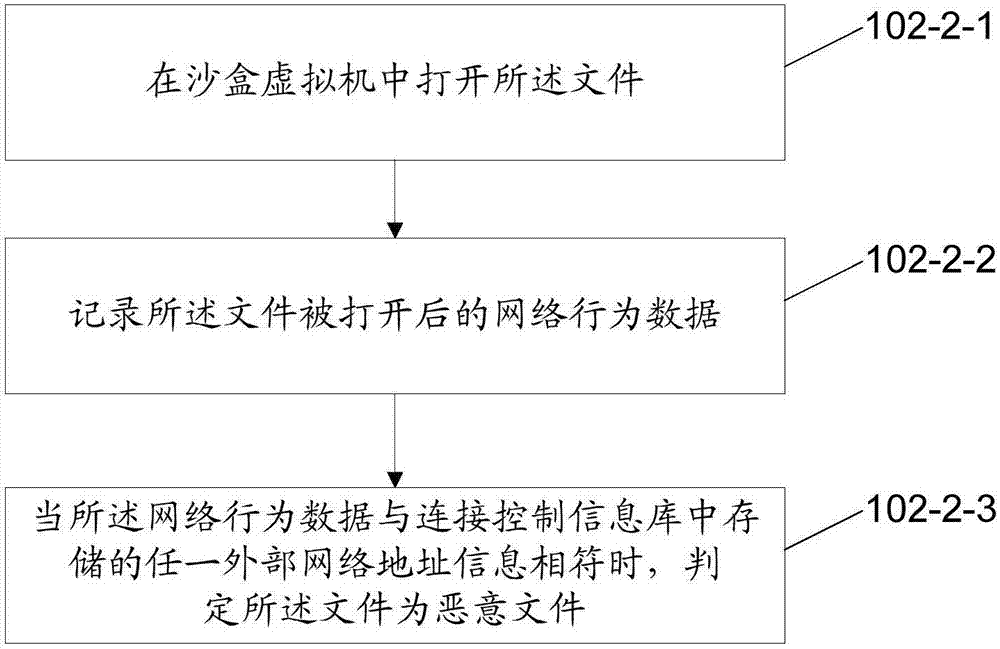
Method used
Image
Examples
Embodiment Construction
[0110] In the following description, numerous specific details are set forth in order to provide a thorough understanding of the application. However, the present application can be implemented in many other ways different from those described here, and those skilled in the art can make similar promotions without violating the connotation of the present application. Therefore, the present application is not limited by the specific implementations disclosed below.
[0111] In this application, an intrusion detection method and device, a detection rule generation method and device, an intrusion detection system, and another intrusion detection method are respectively provided. Each will be described in detail in the following examples. Before describing the embodiments, the technical solution of the present application will be briefly explained.
[0112] In the technical solution of this application, an internal network refers to an internal private network with a specific boun...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More